Securing IoT Connections With Raspberry Pi And VPC
In today's highly interconnected world, establishing secure connections for remote IoT devices through a Virtual Private Cloud (VPC) using a Raspberry Pi is more important than ever. As the Internet of Things (IoT) continues to expand, ensuring secure communication and safeguarding sensitive data have become top priorities. This comprehensive guide will walk you through the essential steps to create a robust, secure connection between your IoT devices and a VPC using a Raspberry Pi.
The rapid proliferation of IoT devices has created countless opportunities, but it has also introduced significant challenges, especially in terms of cybersecurity. With billions of devices connected globally, the potential for cyber threats has grown exponentially. Both organizations and individuals must implement robust security measures to protect their data and infrastructure from breaches and unauthorized access.
This article aims to provide a detailed roadmap for securely connecting remote IoT devices to a VPC using a Raspberry Pi. By following the steps outlined here, you can fortify your IoT ecosystem against unauthorized access, data breaches, and other security risks. Let's delve into the specifics of this process and explore how you can enhance your IoT security.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
Table of Contents
- Understanding IoT Security
- Overview of Raspberry Pi
- Understanding VPC Fundamentals
- Steps to Secure IoT Connections
- Encryption Techniques for IoT Communication
- Configuring Firewalls for Enhanced Security
- Setting Up Secure Remote Access
- Ensuring Data Privacy and Regulatory Compliance
- Addressing Common Issues and Troubleshooting
- Conclusion and Next Steps
Understanding IoT Security
The Internet of Things (IoT) has transformed the way we interact with technology, enabling smarter homes, industries, and cities. However, this widespread adoption necessitates stringent security measures to protect IoT devices, networks, and data from unauthorized access and cyber threats. Establishing secure connections between remote IoT devices and a VPC using a Raspberry Pi is one effective way to enhance the security of your IoT infrastructure.
IoT security encompasses safeguarding IoT devices, networks, and data from malicious actors. This involves implementing encryption, firewalls, and secure communication protocols. By integrating a Raspberry Pi into your IoT ecosystem, you can create a secure gateway for your devices to communicate with a VPC. This not only protects your data but also ensures compliance with industry standards and regulations.
According to a report by Gartner, the global number of IoT devices is projected to reach an astonishing 25 billion by 2030. This exponential growth highlights the critical importance of securing IoT devices and ensuring they communicate safely over the internet.
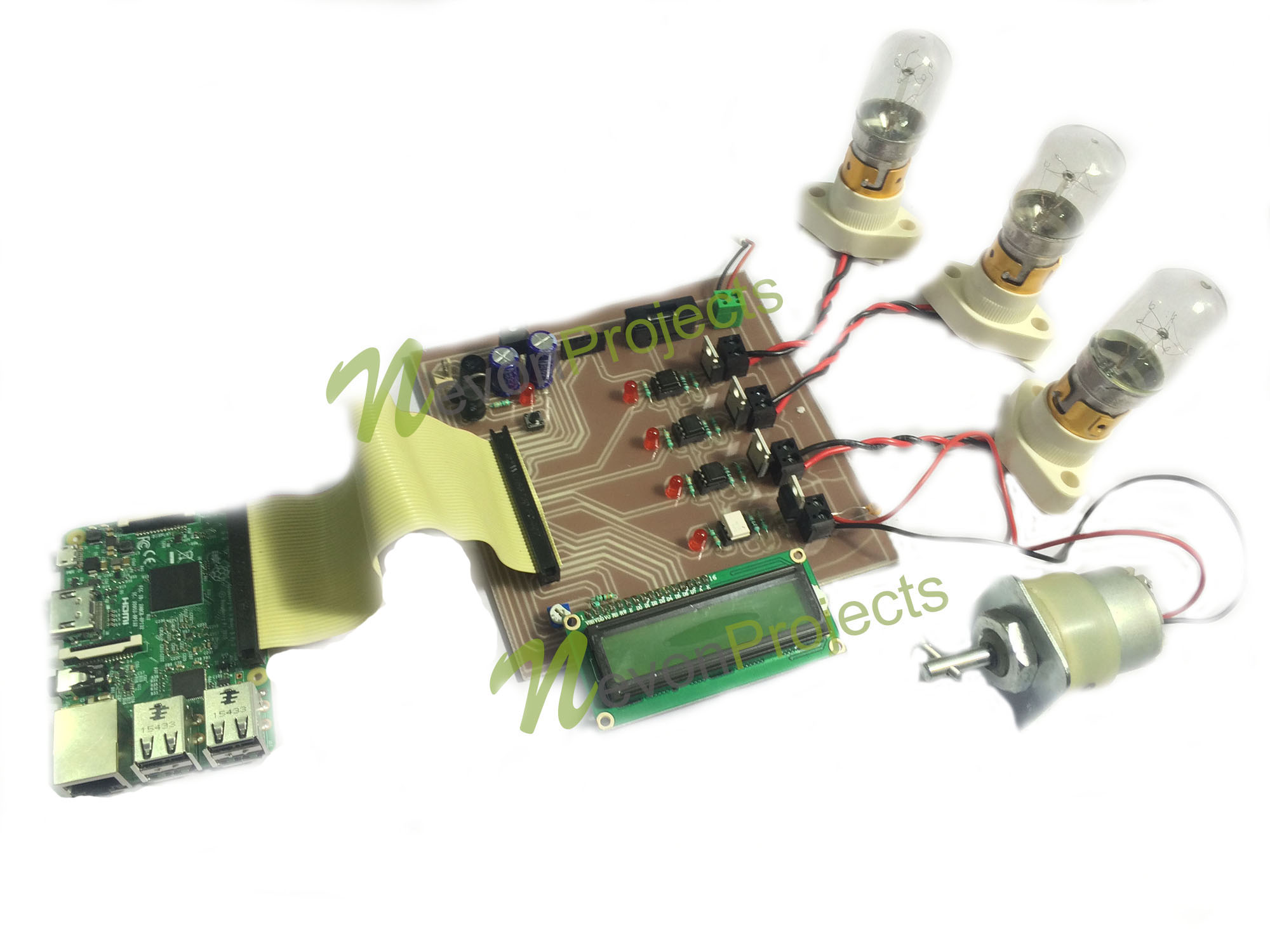
Overview of Raspberry Pi
The Raspberry Pi is a compact, affordable computer that has become a favorite among hobbyists, educators, and professionals alike. Its versatility and ease of use make it an ideal tool for securing IoT connections with a VPC. By leveraging its capabilities, you can establish a secure and reliable gateway for your IoT devices.
Key Features of Raspberry Pi
- Small form factor and energy-efficient design
- Compatibility with multiple operating systems, including Linux
- General-purpose input/output (GPIO) pins for interfacing with external hardware
- Extensive community support and a wealth of resources
In this guide, we will focus on using a Raspberry Pi to create a secure gateway for your IoT devices. Proper configuration ensures that all communication between your devices and the VPC remains encrypted and secure, minimizing the risk of data breaches.
Understanding VPC Fundamentals
A Virtual Private Cloud (VPC) is a logically isolated segment of a cloud environment where you can securely deploy your resources. It provides a private network for your applications and services, shielding them from unauthorized access. By connecting your IoT devices to a VPC through a Raspberry Pi, you create a secure tunnel that encrypts all data transmitted between the devices and the cloud.
Read also:What Is The Jamaican Slang For Friend Or Bro Exploring The Vibrant Language Of Jamaica
When you establish a secure connection between your IoT devices and a VPC, you are essentially creating a protected pathway for communication. This ensures that sensitive data remains encrypted and protected from potential threats, such as cyberattacks and unauthorized access.
Benefits of Using a VPC
- Enhanced security through network isolation
- Flexibility in configuring network settings to meet your specific needs
- Scalability to accommodate the growth of your IoT ecosystem
- Seamless integration with other cloud services for comprehensive solutions
Steps to Secure IoT Connections
Securing remote IoT connections with a VPC using a Raspberry Pi involves several key steps. Follow the detailed instructions below to ensure a secure and reliable setup.
Step 1: Set Up Your Raspberry Pi
Begin by installing an appropriate operating system on your Raspberry Pi. Raspbian, a Linux-based distribution specifically designed for Raspberry Pi, is a popular choice due to its user-friendly interface and extensive software library. Ensure that your Raspberry Pi is updated with the latest software and security patches.
Step 2: Configure Network Settings
Ensure that your Raspberry Pi is connected to the internet and properly configured to communicate with your IoT devices. Assign static IP addresses to simplify the setup process and improve network stability. Additionally, configure your network settings to prioritize security and efficiency.
Step 3: Establish a Secure Tunnel
Create a secure connection between your Raspberry Pi and the VPC using a tunneling protocol such as SSH or OpenVPN. These protocols encrypt all data transmitted between your IoT devices and the cloud, ensuring that your communication remains private and secure. Configure the tunnel settings carefully to maximize security and performance.
Encryption Techniques for IoT Communication
Encryption is a fundamental component of securing IoT connections. It involves transforming plaintext data into ciphertext to prevent unauthorized access. By implementing robust encryption protocols, you can safeguard your IoT devices and ensure secure communication with the VPC.
Common Encryption Protocols
- Transport Layer Security (TLS): A widely used protocol for securing communication over the internet
- Advanced Encryption Standard (AES): A symmetric encryption algorithm known for its strength and efficiency
- Secure Sockets Layer (SSL): An older protocol that has largely been replaced by TLS but is still relevant in some contexts
In addition to these protocols, consider using digital certificates to authenticate devices and prevent man-in-the-middle attacks. This adds an extra layer of security to your IoT ecosystem and ensures that only authorized devices can access your network.
Configuring Firewalls for Enhanced Security
A firewall is a critical network security system that monitors and controls incoming and outgoing traffic. Properly configuring a firewall is essential for securing remote IoT connections with a VPC using a Raspberry Pi. By implementing best practices, you can significantly reduce the risk of unauthorized access to your devices and network.
Best Practices for Firewall Configuration
- Block all incoming traffic by default and only allow necessary ports and services
- Regularly update firewall rules to address emerging threats and vulnerabilities
- Monitor firewall logs for suspicious activity and take corrective action as needed
- Implement advanced features, such as intrusion detection and prevention systems, for enhanced security
By following these best practices, you can create a robust firewall configuration that protects your IoT devices and VPC from potential threats.
Setting Up Secure Remote Access
Remote access allows you to manage your IoT devices and VPC from anywhere in the world. To secure remote connections with a Raspberry Pi, consider using a reliable remote access solution such as SSH or a remote desktop protocol. These tools provide secure and efficient access to your devices, enabling you to monitor and manage your IoT ecosystem from a distance.
Securing Remote Access
- Use strong passwords and enable two-factor authentication to enhance security
- Limit access to trusted IP addresses and restrict unauthorized connections
- Regularly update software and firmware to address vulnerabilities and improve security
By implementing these security measures, you can ensure that your remote access is secure and protected from potential threats, such as unauthorized access and cyberattacks.
Ensuring Data Privacy and Regulatory Compliance
Data privacy is a crucial aspect of securing IoT connections with a Raspberry Pi and VPC. Organizations must adhere to relevant regulations, such as GDPR and HIPAA, to protect sensitive data and maintain trust with their users. By implementing best practices for data privacy, you can ensure compliance with legal requirements and safeguard your IoT ecosystem.
Data Privacy Best Practices
- Encrypt all sensitive data both in transit and at rest to prevent unauthorized access
- Implement access controls to restrict data access to authorized personnel only
- Regularly audit data handling practices to identify and address potential vulnerabilities
- Provide comprehensive training to employees on data privacy and security best practices
By following these best practices, you can create a secure and compliant IoT ecosystem that protects sensitive information and ensures trust with your users.
Addressing Common Issues and Troubleshooting
Despite careful planning and implementation, issues may arise when securing IoT connections with a Raspberry Pi and VPC. Below are some common problems and their solutions:
Issue 1: Connection Problems
Solution: Verify your network settings and ensure that all devices are properly configured. Restart your Raspberry Pi and attempt to reconnect. If the issue persists, consult the documentation or seek assistance from the Raspberry Pi community.
Issue 2: Firewall Blocking Traffic
Solution: Review your firewall rules and ensure that necessary ports and services are allowed. Update your firewall settings as needed to resolve any connectivity issues. Regularly monitor your firewall logs to identify and address potential problems.
Issue 3: Encryption Errors
Solution: Confirm your encryption settings and ensure that all devices are using the same encryption protocol. Update your software and firmware to address any compatibility issues or vulnerabilities. If the problem persists, consult the documentation or seek technical support.
Conclusion and Next Steps
In conclusion, securing remote IoT connections with a VPC using a Raspberry Pi is a critical component of modern technology implementation. By following the steps outlined in this guide, you can create a secure and reliable connection between your IoT devices and the VPC, protecting your data and infrastructure from potential threats.
We encourage you to take action by implementing these security measures and safeguarding your IoT ecosystem. Share your thoughts or ask questions in the comments below. Additionally, feel free to explore other articles on our website for more information on IoT security and related topics.
Stay informed, stay secure, and continue building a safer digital future for yourself and your organization!