Mastering Secure Shell (SSH) For IoT Devices: A Comprehensive Guide
Secure Shell (SSH) has emerged as an essential tool for managing and securing IoT devices in today's technology-driven world. As the Internet of Things (IoT) continues to expand, understanding how to leverage SSH for remote access has become indispensable for developers, engineers, and IT professionals. This tutorial will walk you through the core principles of SSH RemoteIoT, enabling you to confidently manage your IoT devices with enhanced security.
Regardless of whether you're a beginner or an experienced professional, this guide offers step-by-step instructions and expert insights to help you unlock the full potential of SSH for IoT applications. By the end of this tutorial, you'll have the knowledge to establish secure connections to remote devices, execute commands, and maintain robust network security.
This article is designed to be both comprehensive and accessible, providing practical examples and actionable tips. Let’s delve into the world of SSH RemoteIoT and uncover how it can transform the way you interact with your IoT devices.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
Table of Contents
- Understanding Secure Shell (SSH)
- Overview of SSH RemoteIoT
- Setting Up SSH
- Connecting to Remote Devices
- Securing Your SSH Connection
- Common SSH Commands
- Troubleshooting SSH Issues
- Advanced SSH Features
- Best Practices for SSH RemoteIoT
- Conclusion and Next Steps
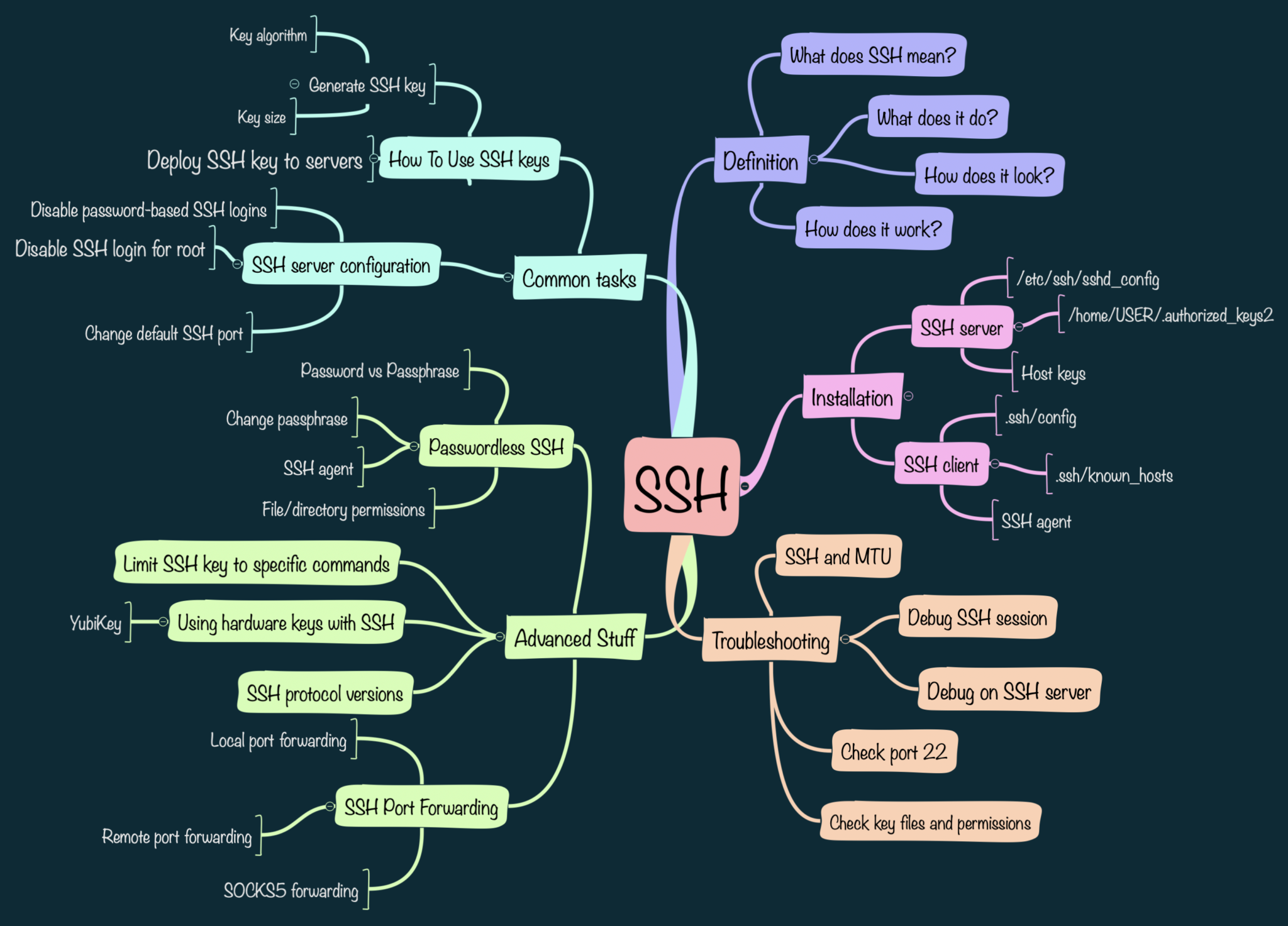
Understanding Secure Shell (SSH)
Secure Shell (SSH) is a cryptographic network protocol designed to facilitate secure communication between devices over potentially insecure networks. It provides a secure channel for remote administration, file transfer, and command execution, ensuring confidentiality, integrity, and authentication through encryption and public-key cryptography. SSH has become a cornerstone for managing devices across industries, including the rapidly evolving Internet of Things (IoT).
For IoT devices, SSH plays a pivotal role in enabling secure remote access. As IoT ecosystems grow in complexity, the ability to manage devices remotely becomes increasingly vital. SSH offers a dependable solution for maintaining control over IoT networks while safeguarding sensitive data, making it an indispensable tool for modern-day IT professionals.
Overview of SSH RemoteIoT
SSH RemoteIoT refers to the strategic application of SSH protocols tailored specifically for IoT devices. This approach empowers users to manage and interact with IoT devices securely from remote locations. By leveraging SSH, IoT administrators can execute commands, transfer files, and monitor device performance without compromising security.
Industry projections indicate that the number of IoT devices will surpass 25 billion by 2025, as reported by Gartner. With this rapid expansion, ensuring secure communication between devices has never been more critical. SSH RemoteIoT equips professionals with the tools necessary to meet this challenge, making it an essential skill for anyone working in the IoT domain.
Setting Up SSH
Installing SSH
Before utilizing SSH for IoT devices, it is crucial to install the SSH client and server software. Fortunately, many Linux distributions come with SSH pre-installed. However, if it is not present, you can easily install it using the package manager. Below are installation instructions for popular Linux distributions:
- For Ubuntu/Debian: Use the command
sudo apt-get install ssh. - For CentOS/RHEL: Use the command
sudo yum install ssh.
Configuring SSH
Once installed, configuring the SSH server to align with your specific requirements is the next step. The primary configuration file for SSH is located at /etc/ssh/sshd_config. Key parameters to adjust include:
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
- Port: Modify the default port (22) to a custom port for enhanced security.
- PasswordAuthentication: Disable password authentication to mitigate brute-force attacks.
- PermitRootLogin: Disable root login to bolster security.
Connecting to Remote Devices
Establishing a connection to remote IoT devices via SSH is a straightforward process. Open your terminal or command prompt and execute the following command:
ssh username@ip_address
Substitute "username" with the appropriate user account and "ip_address" with the IP address of the remote device. If you're utilizing a custom port, include the port number with the -p flag:
ssh -p custom_port username@ip_address
Securing Your SSH Connection
Security remains paramount when managing IoT devices remotely. Below are some best practices to fortify your SSH connections:
- Employ strong, unique passwords or implement SSH key-based authentication.
- Enable two-factor authentication (2FA) for an extra layer of security.
- Regularly update your SSH software to address vulnerabilities.
- Monitor login attempts and block suspicious IP addresses.
Common SSH Commands
Becoming familiar with common SSH commands can significantly enhance your workflow. Below are some essential commands for managing IoT devices:
- ssh-copy-id: Facilitates the copying of your SSH public key to a remote server.
- scp: Enables secure copying of files between local and remote devices.
- ssh-keygen: Assists in generating SSH key pairs for authentication.
- ssh -N -L: Allows the creation of an SSH tunnel for port forwarding.
Troubleshooting SSH Issues
Experiencing issues with SSH connections is not uncommon. Below are some frequent problems and their solutions:
- Connection Refused: Ensure the SSH service is operational on the remote device and verify firewall settings.
- Permission Denied: Confirm your credentials and ensure the correct SSH keys are being utilized.
- Timeout Errors: Assess your network connection and ensure the remote device is accessible.
Advanced SSH Features
SSH Tunneling
SSH tunneling facilitates the secure forwarding of traffic between devices. This feature is invaluable for accessing services behind firewalls or encrypting sensitive data. To establish an SSH tunnel, utilize the following command:
ssh -L local_port:destination_host:destination_port username@ssh_server
SSH Key-Based Authentication
SSH key-based authentication serves as a secure alternative to password authentication. It involves generating a pair of public and private keys. To set this up:
- Generate a key pair using
ssh-keygen. - Copy the public key to the remote device using
ssh-copy-id. - Disable password authentication in the SSH configuration file.
Best Practices for SSH RemoteIoT
To fully leverage the advantages of SSH RemoteIoT, consider adhering to the following best practices:
- Conduct regular audits of your SSH configurations to ensure compliance with security standards.
- Restrict access to SSH servers to authorized personnel exclusively.
- Maintain your IoT devices and SSH software with the latest security patches.
- Implement network segmentation to isolate critical devices from the broader network.
Conclusion and Next Steps
In summary, SSH RemoteIoT represents a potent tool for managing IoT devices securely. By following the steps outlined in this tutorial, you can confidently establish, configure, and secure SSH connections for your IoT networks. Always adhere to best practices and remain informed about the latest advancements in SSH technology.
We encourage you to share your thoughts and experiences with SSH RemoteIoT in the comments section below. Additionally, explore our other articles for further insights into IoT security and management. Together, let’s build a safer and more interconnected world!