Comprehensive Guide To IoT SSH P2P For MacOS
Are you searching for an efficient way to connect and manage your IoT devices on macOS using SSH P2P? You've come to the right place. This detailed guide will provide you with everything you need to know about downloading, setting up, and optimizing IoT SSH P2P for Mac. It also includes troubleshooting tips to ensure a seamless experience.
Meta Description: Discover how to download, install, and optimize IoT SSH P2P for macOS. This guide covers setup instructions, security best practices, troubleshooting tips, and industry trends for managing IoT devices.
In today’s highly connected world, the Internet of Things (IoT) continues to transform how we interact with technology. IoT devices allow users to automate homes, monitor remote locations, and control devices from anywhere. However, securely managing these devices can be challenging, particularly when establishing peer-to-peer (P2P) connections.
Read also:Exploring The Influence And Achievements Of Kim Kylie And Kendall
This article is designed to provide actionable insights and practical advice for downloading and setting up IoT SSH P2P on macOS. Whether you're a tech enthusiast or a beginner, this guide will simplify the process and enhance your experience with IoT management.
Table of Contents
- Understanding IoT SSH P2P
- Advantages of Using IoT SSH P2P
- Step-by-Step Setup Guide for Mac
- Trusted Sources for Downloading IoT SSH P2P
- Key Security Considerations
- Tips for Optimizing Performance
- Troubleshooting Common Issues
- Exploring Alternatives to IoT SSH P2P
- Industry Statistics and Future Trends
- Conclusion and Next Steps
Understanding IoT SSH P2P
IoT SSH P2P is a robust solution that enables users to establish secure, direct connections between IoT devices and their computers. By utilizing SSH (Secure Shell) protocols and peer-to-peer networking, this technology allows remote access and management of IoT devices without the need for intermediary servers or complex configurations.
What Exactly Is IoT SSH P2P?
IoT SSH P2P refers to the process of connecting Internet of Things devices using Secure Shell (SSH) in a peer-to-peer manner. This approach eliminates the reliance on third-party servers, resulting in faster and more secure connections. It is especially beneficial for macOS users seeking to streamline their IoT management processes.
This technology is highly versatile, catering to scenarios such as home automation, remote device monitoring, and industrial IoT applications. With IoT SSH P2P, you can ensure your devices remain accessible and secure, regardless of their physical location.
Advantages of Using IoT SSH P2P
There are numerous benefits to leveraging IoT SSH P2P for managing your IoT devices. Below, we outline some of the key advantages:
- Enhanced Security: SSH ensures encrypted communication between devices, significantly reducing the risk of unauthorized access.
- Direct Connections: Peer-to-peer networking eliminates the need for intermediary servers, leading to faster and more reliable connections.
- Cost-Effectiveness: By avoiding server hosting fees or subscription services, IoT SSH P2P offers a cost-efficient solution for managing IoT devices.
- Flexibility: This technology supports a wide range of IoT devices, from smart home gadgets to industrial sensors, all managed through a single platform.
Step-by-Step Setup Guide for Mac
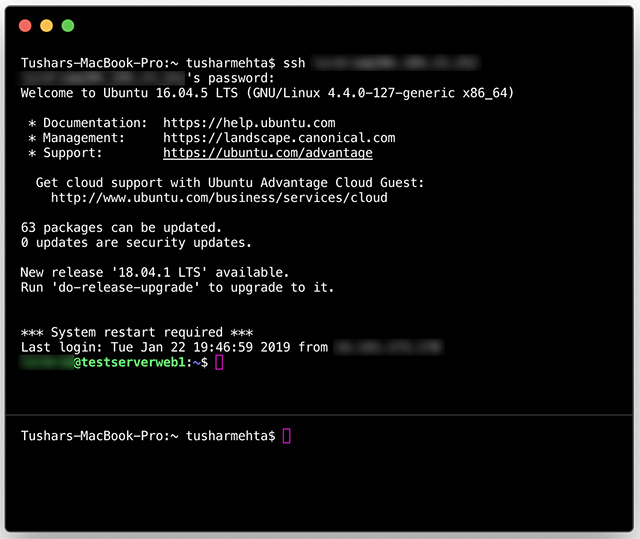
How to Set Up IoT SSH P2P on macOS
Setting up IoT SSH P2P on your Mac involves a few simple steps. Follow this comprehensive guide to ensure a smooth setup process:
Read also:Alexis Bellino Net Worth 2023 A Deep Dive Into Her Wealth Career And Lifestyle
- Download the Software: Obtain IoT SSH P2P from a trusted source (detailed in the next section).
- Install the Application: Follow the on-screen instructions to complete the installation process.
- Configure Settings: Launch the application and adjust the settings to align with your IoT devices.
- Test the Connection: Verify that the setup is functioning correctly by testing the connection.
Tips for a Successful Setup
To ensure a seamless setup process, consider the following recommendations:
- Software Compatibility: Ensure your Mac is running the latest macOS version to avoid potential compatibility issues.
- Device Configuration: Confirm that your IoT devices are properly configured and connected to the internet.
- Official Documentation: Refer to the official documentation for additional guidance and troubleshooting tips.
Trusted Sources for Downloading IoT SSH P2P
When downloading IoT SSH P2P for macOS, it's essential to choose a reputable source to ensure the software is safe and free from malware. Below are some reliable websites where you can find the software:
Always verify the authenticity of the download link and review user feedback to ensure the software is dependable.
Key Security Considerations
Security should be a top priority when working with IoT SSH P2P. Below are some best practices to safeguard your devices and data:
- Strong Passwords: Avoid using easily guessable passwords and enable two-factor authentication whenever possible.
- Regular Updates: Keep the IoT SSH P2P software updated to address any security vulnerabilities.
- Connection Monitoring: Regularly monitor active connections and terminate any suspicious activity promptly.
Common Security Threats
Some prevalent security threats associated with IoT SSH P2P include:
- Brute-force attacks
- Man-in-the-middle attacks
- Unsecured network configurations
Tips for Optimizing Performance
Maximizing the efficiency of your IoT SSH P2P setup involves implementing the following optimization strategies:
- Network Optimization: Configure your network for optimal performance, minimizing latency and maximizing bandwidth.
- Data Compression: Enable data compression in SSH settings to reduce the volume of data transmitted over the network.
- Connection Limitation: Restrict the number of simultaneous connections to prevent overloading your devices.
Tools for Monitoring Performance
Several tools can assist in monitoring and optimizing the performance of your IoT SSH P2P setup:
Troubleshooting Common Issues
Even with careful setup and optimization, issues with IoT SSH P2P may arise. Below are some common problems and their solutions:
- Connection Errors: Verify your network settings and ensure all devices are properly connected to the internet.
- Authentication Failures: Confirm the accuracy of your login credentials and update them if necessary.
- Slow Performance: Identify and eliminate network bottlenecks, and consider upgrading your hardware if needed.
When to Seek Professional Assistance
If you're unable to resolve the issue independently, it may be time to seek professional help. Consult certified technicians or the official support forums for additional guidance.
Exploring Alternatives to IoT SSH P2P
While IoT SSH P2P is a powerful tool, several alternatives exist for managing IoT devices on macOS. Some popular options include:
Each alternative has its unique strengths and weaknesses, so it's crucial to evaluate them thoroughly before making a decision.
Industry Statistics and Future Trends
The IoT market is experiencing rapid growth, with projections indicating over 75 billion connected devices by 2025. This expansion is driven by technological advancements, increasing demand for smart devices, and the need for more efficient data management solutions.
According to a report by Statista, the global IoT market is expected to reach $1.5 trillion by 2030. This presents significant opportunities for businesses and individuals looking to capitalize on the IoT revolution.
Conclusion and Next Steps
In summary, IoT SSH P2P free download for macOS provides a secure and efficient method for managing IoT devices. By following the steps outlined in this guide, you can set up, optimize, and troubleshoot your IoT SSH P2P setup effortlessly.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with your friends and colleagues. For more insights and updates on IoT technology, explore our other articles on the website.
Disclaimer: Always download software from trusted sources to ensure your safety and security. We are not responsible for any damages caused by unauthorized or malicious software.