Setting Up Secure IoT P2P Connections On Raspberry Pi For Mac Users
As technology continues to advance, the demand for secure remote connections in IoT ecosystems has grown exponentially. Whether you're a developer, hobbyist, or enterprise user, establishing a secure connection for remote IoT devices through peer-to-peer (P2P) networks using platforms like Raspberry Pi has become essential. This article will guide you through setting up a secure and efficient IoT P2P connection on Raspberry Pi, ensuring compatibility with Mac devices while keeping costs low.
In today's interconnected world, IoT devices have revolutionized industries, homes, and daily life. However, ensuring these devices remain secure while maintaining seamless connectivity is a significant challenge. This is where P2P technology shines, offering a robust solution for remote device management without the need for centralized servers. This guide will provide a comprehensive walkthrough, covering software downloads, configuration steps, troubleshooting tips, and more, equipping you with the knowledge to establish a secure remote connection on your Mac for free.
Table of Contents
- Understanding IoT P2P Connections
- Exploring Raspberry Pi
- Advantages of Secure IoT P2P Connections
- Step-by-Step Setup for Raspberry Pi
- Ensuring Compatibility with Mac
- Implementing Security Best Practices
- Addressing Common Issues
- Optimizing Network Performance
- Achieving Cost-Effective Solutions
- Final Thoughts and Next Steps
Understanding IoT P2P Connections
IoT P2P (Peer-to-Peer) connections allow devices to communicate directly without relying on a central server or intermediary. This approach offers numerous advantages, including reduced latency, lower bandwidth usage, and enhanced security. When applied to Raspberry Pi, this technology empowers users to create secure and efficient networks for managing remote devices effectively.
Read also:What Is The Jamaican Slang For Friend Or Bro Exploring The Vibrant Language Of Jamaica
With the proliferation of IoT devices, ensuring secure connections has become paramount. P2P technology addresses common vulnerabilities by encrypting data exchanges and minimizing reliance on third-party servers. By utilizing Raspberry Pi, users can implement this solution in a cost-effective and scalable manner. Whether you're setting up a home automation system or managing industrial IoT devices, understanding how to securely connect remote IoT P2P Raspberry Pi is crucial. This guide will provide a step-by-step process to ensure your setup is both secure and compatible with Mac devices.
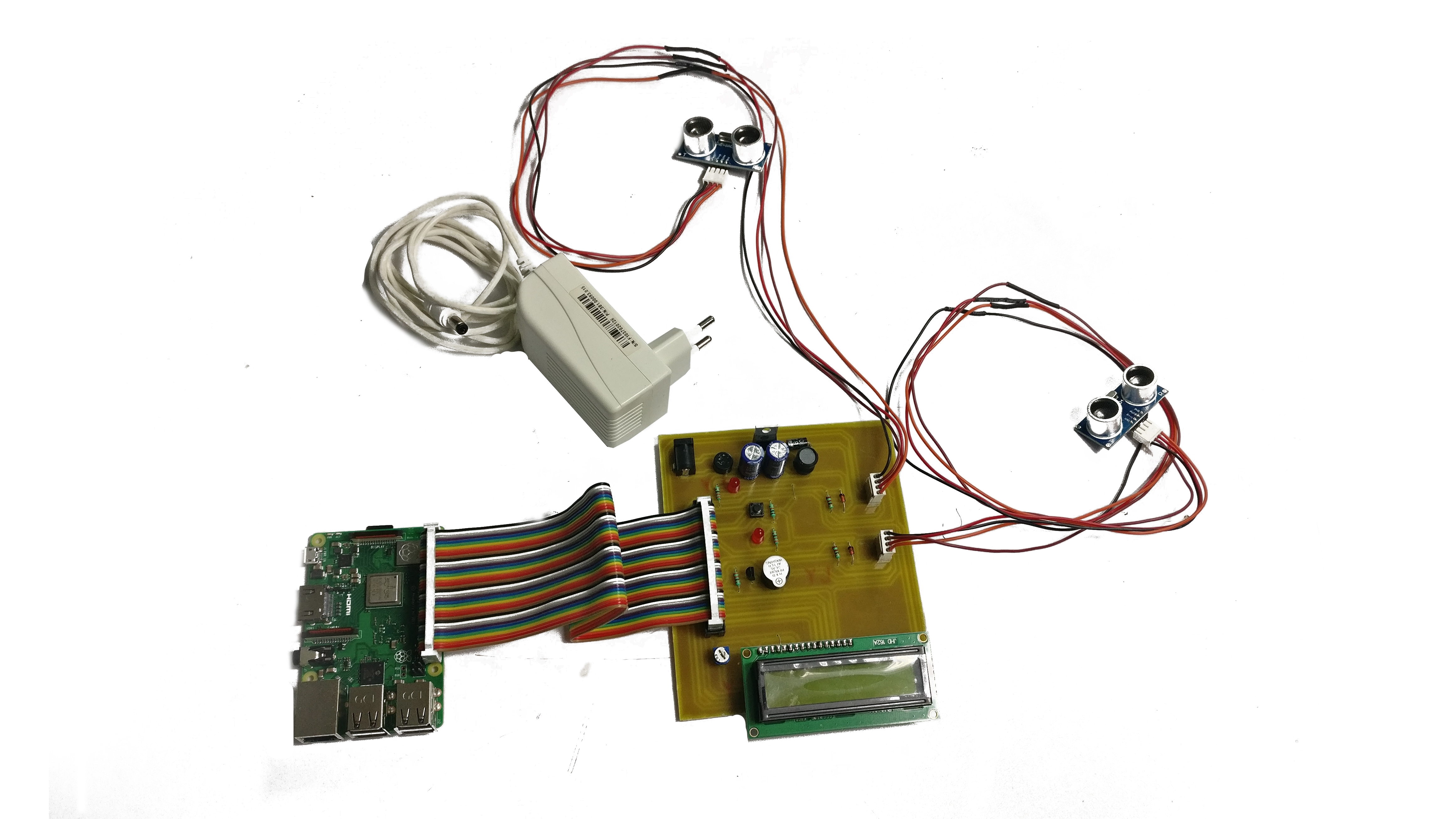
Exploring Raspberry Pi
Raspberry Pi has emerged as a cornerstone in the IoT development landscape, thanks to its affordability, versatility, and open-source nature. This single-board computer boasts features that make it ideal for implementing secure IoT P2P connections, including:
- A compact design with low power consumption, making it perfect for portable and energy-efficient projects.
- Support for multiple operating systems, such as Raspbian, Ubuntu, and others, offering flexibility in software environments.
- Compatibility with a wide array of sensors, actuators, and peripherals, enabling seamless integration with various IoT devices.
- Strong community support and extensive documentation, ensuring users have access to valuable resources and guidance.
For Mac users, Raspberry Pi offers seamless integration through various tools and software, making it an excellent choice for those seeking to establish secure IoT P2P connections without incurring additional costs.
Advantages of Secure IoT P2P Connections
Implementing a secure IoT P2P connection on Raspberry Pi provides numerous benefits, including:
- Enhanced Security: By encrypting data exchanges and minimizing reliance on centralized servers, P2P technology significantly reduces the risk of unauthorized access and data breaches.
- Improved Performance: Direct device-to-device communication eliminates bottlenecks associated with server-based architectures, resulting in faster and more reliable connections.
- Cost Efficiency: Leveraging open-source software and hardware like Raspberry Pi allows users to set up secure IoT networks without significant financial investment.
- Scalability: P2P networks can easily accommodate additional devices, making them suitable for both small-scale projects and large-scale deployments.
These advantages make secure IoT P2P connections an attractive option for developers, hobbyists, and enterprises alike.
Step-by-Step Setup for Raspberry Pi
Downloading Essential Software
Before setting up a secure IoT P2P connection on Raspberry Pi, you'll need to download the necessary software. Follow this step-by-step guide:
Read also:Exploring Elon Musks Partners And Kids A Comprehensive Look
- Visit the official Raspberry Pi website (https://www.raspberrypi.org/) to download the latest version of Raspberry Pi OS.
- Install Balena Etcher or a similar tool to flash the operating system image onto an SD card.
- Download any additional software packages you may need, such as P2P libraries or encryption tools.
Ensure that all software is compatible with your Mac and Raspberry Pi model to avoid potential compatibility issues.
Configuring the System
Once you've downloaded the necessary software, follow these steps to configure your Raspberry Pi for secure IoT P2P connections:
- Insert the SD card into your Raspberry Pi and power it on.
- Connect to your local network via Wi-Fi or Ethernet to establish an initial connection.
- Install and configure P2P software, ensuring proper encryption and authentication settings to secure your network.
- Test the connection by pairing your Raspberry Pi with another device in the network to verify functionality.
For additional guidance and troubleshooting tips, refer to the official Raspberry Pi documentation and community forums.
Ensuring Compatibility with Mac
Integrating Raspberry Pi with Mac devices is straightforward, thanks to its cross-platform compatibility. To ensure seamless integration, consider the following recommendations:
- Use SSH (Secure Shell) to remotely access and manage your Raspberry Pi directly from your Mac.
- Install VNC Viewer or a similar tool to enable graphical remote access for more intuitive control.
- Ensure all software and libraries are compatible with macOS to avoid compatibility issues during setup.
By following these steps, you can establish a secure and efficient IoT P2P connection between your Raspberry Pi and Mac devices, enhancing your project's functionality and usability.
Implementing Security Best Practices
Ensuring the security of your IoT P2P network is critical. To protect your network, adhere to the following best practices:
- Use strong encryption protocols, such as AES-256, to safeguard data exchanges and prevent unauthorized access.
- Implement multi-factor authentication (MFA) to add an extra layer of security and protect against unauthorized access attempts.
- Regularly update your software and firmware to address potential vulnerabilities and maintain optimal security levels.
- Monitor network activity continuously for signs of unauthorized access or suspicious behavior, allowing you to respond promptly to any threats.
By following these guidelines, you can significantly enhance the security of your IoT P2P network and ensure its long-term integrity.
Addressing Common Issues
Encountering issues during setup is common, but most problems can be resolved by following these troubleshooting tips:
- Check network settings to ensure proper connectivity and resolve any connection-related issues.
- Verify software installations and configurations for accuracy to avoid compatibility or functionality problems.
- Consult the official Raspberry Pi documentation and community forums for additional support and troubleshooting advice.
If problems persist despite these efforts, consider reaching out to professional support services for further assistance.
Optimizing Network Performance
To maximize the performance of your IoT P2P network, consider implementing the following techniques:
- Minimize data exchanges by compressing data packets, reducing the bandwidth required for communication.
- Utilize caching mechanisms to reduce redundant data transfers, enhancing efficiency and reducing network load.
- Regularly monitor network performance and adjust settings as needed to maintain optimal functionality and reliability.
By applying these techniques, you can significantly improve the efficiency and reliability of your IoT P2P connections, ensuring a smoother and more effective user experience.
Achieving Cost-Effective Solutions
Setting up a secure IoT P2P connection on Raspberry Pi can be achieved without incurring significant costs. By leveraging open-source software and hardware, users can establish robust networks while keeping expenses to a minimum. Additionally, the extensive support available through the Raspberry Pi community ensures that users have access to the resources they need to succeed, making it an ideal solution for budget-conscious projects.
Final Thoughts and Next Steps
In conclusion, securely connecting remote IoT P2P Raspberry Pi devices is a critical component of modern technology ecosystems. By following the steps outlined in this guide, you can establish a secure, efficient, and cost-effective network that integrates seamlessly with Mac devices. Remember to adhere to best practices for security and performance optimization to ensure the long-term success of your IoT P2P setup.
We encourage you to share your experiences and insights in the comments below. Additionally, consider exploring related articles on our website for further guidance and inspiration. Together, we can build a safer and more connected future for all.