Mastering Secure IoT Connections With P2P SSH On Windows 10
In today's fast-paced technological landscape, establishing secure connections between remote IoT devices using P2P SSH on Windows 10 has become an essential skill for IT professionals and tech enthusiasts alike. As the number of interconnected devices continues to grow, ensuring robust and secure communication channels is crucial for safeguarding sensitive information and maintaining the integrity of networks. This comprehensive guide will explore the methods, tools, and best practices for setting up a secure connection between remote IoT devices using P2P SSH on Windows 10.
Connecting IoT devices securely is no longer a luxury but a necessity. It is vital to protect networks from potential cyber threats that could compromise data or disrupt operations. Whether you're managing smart home devices or overseeing large-scale IoT deployments in enterprises, understanding how to set up a P2P SSH connection ensures that your data remains protected. This article will provide a step-by-step guide to achieving this, offering valuable insights and practical advice along the way.
By the end of this guide, you will have a thorough understanding of the tools, configurations, and security measures needed to create a secure and reliable connection between remote IoT devices. Let’s dive in and explore the world of secure IoT connectivity with P2P SSH on Windows 10.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
Table of Contents
- Understanding IoT and Its Security Challenges
- Exploring P2P SSH and Its Role in IoT Security
- Leveraging Windows 10 Features for Secure Connections
- The Setup Process for Secure IoT Connections
- Essential Tools and Software for Secure Connections
- Key Security Measures for IoT Devices
- Addressing Common Issues in IoT Connectivity
- Best Practices for Enhancing IoT Security
- Real-World Applications of Secure IoT Connections
- Future Trends Shaping IoT Security
Understanding IoT and Its Security Challenges
The Internet of Things (IoT) has transformed the way we interact with technology, offering unprecedented convenience and efficiency in both personal and professional settings. From smart home appliances to industrial sensors, IoT devices have revolutionized industries and enhanced everyday life. However, the rapid proliferation of these devices has also introduced significant security challenges. With billions of interconnected devices, ensuring secure communication is now more critical than ever.
Why IoT Security Matters
IoT devices often lack comprehensive security features, making them susceptible to cyberattacks. These vulnerabilities can be exploited by malicious actors to gain unauthorized access to networks, steal sensitive data, or disrupt services. To address these risks, it is imperative to implement secure communication protocols, such as P2P SSH, when connecting remote IoT devices. This ensures that your network remains protected and your data remains private.
Exploring P2P SSH and Its Role in IoT Security
P2P SSH (Peer-to-Peer Secure Shell) is a powerful tool for establishing secure and encrypted connections between devices. It ensures that data transmitted between devices remains private and protected from unauthorized access. By leveraging P2P SSH, you can create a secure tunnel between IoT devices and your Windows 10 machine, enabling seamless and secure communication.
Key Features of P2P SSH
- Encrypted data transmission to protect sensitive information.
- Robust authentication and authorization mechanisms to ensure only authorized devices can connect.
- Support for public key infrastructure (PKI) for enhanced security.
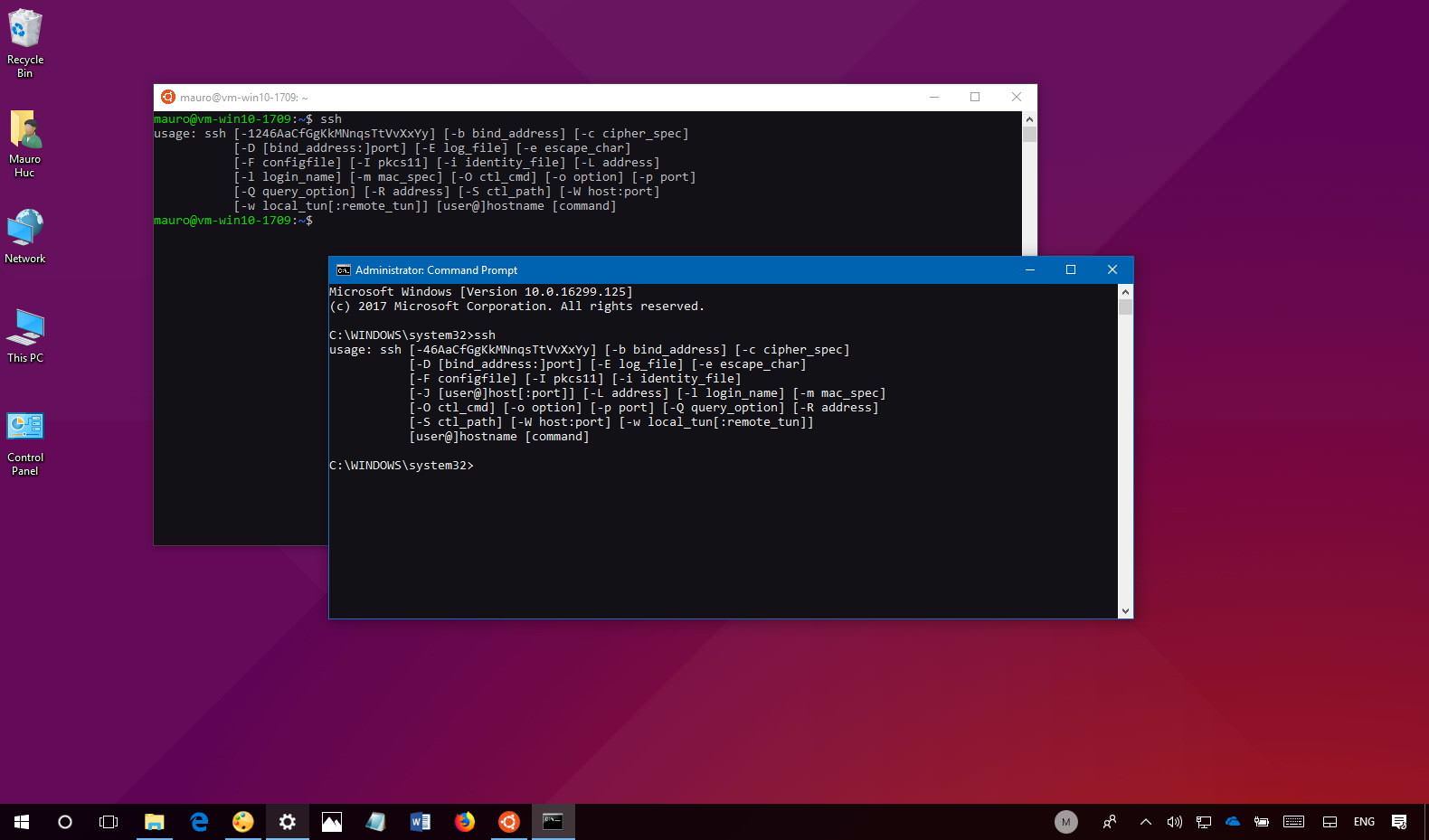
Leveraging Windows 10 Features for Secure Connections
Windows 10 offers a range of built-in features that enhance its ability to securely connect with remote IoT devices. These features include advanced firewall settings, secure authentication protocols, and robust encryption capabilities. By utilizing these features, you can create a secure and reliable environment for your IoT devices.
Configuring Windows 10 for IoT Connectivity
To configure Windows 10 for IoT connectivity, you will need to enable specific settings and install necessary software. This includes configuring the Windows Firewall to allow secure connections, setting up SSH server software, and ensuring that your system is up-to-date with the latest security patches. These steps are crucial for creating a secure and stable connection between your IoT devices and your Windows 10 machine.
The Setup Process for Secure IoT Connections
Establishing a secure connection between remote IoT devices using P2P SSH on Windows 10 involves several key steps. These include installing the necessary software, configuring network settings, and testing the connection to ensure it functions correctly. By following this step-by-step guide, you can create a secure and reliable connection for your IoT devices.
Read also:Exploring Elon Musks Partners And Kids A Comprehensive Look
Step-by-Step Guide
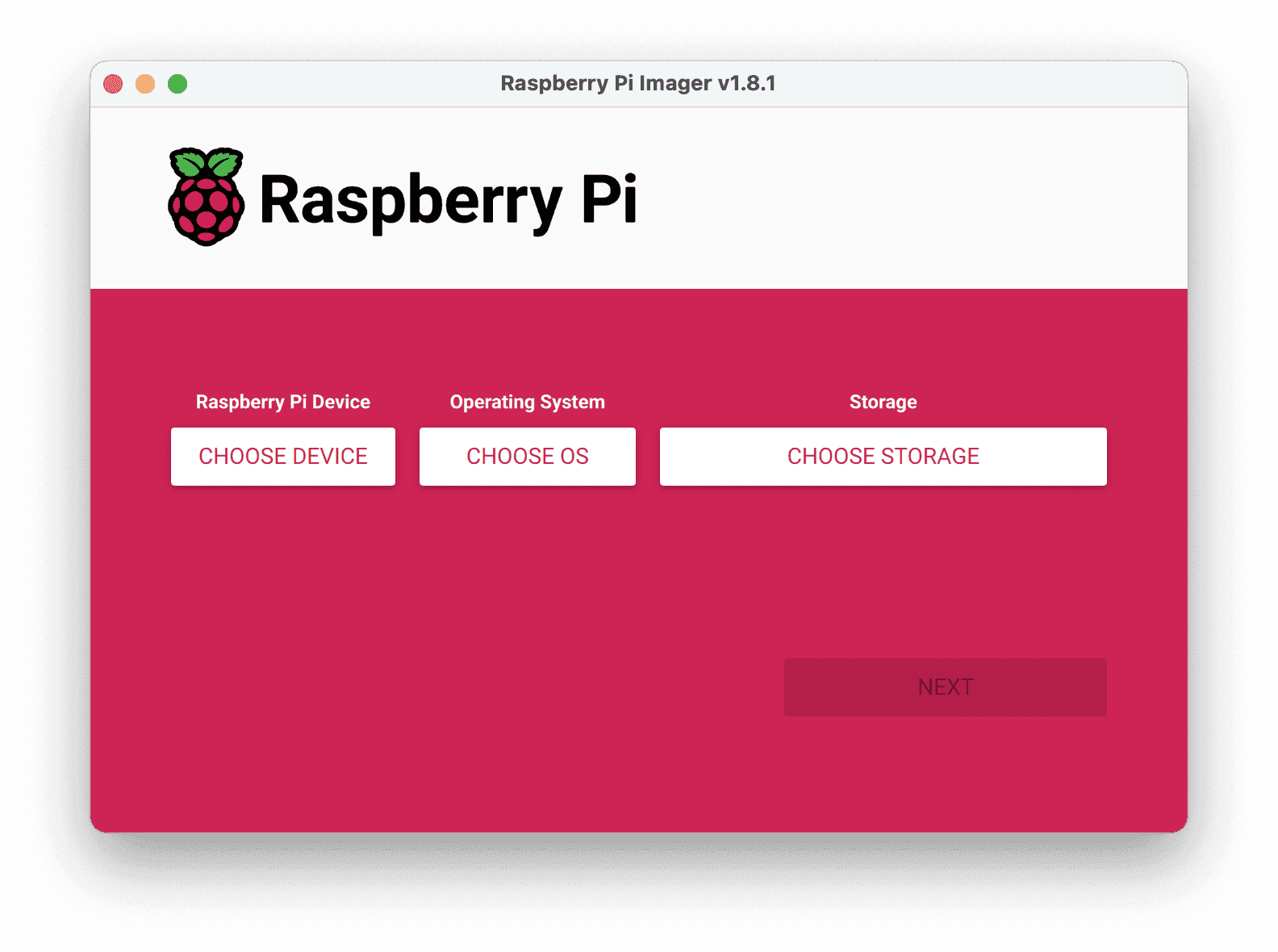
- Install an SSH server on your Windows 10 machine to enable secure communication.
- Configure the SSH server settings to allow remote connections, ensuring that only authorized devices can access your network.
- Set up your IoT devices to connect via SSH, ensuring that they are properly configured for secure communication.
- Test the connection thoroughly to ensure that data transmission is secure and reliable.
Essential Tools and Software for Secure Connections
To securely connect remote IoT devices using P2P SSH on Windows 10, you will need the right tools and software. These include SSH client and server software, network configuration tools, and security utilities. Some popular options include OpenSSH, PuTTY, and Windows Subsystem for Linux (WSL), which provide robust and reliable solutions for secure IoT connectivity.
Recommended Tools
- OpenSSH for Windows: A powerful SSH server that enables secure communication between devices.
- PuTTY SSH client: A versatile and user-friendly tool for managing SSH connections.
- Windows Subsystem for Linux (WSL): A valuable resource for running Linux-based applications on Windows, enhancing flexibility and functionality.
Key Security Measures for IoT Devices
Implementing strong security measures is essential for protecting IoT devices and ensuring the integrity of your network. This includes using strong passwords, enabling two-factor authentication, and regularly updating firmware. Additionally, monitoring network activity and implementing intrusion detection systems can help identify and mitigate potential threats, providing an additional layer of security.
Best Security Practices
- Use strong, unique passwords for all devices to prevent unauthorized access.
- Enable two-factor authentication to enhance security and protect against unauthorized access.
- Regularly update firmware and software to address vulnerabilities and ensure compatibility with the latest security protocols.
Addressing Common Issues in IoT Connectivity
Even with careful planning and implementation, issues can arise when setting up secure IoT connections. Common problems include configuration errors, network connectivity issues, and software conflicts. To address these challenges, it is important to have a comprehensive troubleshooting strategy in place. This includes double-checking settings, testing network configurations, and updating or reinstalling software as needed.
Common Issues and Solutions
- Configuration errors: Carefully review settings and reconfigure as necessary to ensure proper functionality.
- Network connectivity issues: Test network settings and verify proper routing to resolve connectivity problems.
- Software conflicts: Update or reinstall software to resolve conflicts and ensure compatibility with your system.
Best Practices for Enhancing IoT Security
Following best practices for secure IoT connections can significantly enhance the security of your network. These practices include implementing robust authentication mechanisms, using encryption for all data transmissions, and regularly auditing your network for vulnerabilities. By adhering to these principles, you can ensure that your IoT devices remain secure and your network remains protected.
Implementing Best Practices
Regularly review and update your security protocols to adapt to emerging threats and technologies. Stay informed about the latest developments in IoT security and incorporate new strategies and tools into your workflow to maintain a high level of protection.
Real-World Applications of Secure IoT Connections
Real-world applications of secure IoT connections using P2P SSH on Windows 10 demonstrate the effectiveness of this approach. Industries such as healthcare, manufacturing, and smart cities have successfully implemented secure communication protocols for IoT devices, enhancing efficiency and protecting sensitive data.
Example Case Study
In the healthcare industry, secure IoT connections are vital for protecting patient data and ensuring the reliability of medical devices. By using P2P SSH, healthcare providers can securely monitor and manage remote devices, improving patient care and reducing risks. This case study highlights the importance of secure communication protocols in safeguarding critical systems and data.
Future Trends Shaping IoT Security
As technology continues to evolve, so do the trends in IoT security. Emerging technologies such as quantum computing, blockchain, and artificial intelligence are expected to play a significant role in shaping the future of IoT security. Staying informed about these trends will help you stay ahead of potential threats and ensure the security of your IoT devices.
Emerging Technologies
- Quantum computing for enhanced encryption, providing unparalleled security for data transmissions.
- Blockchain for secure data management, ensuring transparency and integrity in IoT ecosystems.
- Artificial intelligence for threat detection, enabling proactive identification and mitigation of potential security risks.
Conclusion
In conclusion, securely connecting remote IoT devices using P2P SSH on Windows 10 is an essential skill for anyone working with IoT technology. By following the steps outlined in this guide, you can create a secure and reliable connection that protects your data and ensures the integrity of your network. Remember to implement best practices, regularly update your security protocols, and stay informed about emerging trends in IoT security to maintain a high level of protection.
We invite you to share your thoughts and experiences in the comments below. Have you successfully implemented secure IoT connections using P2P SSH on Windows 10? What challenges did you encounter, and how did you overcome them? Additionally, explore our other articles for more insights into IoT security and related topics.