Setting Up RemoteIoT VPC SSH On Windows 10 For Enhanced Connectivity
Configuring RemoteIoT VPC SSH on Windows 10 without relying on third-party tools has become an essential solution for secure remote access. As the trend of remote work continues to grow, mastering the art of establishing secure connections has never been more critical. This comprehensive guide will walk you through the setup process step by step, ensuring you achieve a reliable and secure connection tailored to your needs.
RemoteIoT VPC SSH empowers users to securely access their virtual private cloud without the need for external applications. This method leverages the robust capabilities of Windows 10, offering a dependable and efficient connection without the added complexity of third-party software. By following this guide, you will gain the skills and knowledge to configure your system with ease and confidence.
Whether you're managing IoT devices remotely or accessing cloud-based resources, understanding RemoteIoT VPC SSH is vital for modern professionals. This article will delve into the nuances of basic configurations, advanced troubleshooting techniques, and performance optimization strategies, equipping you with the tools to succeed in a remote work environment.
Read also:What Does Obsidian Kingdom Mean Unveiling The Mysteries Of The Name
Table of Contents
- Understanding RemoteIoT VPC SSH
- Key Advantages of RemoteIoT VPC SSH
- Comprehensive Setup Guide
- Strengthening Security Protocols
- Addressing Common Challenges
- Optimizing Connection Performance
- Evaluating Built-In vs. Third-Party Tools
- Exploring Practical Use Cases
- Emerging Trends in RemoteIoT VPC SSH
- Final Thoughts and Next Steps
Understanding RemoteIoT VPC SSH
RemoteIoT VPC SSH represents a secure connection established between a local machine and a virtual private cloud (VPC) using the Secure Shell (SSH) protocol. This approach is invaluable for managing IoT devices and cloud resources remotely. By utilizing the integrated SSH capabilities of Windows 10, users can achieve a secure and efficient connection without depending on third-party software solutions.
The SSH protocol provides a robust framework for encrypted communication, ensuring the integrity and confidentiality of your data. As remote work continues to gain traction, understanding how to configure RemoteIoT VPC SSH on Windows 10 is essential for maintaining secure and efficient remote operations. This section will explore the foundational principles of SSH and its pivotal role in modern remote connectivity.
Key Advantages of RemoteIoT VPC SSH
Adopting RemoteIoT VPC SSH on Windows 10 offers numerous benefits, including enhanced security, cost efficiency, and streamlined workflows. By eliminating the reliance on third-party tools, users can reduce overhead costs while maintaining a high level of security. Below are some of the standout advantages:
- Security: SSH encrypts all communication between your local machine and the VPC, safeguarding sensitive data from unauthorized access.
- Cost-Effectiveness: Utilizing the built-in features of Windows 10 eliminates the need for additional software purchases, saving both time and money.
- Efficiency: A streamlined setup and configuration process minimizes the time and effort required to establish a secure connection.
- Compatibility: This method seamlessly integrates with a wide array of IoT devices and cloud platforms, ensuring broad applicability across various use cases.
Comprehensive Setup Guide
Essential Requirements for Setup
Before proceeding with the configuration process, ensure that your system meets the following prerequisites:
- Windows 10 version 1809 or later installed on your machine.
- Administrative privileges to enable necessary features and make system-level changes.
- Access to the VPC or cloud platform you intend to connect to, along with the required credentials.
- A foundational understanding of SSH and networking concepts to facilitate a smooth setup process.
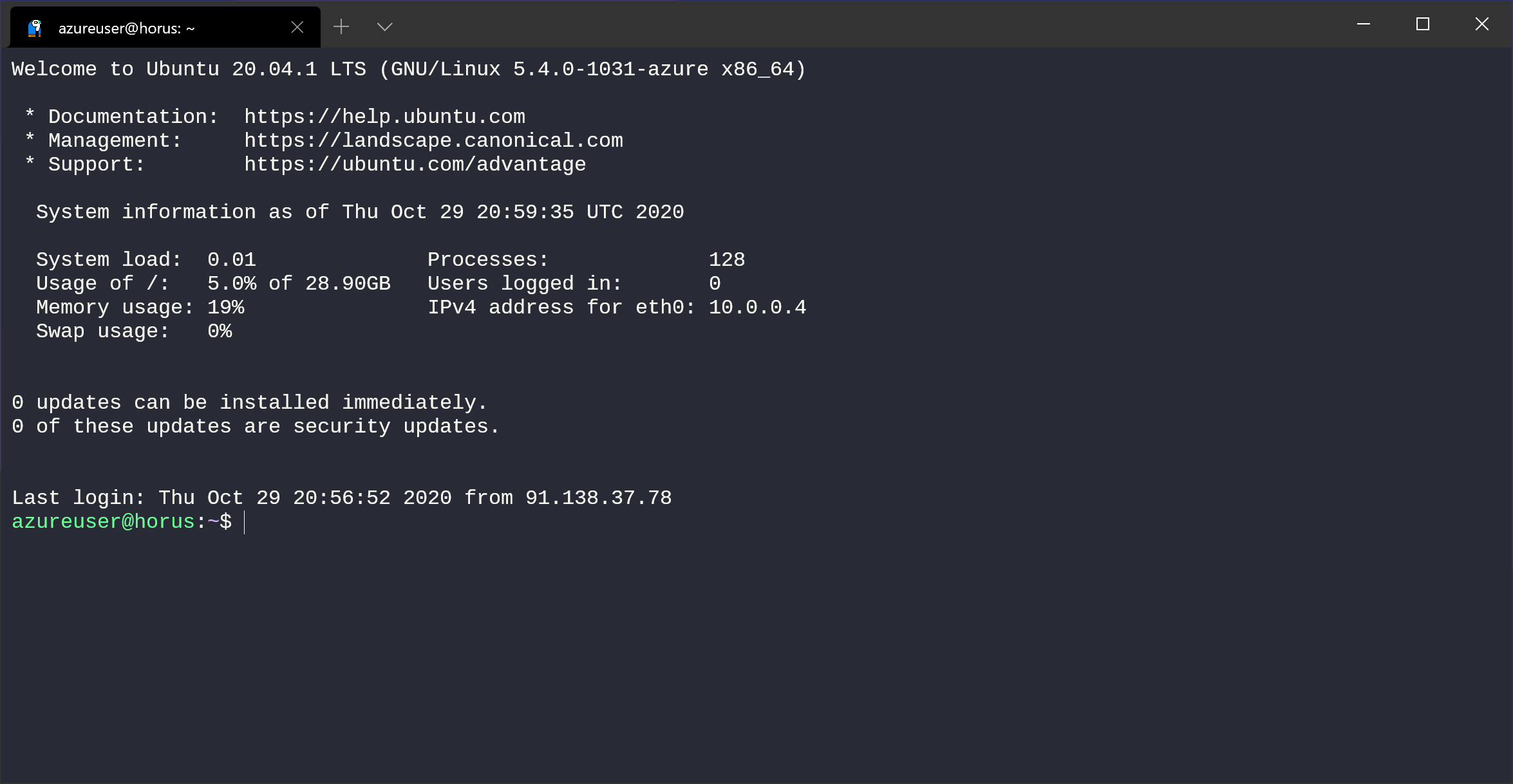
Configuring Windows 10 for SSH
Configuring Windows 10 for SSH involves enabling the OpenSSH client and server features. Follow these detailed steps to successfully set up your system:
- Access the Start menu and search for "Turn Windows features on or off" to open the Windows Features dialog box.
- Locate and check the boxes for both "OpenSSH Client" and "OpenSSH Server" to enable these essential components.
- Click "OK" to apply the changes and restart your computer if prompted to ensure the new features take effect.
- After restarting, verify that the SSH service is operational by opening a command prompt and typing `ssh`. If the command is recognized, the setup was successful.
Strengthening Security Protocols
While SSH inherently provides a secure connection, implementing additional security measures can further fortify your system against potential threats. Consider adopting the following best practices:
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
- Use Strong Passwords: Ensure all user accounts are protected with strong, unique passwords to prevent unauthorized access.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring two-factor authentication for SSH access, significantly reducing the risk of unauthorized logins.
- Restrict Access: Limit SSH access to specific IP addresses or subnets to minimize exposure and protect against unauthorized connections.
- Regularly Update Software: Keep your operating system and SSH software up to date to safeguard against emerging vulnerabilities and ensure optimal performance.
Addressing Common Challenges
Despite meticulous configuration, issues may occasionally arise during the setup process. Below are some common problems and their corresponding solutions:
- Connection Refused: Verify that the SSH service is running and that your firewall rules allow SSH traffic to pass through without restriction.
- Authentication Failed: Carefully review your username and password, ensuring they are accurate. Additionally, confirm that the correct SSH keys are being used for authentication.
- Timeout Errors: Examine your network connection for stability and ensure there are no routing issues preventing successful communication between your local machine and the VPC.
Optimizing Connection Performance
Maximizing the performance of your RemoteIoT VPC SSH connection can significantly enhance productivity and user satisfaction. Consider implementing the following strategies:
- Compress Data: Enable data compression in your SSH client to reduce transfer times and improve overall efficiency during file transfers.
- Limit Bandwidth Usage: Configure bandwidth limits to prevent network congestion and ensure a stable connection, especially in environments with limited bandwidth.
- Monitor Resource Usage: Regularly monitor system resources to identify and address any potential bottlenecks that may impact connection performance.
Evaluating Built-In vs. Third-Party Tools
While third-party tools often offer advanced features, leveraging the built-in capabilities of Windows 10 for RemoteIoT VPC SSH provides numerous advantages. Below is a comparative analysis:
| Feature | Built-In SSH | Third-Party Tools |
|---|---|---|
| Cost | Free of charge, making it an economical choice for users seeking budget-friendly solutions. | Paid or freemium models, which may involve recurring costs or feature limitations in free versions. |
| Security | Highly secure, as it relies on trusted and regularly updated Windows components. | Dependent on the vendor's commitment to security updates and quality assurance. |
| Compatibility | Universal compatibility with a wide range of systems and devices, ensuring seamless integration. | Compatibility may vary depending on the specific third-party tool and its supported platforms. |
Exploring Practical Use Cases
RemoteIoT VPC SSH on Windows 10 is a versatile solution applicable to various real-world scenarios. Below are some practical use cases that highlight its potential:
- Remote Device Management: Administrators can securely manage IoT devices from any location, streamlining operations and reducing the need for physical presence.
- Cloud Resource Access: Developers can access cloud-based resources with confidence, knowing their connection is secure and their data is protected.
- Data Transfer: Securely transfer files between systems using SCP or SFTP, ensuring sensitive information remains encrypted during transit.
Emerging Trends in RemoteIoT VPC SSH
As technology continues to evolve, the future of RemoteIoT VPC SSH holds exciting possibilities. Emerging trends include:
- Quantum-Safe Encryption: The development of encryption methods resistant to quantum computing attacks ensures long-term data security in an era of advancing computational power.
- AI-Powered Security: Incorporating artificial intelligence into security protocols enables real-time threat detection and mitigation, enhancing overall system resilience.
- Zero-Trust Architecture: Implementing strict access controls based on the zero-trust model significantly enhances security in remote environments, reducing the risk of unauthorized access.
Final Thoughts and Next Steps
In conclusion, setting up RemoteIoT VPC SSH on Windows 10 without relying on third-party tools is a practical, secure, and cost-effective solution for remote connectivity. By following the comprehensive steps outlined in this guide, you can achieve a reliable setup while maintaining robust security measures. We invite you to share your experiences and insights in the comments section below and encourage you to explore additional resources on our site to expand your knowledge of remote work solutions and cybersecurity best practices.
Thank you for reading, and we hope this guide serves as a valuable resource in your journey toward secure and efficient remote connectivity.