Securing IoT Networks With P2P SSH On Raspberry Pi
In today's interconnected world, safeguarding communication between devices is critical. The phrase "best securely connect remote IoT P2P SSH Raspberry Pi download" highlights the increasing need for strong security solutions in IoT ecosystems. As remote work and smart home technologies continue to grow, ensuring the security of IoT devices has become a top priority for both individuals and businesses.
As more devices join the Internet of Things (IoT) ecosystem, the risks associated with unauthorized access and cyberattacks rise exponentially. This article explores the most effective methods for securely connecting remote IoT devices using peer-to-peer (P2P) SSH on Raspberry Pi. It provides comprehensive guidance to help protect your network. Additionally, we offer downloadable resources to assist you in implementing these solutions effectively.
By the end of this article, you will have a thorough understanding of how to secure your IoT devices and apply best practices for P2P SSH connections on Raspberry Pi. Let’s explore the tools, techniques, and resources necessary to safeguard your network.
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
Table of Contents
- Introduction to IoT Security
- Raspberry Pi as an IoT Platform
- Understanding P2P SSH
- Securing Remote IoT Connections
- Best Practices for IoT Security
- Tools and Resources
- How to Implement SSH on Raspberry Pi
- Downloading Resources
- Case Studies
- Conclusion
Introduction to IoT Security
The Internet of Things (IoT) has transformed how we interact with technology, offering unprecedented convenience and efficiency. However, this innovation brings challenges, particularly in securing the vast array of interconnected devices. IoT security is the practice of protecting IoT devices and networks from unauthorized access, data breaches, and other cyber threats.
Why IoT Security Matters
IoT devices often handle sensitive information, making them prime targets for cybercriminals. A breach in one device can compromise an entire network, leading to significant financial losses, privacy violations, and even physical harm. To address these risks, it is essential to implement robust security measures that safeguard both data and devices.
- Protect sensitive data from unauthorized access.
- Prevent cyberattacks targeting IoT networks.
- Maintain the integrity and reliability of IoT devices.
Raspberry Pi as an IoT Platform
Raspberry Pi has emerged as a leading choice for IoT projects due to its affordability, versatility, and ease of use. This compact device supports various operating systems and programming languages, enabling developers to design and deploy IoT applications with ease.
Advantages of Using Raspberry Pi for IoT
- Provides a cost-effective solution for IoT projects.
- Supports a wide range of sensors and peripherals.
- Facilitates customization for specific use cases.
By leveraging the capabilities of Raspberry Pi, developers can create secure and efficient IoT solutions tailored to their needs.
Understanding P2P SSH
Peer-to-peer (P2P) SSH is a secure method for establishing connections between devices without relying on a central server. This approach minimizes the risk of single points of failure and reduces the attack surface for potential threats. P2P SSH offers several advantages over traditional methods, making it an ideal choice for securing IoT networks.
Key Features of P2P SSH
- End-to-end encryption ensures secure communication between devices.
- Eliminates the need for centralized servers, reducing complexity.
- Supports robust authentication and authorization mechanisms.
Implementing P2P SSH on Raspberry Pi enhances the security of your IoT network by ensuring that only authorized devices can communicate with each other.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
Securing Remote IoT Connections
Securing remote IoT connections requires a multi-layered approach to safeguard devices and data. This includes implementing strong authentication methods, encrypting communications, and regularly updating systems to address vulnerabilities.
Steps to Secure Remote IoT Connections
- Use strong passwords and enable multi-factor authentication (MFA) for added security.
- Enable encryption for all data transmissions to protect sensitive information.
- Regularly update firmware and software to patch vulnerabilities and stay ahead of emerging threats.
By adhering to these best practices, you can significantly reduce the risk of unauthorized access and ensure the security of your IoT network.
Best Practices for IoT Security
In addition to securing remote connections, adopting comprehensive best practices can enhance the overall security of your IoT ecosystem. These practices focus on device management, network security, and user awareness.
Device Management
- Regularly monitor and manage IoT devices to detect and address potential issues.
- Implement device-specific policies and controls to enforce security standards.
- Isolate IoT devices on a separate network segment to limit exposure.
Network Security
- Deploy firewalls and intrusion detection systems to monitor and block malicious activity.
- Segment your network to minimize the impact of a potential breach.
- Continuously monitor network traffic for suspicious activity and anomalies.
User Awareness
- Educate users about IoT security risks and the importance of adopting secure practices.
- Encourage the use of strong passwords and security protocols to protect devices and data.
- Provide regular training and updates on security best practices to keep users informed.
Tools and Resources
Several tools and resources are available to help you secure your IoT devices and implement P2P SSH on Raspberry Pi. These resources include software libraries, tutorials, and community forums where you can learn from experienced developers.
Recommended Tools
- OpenSSH: A widely used SSH implementation for secure communication.
- Raspberry Pi Documentation: Official documentation for Raspberry Pi projects.
- GitHub: A platform for hosting and collaborating on open-source projects.
These tools provide the foundation for building secure IoT solutions and implementing P2P SSH on Raspberry Pi.
How to Implement SSH on Raspberry Pi
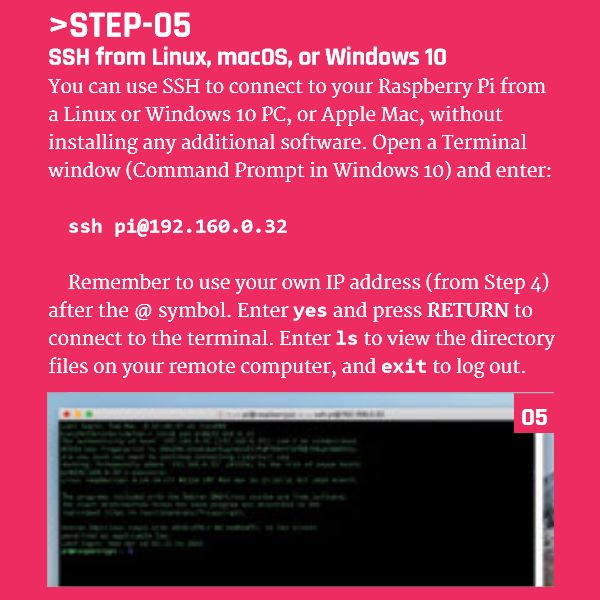
Setting up SSH on Raspberry Pi involves configuring the device to enable secure communication with other devices. Follow these steps to establish a secure SSH connection:
Step-by-Step Guide
- Install the latest version of Raspberry Pi OS on your device.
- Enable SSH in the Raspberry Pi Configuration tool to allow remote access.
- Generate SSH keys for authentication to enhance security.
- Configure firewall rules to allow SSH traffic while blocking unauthorized access.
- Test the connection using a remote SSH client to ensure proper functionality.
By following this guide, you can establish a secure SSH connection between your Raspberry Pi and other devices in your network.
Downloading Resources
We have compiled a list of downloadable resources to assist you in implementing the solutions discussed in this article. These resources include configuration files, scripts, and documentation to help you secure your IoT network.
Download Links
These resources will equip you with the tools and knowledge needed to secure your IoT devices and implement P2P SSH on Raspberry Pi.
Case Studies
Real-world examples demonstrate the effectiveness of IoT security solutions. Below are two case studies showcasing the implementation of secure IoT connections using P2P SSH on Raspberry Pi.
Case Study 1: Smart Home Security
A homeowner implemented P2P SSH on their Raspberry Pi to secure their smart home devices. By enabling end-to-end encryption and multi-factor authentication, they successfully reduced the risk of unauthorized access and ensured the privacy of their data. This solution provided peace of mind while maintaining the convenience of smart home technology.
Case Study 2: Industrial IoT
A manufacturing company used Raspberry Pi to monitor and control their IoT-enabled equipment. By implementing P2P SSH, they achieved secure remote access to their devices, improving operational efficiency and reducing downtime. This approach enhanced the reliability of their IoT infrastructure and minimized the risk of cyberattacks.
Conclusion
Securing remote IoT connections using P2P SSH on Raspberry Pi is a powerful strategy for protecting your network from cyber threats. By following the best practices outlined in this article and utilizing the provided resources, you can ensure the security and reliability of your IoT devices. We encourage you to implement these solutions, share your experiences with the community, and continue exploring IoT security to build a safer and more connected world.