Exploring Free RemoteIoT SSH Services: A Comprehensive Guide
In the modern era of digital innovation, identifying reliable free RemoteIoT SSH services has become crucial for both individuals and businesses. Secure Shell (SSH) tunnels play a pivotal role in enabling remote access, encrypting data, and fostering secure communication between devices. Whether you're a tech enthusiast or a small business owner, understanding how to harness the potential of free RemoteIoT SSH services can significantly boost your productivity and enhance security. This detailed guide will walk you through everything you need to know about RemoteIoT SSH and its advantages.
As the Internet of Things (IoT) continues to expand exponentially, the demand for secure remote access solutions has skyrocketed. Unfortunately, not everyone can afford premium services. This is where free RemoteIoT SSH services step in, offering a cost-effective way to establish encrypted connections without compromising on security. These services provide an accessible solution for secure data transmission and remote device management.
This article will delve into the essential aspects of RemoteIoT SSH, including its benefits, top free services, associated risks, and best practices for optimal usage. By the end, you'll have a comprehensive understanding of how to integrate free RemoteIoT SSH services into your workflow effectively.
Read also:What Does Obsidian Kingdom Mean Unveiling The Mysteries Of The Name
Table of Contents
- Introduction to RemoteIoT SSH
- Why Choose RemoteIoT SSH?
- Top Free RemoteIoT SSH Services
- Benefits of Using RemoteIoT SSH
- Risks Associated with Free RemoteIoT SSH
- Best Practices for Using RemoteIoT SSH
- How to Set Up RemoteIoT SSH
- Comparison of RemoteIoT SSH Services
- Troubleshooting Common Issues
- Conclusion and Call to Action
Understanding RemoteIoT SSH
RemoteIoT SSH (Secure Shell) is a robust protocol designed to facilitate secure communication between devices, even over unsecured networks. By encrypting data transmitted between the client and server, RemoteIoT SSH ensures that sensitive information remains safeguarded from unauthorized access. This technology is indispensable for remote device management, secure file transfers, and encrypted communication within IoT ecosystems.
What Exactly is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that enables secure data communication, remote command execution, and other network services. It employs strong authentication and encrypted data communications to protect the security and integrity of both the server and the client. SSH is widely regarded as one of the most reliable tools for secure data transmission in today's digital landscape.
Why is RemoteIoT SSH Essential?
As the Internet of Things continues to evolve, the importance of secure remote access cannot be overstated. RemoteIoT SSH ensures that IoT devices connected to the network can be managed securely, significantly reducing the risk of cyberattacks and unauthorized access. Its ability to provide end-to-end encryption makes it an indispensable tool for safeguarding sensitive data in IoT environments.
The Advantages of Choosing RemoteIoT SSH
Selecting RemoteIoT SSH for your IoT needs offers numerous benefits, particularly for individuals and small businesses operating within budget constraints. Below are some compelling reasons to consider this technology:
- Uncompromised Security: SSH employs end-to-end encryption, ensuring all data transmitted between devices remains secure from potential cyber threats.
- Global Accessibility: With SSH, you can manage IoT devices remotely from any location worldwide, as long as you have an active internet connection.
- Cost Efficiency: Free RemoteIoT SSH services provide secure connectivity without the financial burden of expensive proprietary solutions.
- Versatility: SSH is compatible with various operating systems and devices, making it an adaptable solution for diverse IoT environments.
Top Free RemoteIoT SSH Services to Consider
Several free RemoteIoT SSH services are available, each offering unique features and benefits. Below is a list of some of the top options:
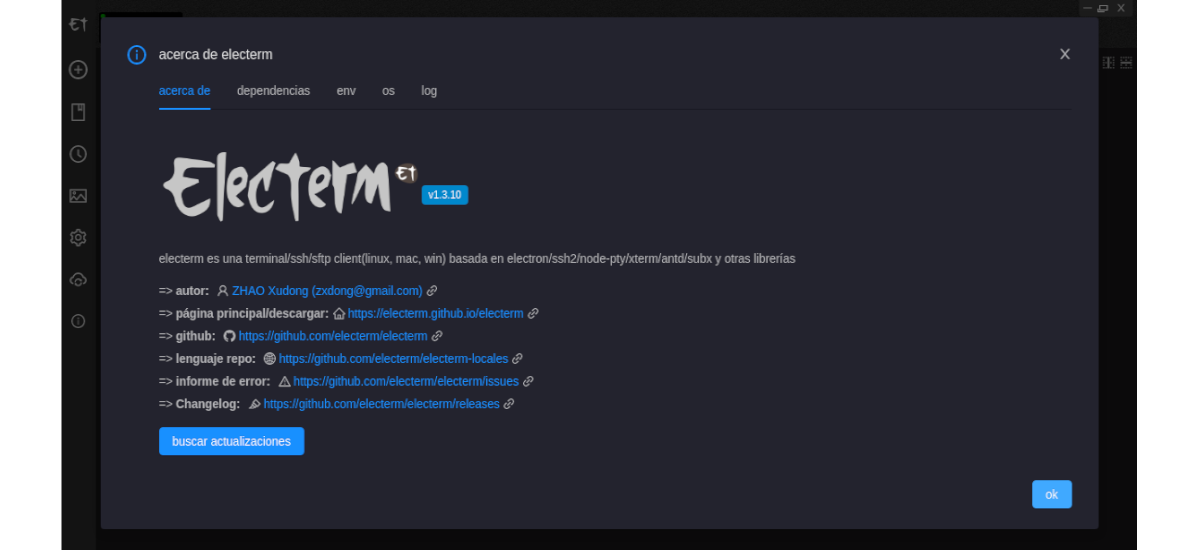
1. Ngrok
Ngrok is a widely-used tool for creating secure tunnels to localhost. It allows users to expose local servers to the internet, making it an excellent choice for testing and development purposes. Its ease of use and reliability make it a popular choice among developers and tech enthusiasts.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
2. Pagekite
Pagekite offers free SSH tunneling services that enable users to access their local servers from anywhere. It supports multiple protocols, including HTTP, HTTPS, and SSH, providing flexibility and customization options for users with varying needs.
3. LocalTunnel
LocalTunnel is a straightforward and user-friendly tool for creating temporary public URLs for local servers. Its simplicity and speed make it ideal for quick testing and debugging sessions, ensuring efficient workflows for developers and IoT professionals.
Key Benefits of Utilizing RemoteIoT SSH
Using RemoteIoT SSH provides numerous advantages, including:
- Enhanced Data Protection: SSH encryption ensures that sensitive information remains shielded from potential cyber threats, safeguarding your IoT ecosystem.
- Increased Operational Efficiency: With remote access capabilities, you can manage IoT devices effortlessly from any location, streamlining your workflow and boosting productivity.
- Financial Savings: Free RemoteIoT SSH services eliminate the need for costly proprietary solutions, allowing you to allocate resources more effectively.
- Scalability: SSH is easily scalable, enabling it to accommodate growing IoT networks as your business expands, ensuring long-term viability.
Potential Risks of Free RemoteIoT SSH Services
While free RemoteIoT SSH services offer numerous benefits, it's essential to be aware of potential risks:
- Security Vulnerabilities: Free services may not provide the same level of security as paid solutions, leaving your IoT devices susceptible to attacks.
- Reliability Concerns: Free services might experience downtime or performance issues, impacting your ability to access IoT devices when needed.
- Privacy Issues: Some free services may collect and utilize your data for advertising or other purposes, raising privacy concerns that need to be addressed.
Optimizing Your RemoteIoT SSH Experience
To maximize the benefits of RemoteIoT SSH and minimize risks, consider following these best practices:
- Implement Strong Passwords: Ensure all SSH accounts are protected with strong, unique passwords to prevent unauthorized access and enhance security.
- Enable Two-Factor Authentication: Add an additional layer of security by enabling two-factor authentication for SSH access, further safeguarding your IoT devices.
- Regularly Update Software: Keep your SSH clients and servers updated with the latest security patches to protect against vulnerabilities and potential threats.
- Monitor Activity Logs: Regularly review SSH activity logs to detect any suspicious behavior and address potential security breaches promptly.
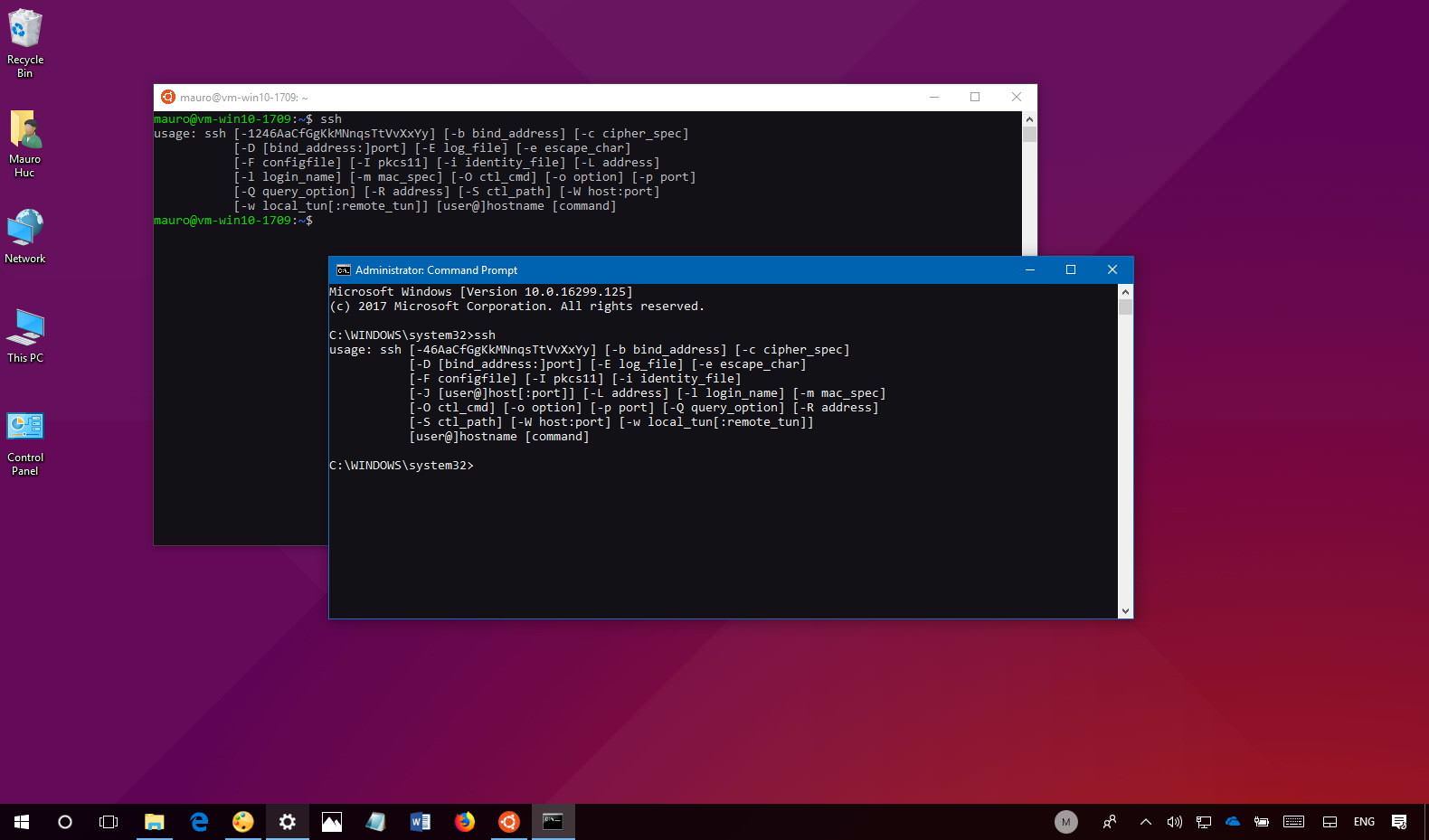
A Step-by-Step Guide to Setting Up RemoteIoT SSH
Setting up RemoteIoT SSH is a straightforward process that can be accomplished in a few simple steps:
- Install an SSH client on your local machine, such as PuTTY for Windows or OpenSSH for Linux, ensuring compatibility with your operating system.
- Obtain the IP address and port number of the remote server you wish to connect to, as these details are essential for establishing a secure connection.
- Enter the server details into the SSH client and authenticate using your credentials, ensuring secure access to the remote server.
- Once connected, you can execute commands, manage files, and perform various tasks securely, enhancing your IoT management capabilities.
Comparing Popular RemoteIoT SSH Services
When selecting a RemoteIoT SSH service, comparing the features and benefits of each option is crucial. Below is a comparison of some popular services:
| Service | Features | Advantages | Drawbacks |
|---|---|---|---|
| Ngrok | Tunneling, HTTPS support | Easy to use, reliable | Free tier limitations |
| Pagekite | Multiple protocols, custom domains | Flexible, customizable | Complex setup process |
| LocalTunnel | Quick setup, temporary URLs | Simple, fast | Limited functionality for advanced use cases |
Addressing Common Issues with RemoteIoT SSH
When using RemoteIoT SSH, you may encounter certain challenges. Below are some tips for troubleshooting common issues:
- Connection Refused: Verify that the SSH server is operational and the required port is open to ensure a successful connection.
- Authentication Failed: Double-check your username and password, or consider resetting them to resolve authentication issues.
- Timeout Errors: Check your internet connection and attempt reconnecting to resolve any connectivity-related issues.
Final Thoughts and Next Steps
In summary, discovering the best free RemoteIoT SSH service can significantly enhance your ability to manage IoT devices securely and efficiently. By understanding the benefits, risks, and best practices associated with RemoteIoT SSH, you can make an informed decision about which service aligns best with your needs. We encourage you to share your thoughts and experiences in the comments section below. Have you experimented with any of the services mentioned in this article? Let us know which one has worked best for you. Additionally, feel free to explore other articles on our site for further insights into IoT and cybersecurity trends.