Securing Remote IoT Connections Via P2P Networks On Windows 10
In our increasingly interconnected world, establishing secure connections for remote IoT devices through peer-to-peer (P2P) networks has become essential for both businesses and individuals. With the rapid expansion of the Internet of Things (IoT), safeguarding sensitive information during data transmission is more critical than ever. This comprehensive guide will walk you through the process of creating a secure, efficient P2P network on Windows 10, helping you mitigate risks and optimize performance.
As technology continues to evolve at a rapid pace, the demand for seamless remote connectivity is growing exponentially. Whether you're managing smart home devices or monitoring industrial equipment, secure connections are indispensable. However, with the rise in cyber threats, it's crucial to adopt the right protocols and tools to ensure your network remains protected. This article will provide you with the knowledge and tools needed to secure your IoT devices effectively.
By the end of this article, you'll gain a thorough understanding of how to securely connect remote IoT devices via P2P networks on Windows 10. We'll delve into topics such as encryption methods, firewall configurations, and best practices for maintaining a secure network environment. Let’s get started!
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
Table of Contents
- Understanding IoT and Its Importance
- Basics of Secure Connections
- What is P2P Networking?
- Setting Up P2P on Windows 10
- Encryption Methods for Secure Connections
- Firewall Configuration for IoT Devices
- Best Practices for Secure IoT Connections
- Troubleshooting Common Issues
- Additional Security Tips
- Future Trends in IoT Security
Exploring IoT and Its Critical Role
The Internet of Things (IoT) refers to a vast network of physical devices equipped with sensors, software, and connectivity capabilities that enable them to collect and exchange data. These devices span a wide range, from everyday smart home appliances to complex industrial machinery. The significance of IoT lies in its ability to enhance operational efficiency, reduce costs, and provide valuable insights for better decision-making processes.
Applications of IoT Across Various Sectors
IoT has transformed numerous industries, offering innovative solutions that were once unimaginable. Here are some examples:
- Healthcare: Remote patient monitoring systems and wearable health devices that provide real-time data to healthcare providers.
- Manufacturing: Predictive maintenance tools and real-time production tracking systems that improve efficiency and reduce downtime.
- Agriculture: Smart farming techniques utilizing soil sensors, drones, and automated irrigation systems to optimize crop yields.
Despite the numerous benefits, the increasing number of connected devices also presents a growing risk of cyberattacks. Ensuring secure connections is vital to protect sensitive data and maintain operational integrity across all sectors.
Foundations of Secure Connections
Establishing a secure connection involves multiple components, including authentication, encryption, and robust network protocols. These elements work in harmony to safeguard data during transmission and prevent unauthorized access. For remote IoT devices, secure connections are particularly crucial, as they help mitigate the risks associated with data interception and tampering.
Key Components of Secure Connections
- Authentication: A process that verifies the identity of users and devices, ensuring only authorized entities can access the network.
- Encryption: The process of encoding data to make it unreadable to unauthorized parties, safeguarding sensitive information during transmission.
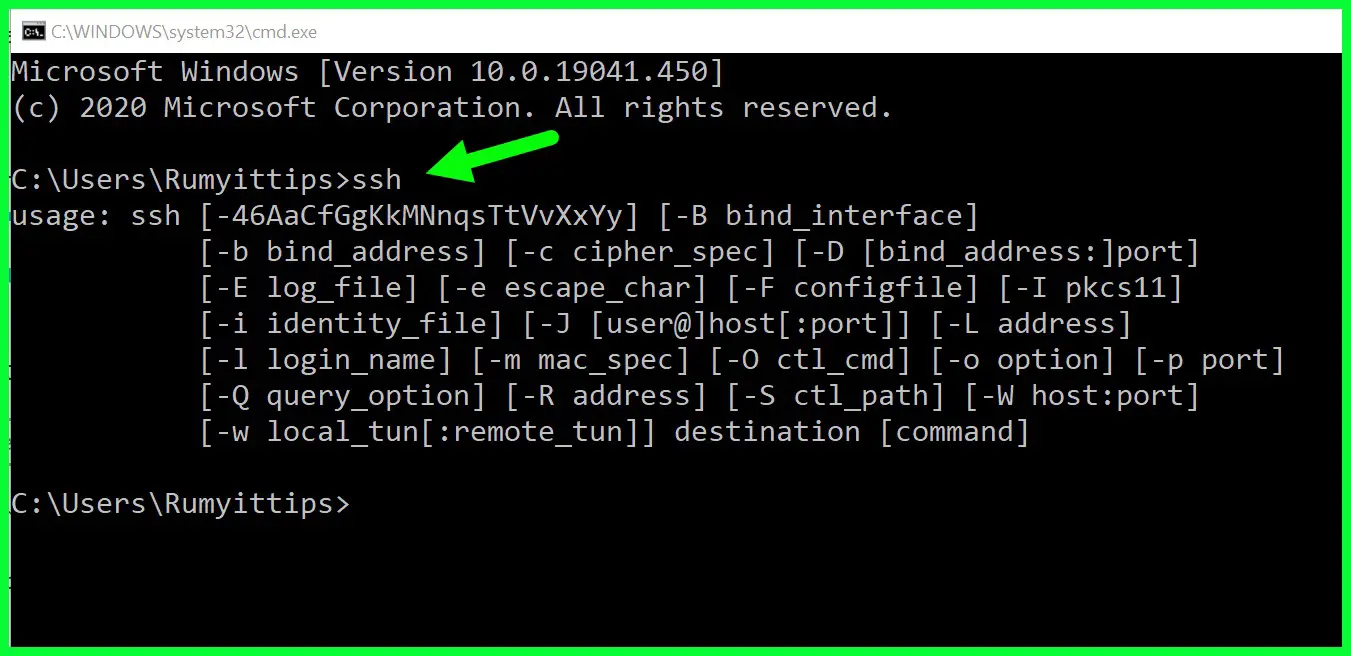
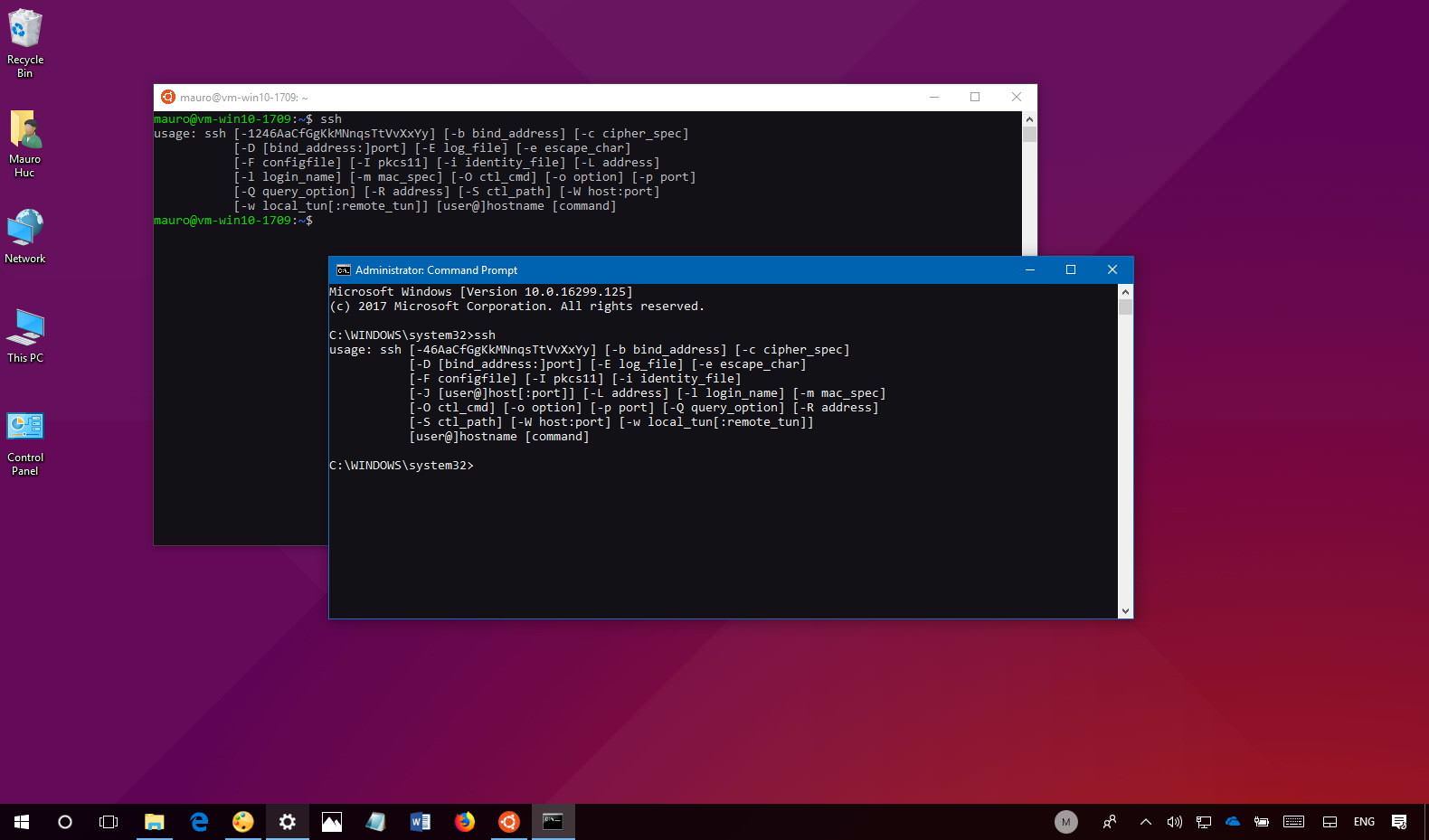
- Protocols: Secure communication standards such as HTTPS and SSH that ensure data is transmitted safely and efficiently.
Without proper security measures, remote IoT devices are vulnerable to various cyber threats, including data breaches and unauthorized access. Understanding these components is essential for creating a secure network environment.
An Introduction to P2P Networking
Peer-to-peer (P2P) networking allows devices to communicate directly with one another without relying on a central server. This decentralized approach offers several advantages, including improved efficiency, reduced latency, and enhanced scalability. However, it also introduces unique security challenges that must be addressed to ensure the network remains secure.
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
Benefits of P2P Networking
- Improved Performance: Direct communication between devices eliminates the need for a central server, reducing delays and improving overall efficiency.
- Reduced Dependency: By eliminating reliance on centralized servers, P2P networks can function more independently, enhancing resilience.
- Enhanced Scalability: P2P networks are highly scalable, making them ideal for large-scale deployments where numerous devices need to communicate seamlessly.
When implementing P2P networking for IoT devices, it's essential to incorporate robust security measures to protect against potential threats such as man-in-the-middle attacks and unauthorized access. This ensures the network remains secure and reliable.
Configuring P2P on Windows 10
Setting up a P2P connection on Windows 10 involves a series of straightforward steps, including enabling necessary features and installing the appropriate software. Follow these guidelines to establish a secure P2P connection:
Steps to Configure P2P on Windows 10
- Enable File and Printer Sharing: Navigate to Control Panel > Network and Sharing Center > Change advanced sharing settings. Enable file and printer sharing to allow devices to communicate directly.
- Install P2P Software: Download and install reliable P2P software, such as uTorrent or qBittorrent, to facilitate direct communication between devices.
- Configure Firewall Settings: Adjust your Windows Firewall settings to allow P2P applications, ensuring they can function without interference from security protocols.
By following these steps, you can establish a secure P2P connection on Windows 10. Regularly updating your software and security settings is essential to protect against emerging threats and maintain optimal performance.
Essential Encryption Methods for Secure Connections
Encryption is a cornerstone of data security, playing a critical role in protecting information transmitted between IoT devices. Several encryption methods are available, each offering unique advantages and limitations. Understanding these methods can help you select the most appropriate option for your specific needs.
Common Encryption Methods
- SSL/TLS: Secure Socket Layer/Transport Layer Security is widely used to encrypt web traffic, ensuring data remains secure during transmission.
- AES: Advanced Encryption Standard is a robust encryption protocol used to secure both data at rest and in transit, with AES-256 being one of the strongest options available.
- SSH: Secure Shell is a protocol that secures remote connections, making it ideal for managing IoT devices over a network.
For remote IoT connections, implementing strong encryption protocols like AES-256 can significantly enhance security. Additionally, adopting end-to-end encryption ensures that data remains protected throughout its entire journey, from sender to recipient.
Configuring Firewalls for IoT Devices
A firewall acts as a protective barrier between your network and external threats, playing a vital role in securing IoT devices. Properly configuring your firewall is essential to prevent unauthorized access and protect against cyberattacks.
Best Practices for Firewall Configuration
- Enable Windows Firewall: Use the built-in Windows Firewall or consider installing a third-party firewall solution for enhanced protection.
- Create Custom Rules: Develop rules to allow or block specific applications and services, ensuring only authorized traffic can access your network.
- Regular Updates: Keep your firewall software up to date to address known vulnerabilities and protect against emerging threats.
By configuring your firewall correctly, you can significantly reduce the risk of unauthorized access and ensure the security of your IoT devices, even in the face of evolving cyber threats.
Best Practices for Securing IoT Connections
Implementing best practices is crucial for maintaining secure IoT connections. These practices include regular updates, strong authentication methods, and strategic network segmentation. By adopting these measures, you can enhance the security of your IoT network and protect against potential threats.
Key Best Practices for IoT Security
- Regular Updates: Keep firmware and software updated to address security vulnerabilities and ensure your devices remain protected.
- Strong Authentication: Use complex passwords and enable two-factor authentication (2FA) to prevent unauthorized access to your devices and network.
- Network Segmentation: Isolate IoT devices from critical systems to minimize the risk of a breach spreading throughout your network.
Adopting these best practices can significantly enhance the security of your IoT network, ensuring it remains resilient against potential threats and vulnerabilities.
Addressing Common Issues in IoT Networks
Even with the most robust security measures in place, issues can arise. Promptly troubleshooting these problems is essential to maintain network stability and security. Understanding common issues and their solutions can help you address them efficiently.
Common Issues and Their Solutions
- Connection Problems: Verify network settings, restart devices, and ensure all components are properly configured to resolve connection issues.
- Security Breaches: Conduct regular security audits, update firewalls, and implement intrusion detection systems (IDS) to identify and address potential breaches.
- Performance Issues: Optimize network settings, reduce unnecessary traffic, and monitor device performance to ensure smooth operation and optimal efficiency.
By addressing these issues promptly, you can ensure the continued functionality and security of your IoT network, minimizing downtime and protecting against potential threats.
Additional Tips for Enhancing IoT Security
Here are some additional strategies to further strengthen the security of your remote IoT P2P connections:
- Intrusion Detection Systems (IDS): Deploy IDS to monitor your network for suspicious activity and respond promptly to potential threats.
- Access Control: Limit access to IoT devices to authorized personnel only, ensuring sensitive data remains protected.
- Regular Backups: Regularly back up important data to prevent loss in the event of a security breach or other unforeseen circumstances.
Implementing these tips can provide an additional layer of security, helping you safeguard your network and protect against potential threats.
Emerging Trends in IoT Security
As IoT technology continues to evolve, so do the methods used to secure it. Emerging trends such as blockchain, artificial intelligence, and quantum cryptography offer innovative solutions for enhancing IoT security and addressing future challenges.
Revolutionary Technologies in IoT Security
- Blockchain: Decentralized ledgers provide secure data storage and verification, ensuring data integrity and transparency across IoT networks.
- Artificial Intelligence: AI-driven threat detection and response systems can identify and mitigate potential threats in real-time, enhancing network security.
- Quantum Cryptography: Unbreakable encryption methods based on quantum mechanics offer unparalleled security for securing sensitive data.
By staying informed about these emerging trends, you can prepare for the future of IoT security and implement cutting-edge solutions to protect your network against evolving threats.
Kesimpulan
In conclusion, securely connecting remote IoT devices through P2P networks on Windows 10 requires a combination of proper setup, robust encryption, and adherence to best practices. By following the guidelines outlined in this article, you can establish a secure, efficient connection that protects your data and minimizes risks. We encourage you to take action by implementing the tips and best practices discussed, ensuring your IoT network remains secure and reliable.
Feel free to leave a comment below with any questions or share this article with others who may find it helpful. Stay informed, stay secure, and continue exploring the vast possibilities of IoT technology!