Mastering RemoteIoT VPC SSH: A Comprehensive Guide
In today's highly interconnected digital environment, managing remote IoT (Internet of Things) devices through a Virtual Private Cloud (VPC) using Secure Shell (SSH) has become an essential practice for businesses and developers. As the number of connected devices continues to grow exponentially, ensuring secure and reliable communication between them is more critical than ever. RemoteIoT VPC SSH not only fortifies cybersecurity but also enables seamless and efficient remote access to IoT ecosystems.
As cloud-based infrastructures become increasingly integral to modern operations, understanding how to configure and manage remote IoT devices via VPC SSH is no longer optional—it’s a necessity. This guide will explore the complexities of RemoteIoT VPC SSH, offering actionable insights and practical advice tailored to both beginners and seasoned professionals.
Whether you're a network administrator, IT professional, or simply someone eager to deepen your knowledge of secure IoT connections, this article will equip you with the tools and information needed to achieve your goals. Let’s dive into the world of RemoteIoT VPC SSH and unlock its full potential.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
Table of Contents
- Exploring RemoteIoT VPC SSH
- Understanding Virtual Private Cloud (VPC)
- Overview of Secure Shell (SSH)
- The Importance of RemoteIoT Architecture
- Enhancing Security for RemoteIoT VPC SSH
- Configuring RemoteIoT VPC SSH Step-by-Step
- Resolving Common Challenges
- Optimizing Performance for RemoteIoT VPC SSH
- Real-World Applications of RemoteIoT VPC SSH
- Future Directions in RemoteIoT VPC SSH
Exploring RemoteIoT VPC SSH
RemoteIoT VPC SSH represents a cutting-edge approach to managing IoT devices securely over the internet. By combining the robust security of Virtual Private Clouds with the encrypted communication capabilities of Secure Shell protocols, organizations can protect their IoT ecosystems from unauthorized access and potential cyber threats.
Why RemoteIoT VPC SSH is Essential
In the age of widespread IoT adoption, traditional security measures often prove insufficient. RemoteIoT VPC SSH addresses these limitations by establishing an encrypted communication channel, ensuring the protection of sensitive data and operations. Its key advantages include:
- Enhanced Security: Advanced encryption safeguards data during transmission.
- Scalability: Easily accommodate expanding IoT fleets without compromising performance.
- Centralized Control: Streamline the management of remote devices from a single, secure interface.
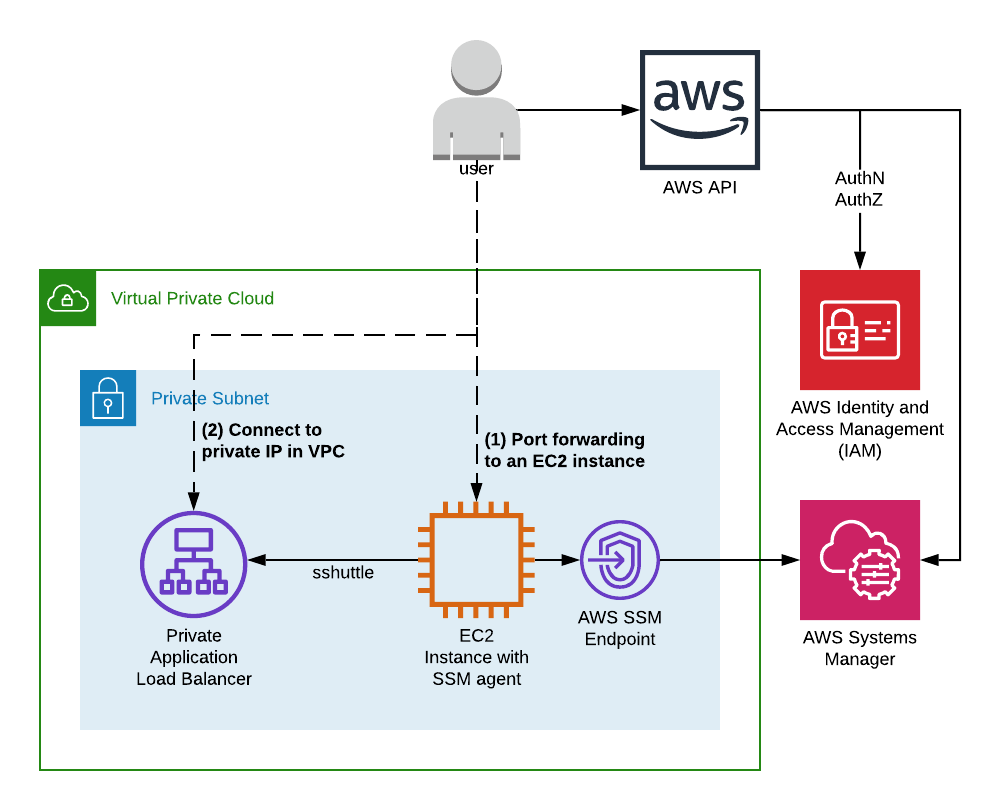
Understanding Virtual Private Cloud (VPC)
A Virtual Private Cloud (VPC) functions as a secure, isolated segment within a public cloud environment, providing users with enhanced control over their resources. It serves as the backbone of RemoteIoT VPC SSH setups, enabling secure and efficient management of IoT devices.
Key Components of a VPC
VPCs comprise several critical components, including subnets, routing tables, and security groups, all of which work together to create a secure and functional network environment. These elements ensure that only authorized traffic is allowed, minimizing the risk of unauthorized access.
Overview of Secure Shell (SSH)
Secure Shell (SSH) is a cryptographic protocol designed to secure communications over untrusted networks. When integrated with VPC, SSH becomes an indispensable tool for remotely managing IoT devices with confidence and reliability.
How SSH Ensures Secure Communication
SSH operates by establishing an encrypted connection between a client and server, ensuring that all transmitted data remains confidential and tamper-proof. This process involves robust authentication methods, such as passwords or public key cryptography, to verify the identity of users and devices.
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
The Importance of RemoteIoT Architecture
The architecture of RemoteIoT systems built on VPC SSH incorporates multiple layers of security and redundancy to ensure reliability and resilience. Understanding this architecture is vital for designing and implementing effective solutions that meet the demands of modern IoT ecosystems.
Key Components of RemoteIoT Architecture
- Gateways: Facilitate communication between IoT devices and the cloud.
- Cloud-Based Data Processing: Handle data storage and analysis in real-time.
- Monitoring Platforms: Provide insights into device performance and system health.
Enhancing Security for RemoteIoT VPC SSH
Implementing robust security measures is paramount when working with RemoteIoT VPC SSH. Below are some best practices to help fortify your system against potential threats:
- Use Strong Authentication: Employ unique passwords or SSH keys to verify user identities.
- Regular Updates: Keep software and firmware up to date to address known vulnerabilities.
- Restrict Access: Limit system access to authorized personnel only, reducing the risk of unauthorized entry.
Configuring RemoteIoT VPC SSH Step-by-Step
Setting up RemoteIoT VPC SSH involves several critical steps, each contributing to the creation of a secure and functional environment. Follow this step-by-step guide to ensure a smooth configuration process.
Step 1: Establish Your VPC
Create a VPC within your cloud provider's console, ensuring that all necessary subnets, routing tables, and security groups are properly configured to meet your specific requirements.
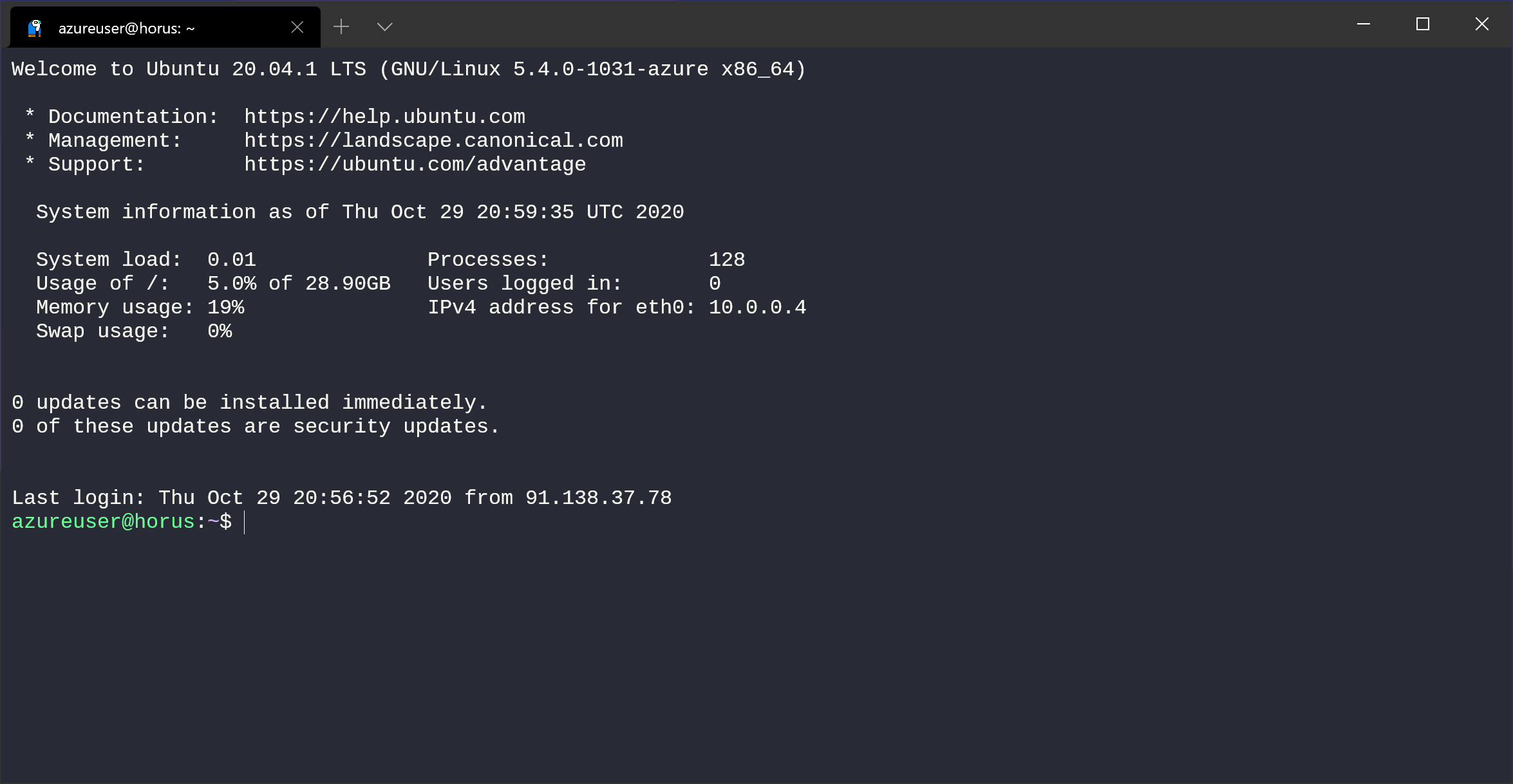
Step 2: Configure SSH Access
Generate SSH keys and establish appropriate rules to allow secure access to your IoT devices. This step ensures that only authorized users can interact with your system.
Resolving Common Challenges
Encountering issues during setup or operation is not uncommon. Below are some tips for addressing and resolving common problems:
- Firewall Settings: Verify that firewall configurations do not restrict necessary traffic.
- SSH Key Verification: Confirm the validity of SSH key pairs and ensure proper permissions are set.
- Log Analysis: Consult system logs for detailed error information to identify and resolve issues efficiently.
Optimizing Performance for RemoteIoT VPC SSH
To maximize the performance of your RemoteIoT VPC SSH setup, consider implementing the following strategies:
- Network Optimization: Fine-tune network configurations to minimize latency and improve data transfer speeds.
- Load Balancing: Distribute traffic effectively across multiple servers to enhance system responsiveness.
- Resource Monitoring: Regularly monitor system resources to detect and address potential bottlenecks proactively.
Real-World Applications of RemoteIoT VPC SSH
RemoteIoT VPC SSH finds practical applications across various industries, driving innovation and efficiency in numerous domains. Some notable examples include:
- Smart Manufacturing: Enable real-time monitoring and control of production lines for increased productivity.
- Smart Cities: Manage urban infrastructure, such as traffic systems and energy grids, with precision and efficiency.
- Healthcare: Facilitate remote monitoring of patient health metrics, enhancing care delivery and patient outcomes.
Future Directions in RemoteIoT VPC SSH
As technology continues to advance, the capabilities and applications of RemoteIoT VPC SSH are expected to expand significantly. Some emerging trends to watch include:
- AI-Driven Security: Leverage artificial intelligence to detect and respond to threats in real-time.
- Quantum Cryptography: Explore ultra-secure communication methods using quantum encryption techniques.
- Edge Computing Integration: Enhance processing speed and efficiency by incorporating edge computing into IoT ecosystems.
Conclusion
RemoteIoT VPC SSH provides a powerful solution for securely managing IoT devices in today's interconnected world. By mastering its architecture, adhering to best practices, and staying informed about future trends, you can unlock its full potential to drive innovation and efficiency within your organization.
We invite you to share your thoughts and experiences with RemoteIoT VPC SSH in the comments section below. Additionally, explore other articles on our site for further insights into cutting-edge technologies shaping the future of cybersecurity and IoT management.
References:
- Amazon Web Services. (n.d.). What is a Virtual Private Cloud? Retrieved from [AWS Documentation](https://aws.amazon.com/vpc/)
- OpenSSH. (n.d.). About SSH. Retrieved from [OpenSSH Website](https://www.openssh.com/)