Mastering Remote IoT Connectivity On Mac
In today's highly interconnected world, establishing secure remote connectivity for IoT devices behind firewalls is a critical challenge faced by businesses and individuals alike. Whether you're managing smart devices at home or overseeing an enterprise-level IoT infrastructure, understanding how to create robust and secure connections is essential. This comprehensive guide will walk you through the best methods to connect IoT devices remotely on a Mac, ensuring you have the tools and knowledge to achieve seamless connectivity without relying on Windows-based systems.
As technology continues to evolve, IoT devices are becoming increasingly prevalent in homes and workplaces. However, setting up secure remote connections for these devices, especially when dealing with firewalls, can be a complex task. This article will provide an in-depth exploration of how to configure remote connections for IoT devices on a Mac. It will offer practical advice, detailed instructions, and expert tips to help you navigate this process successfully.
Regardless of whether you're a tech enthusiast, a small business owner, or an IT professional, this guide is designed to assist you in overcoming the challenges of remote IoT connectivity. We will cover everything from setting up your environment and selecting the right tools to troubleshooting common issues and ensuring optimal performance, all while maintaining the highest level of security.
Read also:Exploring Elon Musks Partners And Kids A Comprehensive Look
Exploring Remote IoT Connectivity
What Exactly is Remote IoT Connectivity?
Remote IoT connectivity refers to the ability to access and manage IoT devices from a distance, regardless of their physical location. This capability is particularly valuable for devices situated behind firewalls, which are designed to safeguard networks from unauthorized access. By establishing secure and reliable connections, users can monitor and control their IoT devices as if they were physically present, enhancing both convenience and efficiency.
Key components of remote IoT connectivity include:
- Secure communication protocols to ensure data integrity and privacy
- Data encryption to protect sensitive information during transmission
- Advanced firewall traversal techniques to bypass network restrictions without compromising security
Advantages of Using a Mac for Remote IoT Connections
Macs offer several unique advantages when it comes to remote IoT connectivity. Their Unix-based architecture provides robust security features and seamless compatibility with a wide range of open-source tools. Additionally, macOS's powerful built-in terminal and scripting capabilities make it an ideal platform for configuring and managing IoT devices with precision and ease.
Some key benefits of using a Mac for remote IoT connections include:
- Seamless integration with Apple's ecosystem, enabling smooth interoperability with other Apple devices
- State-of-the-art security features to protect your devices and data from potential threats
- Outstanding compatibility with Linux-based tools, expanding the range of available resources and solutions
Preparing Your Mac for IoT Connectivity
Setting Up Your Environment for Success
Before diving into the process of remote IoT connectivity, it's crucial to prepare your Mac properly. This involves installing necessary software, configuring network settings, and ensuring your system is secure and up-to-date. Below is a step-by-step guide to help you get started:
- Install a terminal emulator such as iTerm2 to enhance functionality and streamline workflows
- Update macOS to the latest version to ensure you have the latest security patches and feature improvements
- Install Homebrew, a popular and versatile package manager for macOS, to simplify the installation of essential tools and utilities
Selecting the Right Tools for the Job
Choosing the appropriate tools is essential for achieving successful IoT connectivity. Some of the most popular options include:
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
- MQTT brokers, such as Mosquitto, for facilitating efficient and secure message exchanges between IoT devices
- SSH clients for establishing encrypted and secure connections to remote devices
- Network monitoring tools, such as Wireshark, for diagnosing and resolving connectivity issues
For example, Mosquitto is a widely-used MQTT broker that supports secure communication between IoT devices. Similarly, tools like WireGuard can help create secure tunnels through firewalls, enabling seamless remote access.
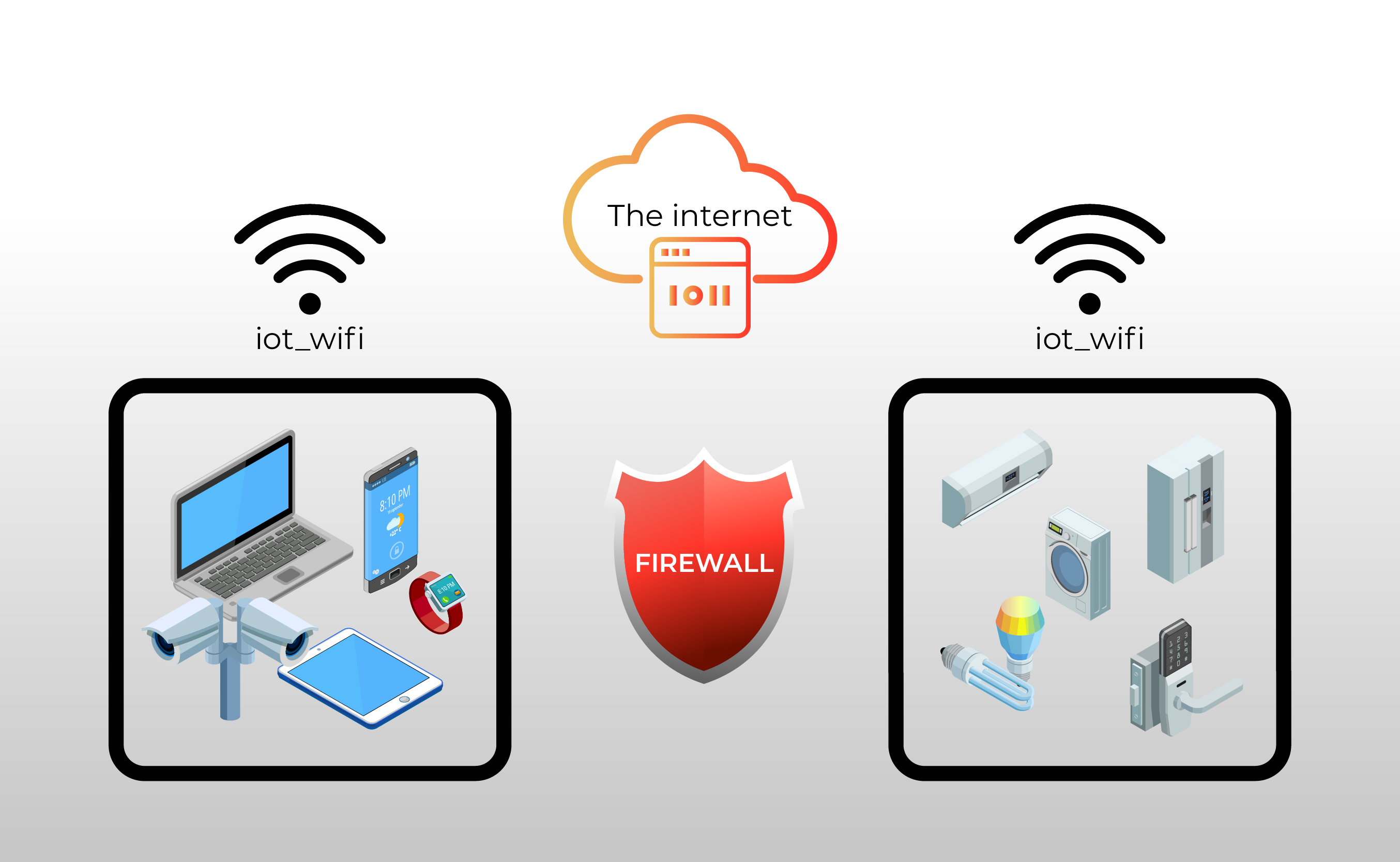
Understanding and Navigating Firewalls
What Are Firewalls and Why Do They Matter?
Firewalls are sophisticated network security systems designed to monitor and control incoming and outgoing network traffic based on predefined security rules. While they play a vital role in protecting networks from unauthorized access, they can sometimes pose challenges for remote IoT connectivity. Gaining a thorough understanding of how firewalls work is the first step in overcoming these obstacles and ensuring secure access to your IoT devices.
Effective Methods for Traversing Firewalls
There are several techniques you can employ to traverse firewalls while maintaining the highest level of security. These include:
- Port forwarding to direct incoming traffic to specific devices or services
- VPN tunnels to create encrypted connections that bypass firewall restrictions
- Reverse SSH tunnels to establish secure connections from behind a firewall
Each method has its own set of advantages and limitations, and the choice ultimately depends on your specific requirements and network configuration.
Acquiring and Installing Necessary Software
Identifying the Tools You Need
To establish remote connectivity for IoT devices, you'll need to download and install several essential tools. These may include:
- MQTT clients, such as MQTT Explorer, for connecting to brokers and testing message exchanges
- SSH clients for secure remote access to IoT devices
- Network monitoring software, such as Wireshark, for diagnosing and resolving connectivity issues
For instance, MQTT Explorer is a user-friendly MQTT client that allows you to connect to brokers, test message exchanges, and troubleshoot issues efficiently. Similarly, tools like Wireshark can provide valuable insights into network activity, helping you identify and resolve potential problems.
Step-by-Step Installation Process
Installing these tools on a Mac is a straightforward process. Follow these steps to get started:
- Download the software from official and trusted sources to ensure security and reliability
- Open the downloaded file and follow the installation wizard's instructions carefully
- Verify the installation by launching the application and testing its functionality
Configuring and Managing IoT Devices
Setting Up Your IoT Devices for Optimal Performance
Once your Mac is fully prepared, it's time to configure your IoT devices for remote connectivity. This process involves several key steps:
- Connecting devices to your network via Wi-Fi or Ethernet, depending on your setup and requirements
- Configuring security settings to protect your devices and data from unauthorized access
- Testing connectivity to ensure everything is functioning as expected
For example, if you're using a Raspberry Pi as an IoT gateway, you'll need to establish Wi-Fi or Ethernet connections, configure firewall rules, and set up any additional security measures necessary for your specific use case.
Troubleshooting Common Issues and Challenges
During the setup process, you may encounter various issues such as:
- Connection timeouts due to network configuration errors or firewall restrictions
- Authentication failures resulting from incorrect credentials or misconfigured security settings
- Network configuration errors that prevent devices from communicating effectively
To resolve these issues, consult the device documentation or seek assistance from online communities and forums where experts and enthusiasts share their knowledge and experience.
Enhancing Security for Remote IoT Connectivity
Why Security Should Be Your Top Priority
Security is of paramount importance when dealing with IoT devices, especially when connecting them remotely. Compromised devices can lead to data breaches, privacy violations, and other serious security risks. Implementing robust security measures is essential for protecting your network and ensuring the integrity of your data.
Best Practices for Securing Your IoT Connections
Adopt the following best practices to enhance the security of your remote IoT connections:
- Use strong, unique passwords and enable two-factor authentication to prevent unauthorized access
- Regularly update firmware and software to protect against known vulnerabilities and exploits
- Monitor network activity continuously for any signs of suspicious behavior or potential threats
Optimizing Performance for Seamless Connectivity
Tips for Improving Remote IoT Connectivity
To ensure optimal performance and reliability, consider implementing the following tips:
- Optimize network settings to minimize latency and improve responsiveness
- Use compression techniques to reduce the size of data transfers and conserve bandwidth
- Implement load balancing for high-traffic devices to distribute the workload efficiently
Importance of Monitoring and Maintenance
Regular monitoring and maintenance are crucial for maintaining reliable and secure remote IoT connections. Tools like Nagios or Zabbix can help you monitor device health, network performance, and potential security threats, enabling you to take proactive measures to address any issues that arise.
Real-World Applications of Remote IoT Connectivity
Case Studies and Practical Examples
Explore real-world applications of remote IoT connectivity to gain insights into its versatility and potential. Some notable examples include:
- Smart home automation systems that allow users to control lighting, temperature, and security remotely
- Industrial IoT implementations that enable real-time monitoring and control of manufacturing processes
- Remote healthcare monitoring solutions that provide patients and healthcare providers with instant access to vital health data
These examples demonstrate the transformative impact of IoT technology when combined with secure remote connectivity, highlighting its potential to enhance efficiency, convenience, and quality of life across various industries and applications.
Emerging Trends in IoT Connectivity
Innovative Technologies Shaping the Future
As technology continues to evolve, new and innovative solutions for IoT connectivity are emerging. These include:
- 5G networks, offering faster data transfer speeds and lower latency for enhanced performance
- Edge computing, enabling localized processing and reducing reliance on centralized cloud resources
- Blockchain technology, providing secure and transparent methods for data transactions and device authentication
Staying informed about these emerging trends and technologies can help you prepare for the future of IoT connectivity and ensure your systems remain cutting-edge and competitive.
Conclusion
In conclusion, achieving secure and reliable remote IoT connectivity behind firewalls on a Mac is entirely possible with the right tools, knowledge, and approach. By following the steps and best practices outlined in this guide, you can establish robust connections for your IoT devices, ensuring they remain accessible, secure, and efficient. Always prioritize security and keep your systems updated to protect against potential threats and vulnerabilities.
We encourage you to share your experiences, insights, and feedback in the comments section below. Additionally, explore other articles on our site to learn more about IoT and related technologies. Together, let's continue to build a smarter, more connected, and secure world!
Table of Contents
- Exploring Remote IoT Connectivity
- Preparing Your Mac for IoT Connectivity
- Understanding and Navigating Firewalls
- Acquiring and Installing Necessary Software
- Configuring and Managing IoT Devices