Exploring The Best Free SSH Remote IoT Device Solutions
In today's fast-paced digital era, the need for secure, efficient, and cost-effective remote access solutions has grown exponentially, especially within the Internet of Things (IoT) landscape. If you're on the lookout for the best SSH remote IoT device options that are free, you're in the right place. This in-depth guide will take you through the world of SSH remote IoT devices, examining their unique features, benefits, and how they can transform your connectivity experience.
As both businesses and individuals increasingly rely on interconnected devices, maintaining seamless remote access without jeopardizing security is crucial. Free SSH remote IoT devices offer a budget-friendly yet powerful solution for managing and monitoring your IoT infrastructure from anywhere across the globe.
Whether you're a tech enthusiast, a small business owner, or an experienced IT professional, understanding the intricacies of SSH remote IoT devices can significantly enhance your operational efficiency. Let's delve deeper into the possibilities and discover the top options available today.
Read also:Alexis Bellino Net Worth 2023 A Deep Dive Into Her Wealth Career And Lifestyle
Table of Contents
- Introduction to SSH Remote IoT Device
- Why Choose SSH for Remote Access
- Top Free SSH Remote IoT Devices
- Benefits of Using SSH Remote IoT Devices
- Security Considerations
- How to Set Up SSH Remote IoT Device
- Comparison of Popular SSH Remote IoT Devices
- Troubleshooting Common Issues
- Future of SSH Remote IoT Devices
- Conclusion
Understanding SSH Remote IoT Devices
SSH (Secure Shell) is a cryptographic protocol designed to facilitate secure communication over an unsecured network. When applied to IoT devices, SSH remote access becomes an essential tool for managing and monitoring devices remotely. The best free SSH remote IoT device options empower users to fully utilize their IoT infrastructure without additional financial burdens.
What Is SSH Protocol?
SSH protocol ensures secure data transfer by encrypting all communication between the client and server. Additionally, it authenticates users, preventing unauthorized access and guaranteeing data integrity. This protocol is a cornerstone for maintaining secure connections in the digital world.
Key Features of SSH Remote IoT Devices
- Secure communication through robust encryption methods
- Support for various authentication methods, including public key and password-based authentication
- Compatibility with a wide range of IoT platforms and operating systems
- Ability to execute remote commands, enabling efficient device management
Why SSH is the Ideal Choice for Remote Access
Among the many remote access protocols available, SSH stands out due to its strong security features and user-friendly interface. Below are some compelling reasons why SSH is the preferred option for managing IoT devices remotely:
Superior Security
SSH employs advanced encryption algorithms, such as AES and RSA, to protect data during transmission. This makes it an excellent choice for sensitive IoT applications where security is paramount.
Reliable and Stable Connections
SSH connections are renowned for their stability, ensuring uninterrupted access even under challenging network conditions. This reliability is crucial for maintaining consistent IoT device performance.
Cost-Effective and Versatile
With a variety of free SSH remote IoT device options available, businesses can significantly reduce infrastructure costs without sacrificing functionality. SSH's versatility allows it to adapt to a wide range of use cases, making it a practical choice for organizations of all sizes.
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
Top Free SSH Remote IoT Devices to Consider
The market offers numerous free SSH remote IoT devices, each with its own set of features and capabilities. Below are some of the top options available:
1. Raspberry Pi with SSH
The Raspberry Pi is a highly versatile single-board computer that supports SSH right out of the box. Its affordability, coupled with its expandability, makes it a popular choice for IoT projects. Users can easily configure SSH to manage their IoT devices remotely.
2. ESP32 with SSH Support
ESP32 is a powerful IoT microcontroller that can be configured to support SSH, enabling secure remote access to your IoT projects. Its low power consumption and built-in Wi-Fi and Bluetooth capabilities make it an attractive option for resource-constrained environments.
3. OpenWrt-based Routers
OpenWrt is an open-source Linux distribution specifically designed for embedded devices, including routers. By installing OpenWrt on a compatible router, users can enable SSH remote access for their IoT network, enhancing both security and functionality.
Advantages of Using SSH Remote IoT Devices
Implementing SSH remote IoT devices brings numerous benefits, both for individuals and organizations. Let's explore these advantages in greater detail:
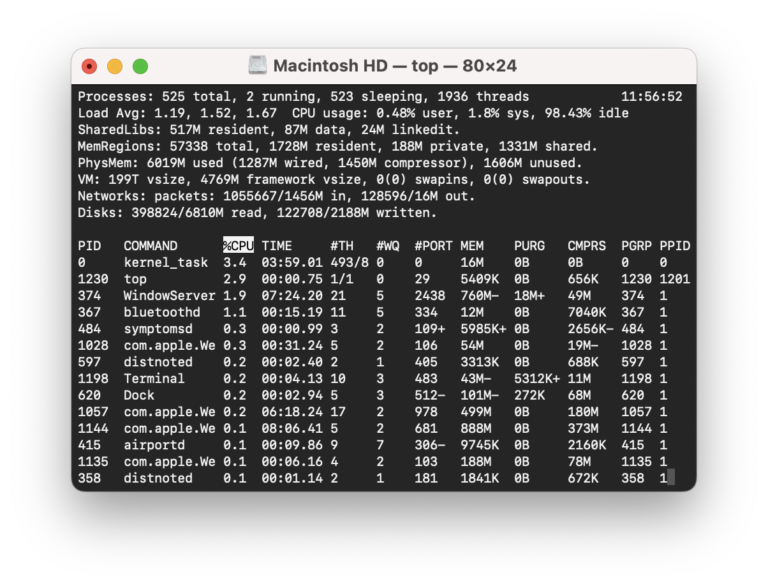
Boosted Operational Efficiency
With SSH remote access, you can effortlessly manage and monitor your IoT devices from anywhere, streamlining your workflow and minimizing downtime. This capability allows for more efficient resource allocation and faster issue resolution.
Enhanced Security Protocols
SSH's advanced encryption and authentication mechanisms protect your IoT devices from unauthorized access and potential cyber threats. This level of security ensures the integrity and confidentiality of your data, providing peace of mind.
Cost Reduction
Free SSH remote IoT devices eliminate the need for expensive proprietary solutions, allowing you to allocate resources more strategically. By leveraging open-source technologies, you can achieve significant cost savings without compromising on quality.
Important Security Considerations
While SSH offers robust security features, it's essential to implement best practices to safeguard your IoT devices fully:
Implement Strong Passwords and Key-Based Authentication
Avoid using weak passwords and opt for SSH key-based authentication to enhance security. Strong authentication methods significantly reduce the risk of unauthorized access and data breaches.
Keep Software Updated
Regularly update your SSH server and client software to protect against potential vulnerabilities. Staying current with the latest security patches ensures that your devices remain protected against emerging threats.
Limit Access to Trusted Sources
Restrict SSH access to trusted IP addresses and disable root login to minimize risks. By controlling access permissions, you can create a more secure environment for your IoT devices.
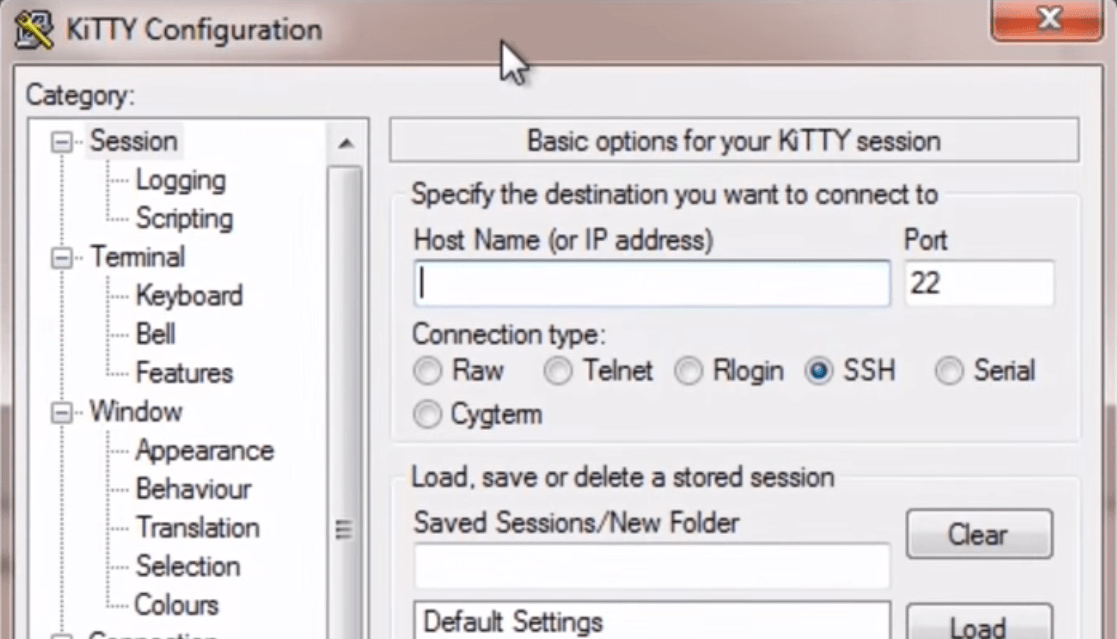
Step-by-Step Guide to Setting Up an SSH Remote IoT Device
Configuring an SSH remote IoT device involves a series of straightforward steps:
Step 1: Install the SSH Server
Depending on your device, you may need to install an SSH server. For instance, on a Raspberry Pi, you can enable SSH through the Raspberry Pi Configuration tool, making the process simple and accessible for users of all skill levels.
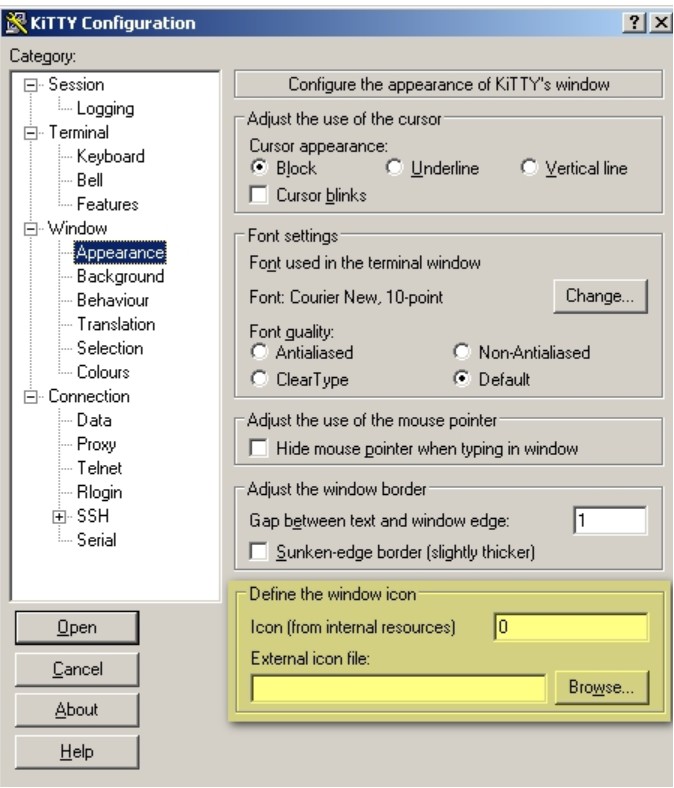
Step 2: Configure Authentication Settings
Set up SSH key-based authentication to enhance security and eliminate the need for passwords. This method provides a more secure and convenient way to access your IoT devices remotely.
Step 3: Test the Connection
Use an SSH client, such as PuTTY or OpenSSH, to connect to your device and verify the setup. Testing the connection ensures that everything is functioning correctly and allows you to address any issues promptly.
Comparing Popular SSH Remote IoT Devices
Selecting the right SSH remote IoT device depends on your specific needs and preferences. Below is a comparison of some popular options:
| Device | Price | Features | Compatibility |
|---|---|---|---|
| Raspberry Pi | Free SSH | Highly customizable, supports multiple protocols | Linux, Windows, macOS |
| ESP32 | Free SSH | Low power consumption, built-in Wi-Fi and Bluetooth | Arduino, MicroPython |
| OpenWrt Router | Free SSH | Advanced networking features, open-source | Compatible routers |
Resolving Common Issues with SSH Remote IoT Devices
Even with a well-configured SSH remote IoT device, you may encounter challenges. Below are some common problems and their solutions:
Connection Issues
Ensure the SSH service is running and the firewall is not blocking the connection. Verifying these settings can resolve connection issues and ensure smooth communication between devices.
Authentication Errors
Double-check your SSH keys and passwords, and verify the server configuration. Ensuring proper authentication settings helps prevent access issues and enhances security.
Slow Performance
Optimize your network settings and consider using compression to improve performance. Streamlining your network setup can enhance the speed and reliability of your SSH connections.
The Future of SSH Remote IoT Devices
As the IoT ecosystem continues to grow, the importance of SSH remote IoT devices will only increase. Future advancements in encryption, authentication, and automation technologies will further enhance the capabilities of these devices, making them indispensable for modern connectivity needs. Staying informed about these developments will help you make the most of SSH remote IoT solutions.
Final Thoughts
To summarize, the best free SSH remote IoT device options provide a secure, efficient, and cost-effective solution for managing your IoT infrastructure. By understanding the features, benefits, and security considerations associated with these devices, you can make an informed decision that aligns with your specific requirements.
We encourage you to share your thoughts and experiences in the comments section below. Feel free to explore other articles on our site for additional insights into the world of IoT and remote access technologies. Stay ahead of the curve by leveraging the power of SSH remote IoT devices today!