Mastering Secure IoT Connections With P2P Downloads On Mac
Establishing secure connections for remote IoT devices through P2P downloads on Mac is a cornerstone of modern technology. As the number of interconnected devices continues to grow, implementing strong security measures is essential to safeguard sensitive data and maintain user privacy. This comprehensive guide explores the intricacies of securing IoT connections while using P2P downloads on Mac, offering practical advice and actionable strategies for users.
In today's fast-evolving digital landscape, the Internet of Things (IoT) has transformed the way we interact with technology, enhancing convenience and efficiency in both personal and professional settings. From smart homes to industrial automation, IoT devices have become indispensable. However, with this advancement comes the challenge of ensuring secure connections, especially when utilizing peer-to-peer (P2P) networks on Mac devices for file downloads.
This article aims to provide an in-depth understanding of securely connecting remote IoT devices using P2P downloads on Mac. We will delve into key concepts, potential risks, and best practices to ensure your data remains protected. Whether you're a tech enthusiast or a professional seeking to enhance your cybersecurity knowledge, this guide offers valuable insights tailored to your needs.
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
Table of Contents
- Exploring the Internet of Things
- Understanding P2P Networks
- Enhancing Secure Connections on Mac
- Navigating Risks and Challenges
- Best Practices for Security
- Essential Tools and Software
- Advanced Encryption Methods
- Strengthening Firewall and Network Security
- Prioritizing Data Privacy
- The Future of IoT Security
- Conclusion
Exploring the Internet of Things
The Internet of Things (IoT) refers to the interconnected network of physical devices embedded with sensors, software, and connectivity that enable them to exchange data seamlessly. These devices range from simple household appliances to sophisticated industrial machinery. By securely connecting remote IoT devices through P2P downloads on Mac, users can enhance their experience while ensuring robust data protection.
Advantages of IoT Devices
IoT devices bring numerous benefits to the table, including:
- Automation that reduces manual intervention and increases productivity.
- Improved efficiency in operations by streamlining processes.
- Enhanced data collection capabilities for better decision-making.
- Cost savings through optimized resource utilization.
Challenges in IoT Deployment
Despite their numerous advantages, IoT devices present significant challenges, particularly in terms of security. Ensuring secure connections is critical to preventing unauthorized access and safeguarding sensitive data from breaches.
Understanding P2P Networks
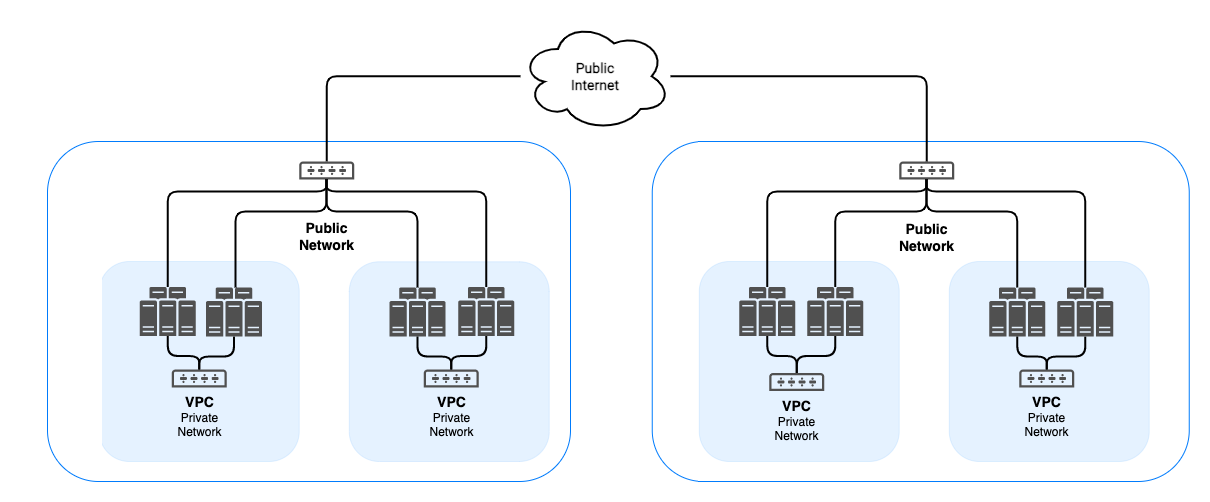
Peer-to-peer (P2P) networks enable devices to connect directly without relying on centralized servers. This decentralized architecture is especially beneficial for securely connecting remote IoT devices through P2P downloads on Mac, as it minimizes latency and reduces bandwidth consumption.
How P2P Networks Operate
P2P networks function by allowing devices to act as both clients and servers. This decentralized approach not only enhances efficiency and reliability but also ensures smoother data transmission, making it an ideal choice for IoT applications.
Benefits of P2P Networks
- Reduced dependence on centralized servers, minimizing single points of failure.
- Improved scalability, accommodating a growing number of devices and data exchanges.
- Enhanced fault tolerance, ensuring continuity even if some nodes fail.
Enhancing Secure Connections on Mac
Securing IoT connections on Mac involves implementing robust protocols and adhering to best practices. By focusing on securely connecting remote IoT devices through P2P downloads on Mac, users can effectively protect their devices and data from potential threats.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
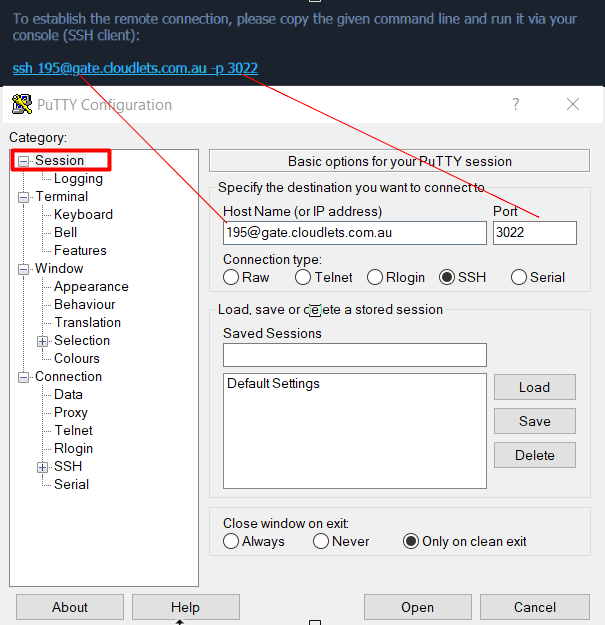
Essential Security Protocols
Some of the critical security protocols for Mac users include:
- SSL/TLS encryption for securing data in transit.
- SSH tunneling for establishing secure communication channels.
- IPSec for protecting network communications at the IP layer.
Optimizing Security Settings
Adjusting security settings on Mac devices is vital for maintaining secure IoT connections. Regularly updating your operating system and installing security patches are essential steps to address vulnerabilities and enhance protection.
Navigating Risks and Challenges
While securely connecting remote IoT devices through P2P downloads on Mac offers numerous advantages, it also presents significant risks and challenges. Cyber threats such as malware, phishing attacks, and unauthorized access can jeopardize IoT devices and networks.
Common Security Risks
- Malware infections that can compromise device functionality and data integrity.
- Data breaches that expose sensitive information to unauthorized parties.
- Unsecured network connections that leave devices vulnerable to attacks.
Addressing Security Challenges
To mitigate these risks, users should adopt proactive security measures, such as regular software updates, strong password policies, and network segmentation. These practices help fortify defenses against potential threats.
Best Practices for Security
Implementing best practices is crucial for securely connecting remote IoT devices through P2P downloads on Mac. These practices include:
- Using strong, unique passwords to prevent unauthorized access.
- Enabling two-factor authentication for an additional layer of security.
- Regularly monitoring network activity to detect and respond to suspicious behavior promptly.
Securing IoT Devices
Securing IoT devices involves configuring default settings, disabling unnecessary features, and applying firmware updates in a timely manner. These steps help protect devices from potential vulnerabilities and ensure long-term security.
Implementing Network Security Measures
Network security measures, such as firewalls and intrusion detection systems, play a critical role in safeguarding IoT connections. Users should ensure their networks are properly configured and continuously monitored for any suspicious activity.
Essential Tools and Software
Several tools and software solutions are available to enhance the security of IoT connections. These tools assist users in securely connecting remote IoT devices through P2P downloads on Mac by offering advanced features and functionalities.
Popular Security Tools
- WireGuard for secure and efficient network connections.
- OpenVPN for creating encrypted tunnels for data transmission.
- ClamXav for detecting and eliminating malware on Mac devices.
Recommended Software
Mac users can leverage software like Little Snitch, which monitors outgoing connections and alerts users to potential threats. Additionally, antivirus programs like Sophos provide comprehensive protection against malware and other cyber threats, ensuring a secure environment for IoT operations.
Advanced Encryption Methods
Encryption is a cornerstone of securely connecting remote IoT devices through P2P downloads on Mac. By encrypting data transmissions, users can protect sensitive information from unauthorized access and interception.
Types of Encryption
Common encryption methods include:
- Symmetric encryption, which uses the same key for both encryption and decryption.
- Asymmetric encryption, which utilizes a pair of keys (public and private) for secure communication.
- Hash functions, which transform data into a fixed-size string of characters for secure storage and verification.
Implementing Encryption Protocols
Users should implement encryption protocols such as AES and RSA to secure their IoT connections. These protocols provide robust protection against data interception and tampering, ensuring the confidentiality and integrity of transmitted information.
Strengthening Firewall and Network Security
Firewalls and network security measures are indispensable for maintaining secure IoT connections. By configuring firewalls and implementing network segmentation, users can enhance the security of their devices and networks, minimizing the risk of breaches.
Configuring Firewalls
Mac users can configure firewalls using built-in tools like the macOS Firewall or third-party solutions like pfSense. These firewalls help block unauthorized access and protect against malicious attacks, ensuring a secure environment for IoT operations.
Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments. This approach limits the potential impact of a security breach and enhances overall network security, providing an additional layer of protection for IoT devices.
Prioritizing Data Privacy
Data privacy is a critical consideration when securely connecting remote IoT devices through P2P downloads on Mac. Users must ensure their data is protected from unauthorized access and misuse, maintaining trust and compliance with regulations.
Protecting Personal Data
To safeguard personal data, users should implement privacy-enhancing technologies such as anonymization and data minimization. These techniques help reduce the risk of data exposure and misuse, ensuring user information remains confidential.
Ensuring Regulatory Compliance
Adhering to data privacy regulations such as GDPR and CCPA is essential for ensuring compliance and protecting user data. Organizations must implement appropriate safeguards to meet these regulatory requirements, fostering trust and security in the IoT ecosystem.
The Future of IoT Security
The future of IoT security hinges on the development of advanced technologies and protocols. As securely connecting remote IoT devices through P2P downloads on Mac becomes increasingly prevalent, innovations in encryption, authentication, and network security will play a pivotal role in protecting devices and data.
Emerging Technologies
Emerging technologies such as blockchain and quantum cryptography offer promising solutions for enhancing IoT security. These technologies provide robust protection against cyber threats and ensure the integrity of data transmissions, paving the way for a more secure IoT landscape.
Addressing Future Challenges
Despite advancements in technology, challenges such as scalability, interoperability, and standardization remain. Addressing these challenges will be crucial for the continued growth and widespread adoption of IoT devices, ensuring a secure and connected future.
Conclusion
Securing IoT connections while utilizing P2P downloads on Mac demands a comprehensive approach that integrates robust security protocols, best practices, and cutting-edge technologies. By focusing on securely connecting remote IoT devices through P2P downloads on Mac, users can protect their devices and data from potential threats, fostering a safer and more connected digital environment.
We encourage readers to take proactive steps in enhancing their cybersecurity measures. Share your thoughts and experiences in the comments section below, and explore other articles on our website for more insights into technology and security. Together, we can build a more secure and resilient IoT ecosystem for the future.