Mastering Secure IoT Connections With P2P SSH On Ubuntu
In today's highly interconnected world, establishing secure connections between remote IoT devices using Peer-to-Peer (P2P) SSH on Ubuntu is vital for safeguarding data privacy and ensuring system integrity. Whether you're a developer, system administrator, or tech enthusiast, understanding how to implement secure connections is essential. This comprehensive guide will walk you through the process step-by-step, providing practical examples, expert advice, and actionable insights.
As the number of connected devices in the Internet of Things (IoT) continues to grow exponentially, ensuring secure communication between these devices has become more critical than ever. This article delves into the methods for establishing secure peer-to-peer (P2P) connections using SSH on Ubuntu. We’ll cover everything from setting up your environment to resolving common issues, giving you a thorough understanding of the subject.
Our primary focus will be on practical implementation while adhering to security best practices. By the end of this guide, you'll have the knowledge and tools to securely connect remote IoT devices using SSH, protecting both your data and infrastructure from potential threats.
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
Table of Contents
- Understanding IoT and SSH
- The Importance of Secure Connections
- Preparing Ubuntu for IoT Deployment
- An Overview of P2P SSH
- Step-by-Step Guide to Secure Connections
- Common Challenges and Solutions
- Best Practices for Enhanced Security
- Troubleshooting Techniques
- Advanced Methods for Securing IoT
- Conclusion and Recommendations
Understanding IoT and SSH
The Internet of Things (IoT) represents a vast network of physical devices equipped with sensors, software, and connectivity, enabling them to exchange data seamlessly. Secure Shell (SSH), a cryptographic network protocol, plays a pivotal role in ensuring secure communication between these devices. By integrating IoT with SSH, you can guarantee that all data transmissions remain private and safeguarded from unauthorized access.
Why Choose SSH for IoT?
SSH is renowned for its robust encryption and authentication mechanisms, making it an ideal choice for securing IoT communications. Below are some key features that make SSH indispensable:
- End-to-End Encryption: Ensures that data remains encrypted during transmission.
- Strong Authentication: Provides reliable methods to verify the identity of devices.
- Protection Against Attacks: Safeguards against man-in-the-middle and other malicious attacks.
The Importance of Secure Connections
IoT devices often handle sensitive information, ranging from personal health records to critical industrial data. A breach in security could result in severe consequences, including data theft, financial losses, or even physical harm. Establishing secure connections using SSH for IoT devices ensures:
- Data Integrity: Protects data from being altered or corrupted during transmission.
- Privacy Protection: Safeguards sensitive information from unauthorized access.
- Regulatory Compliance: Ensures adherence to industry standards and legal requirements.
A report by Gartner predicts that the number of connected devices will surpass 25 billion by 2025. This rapid growth highlights the pressing need for secure communication protocols.
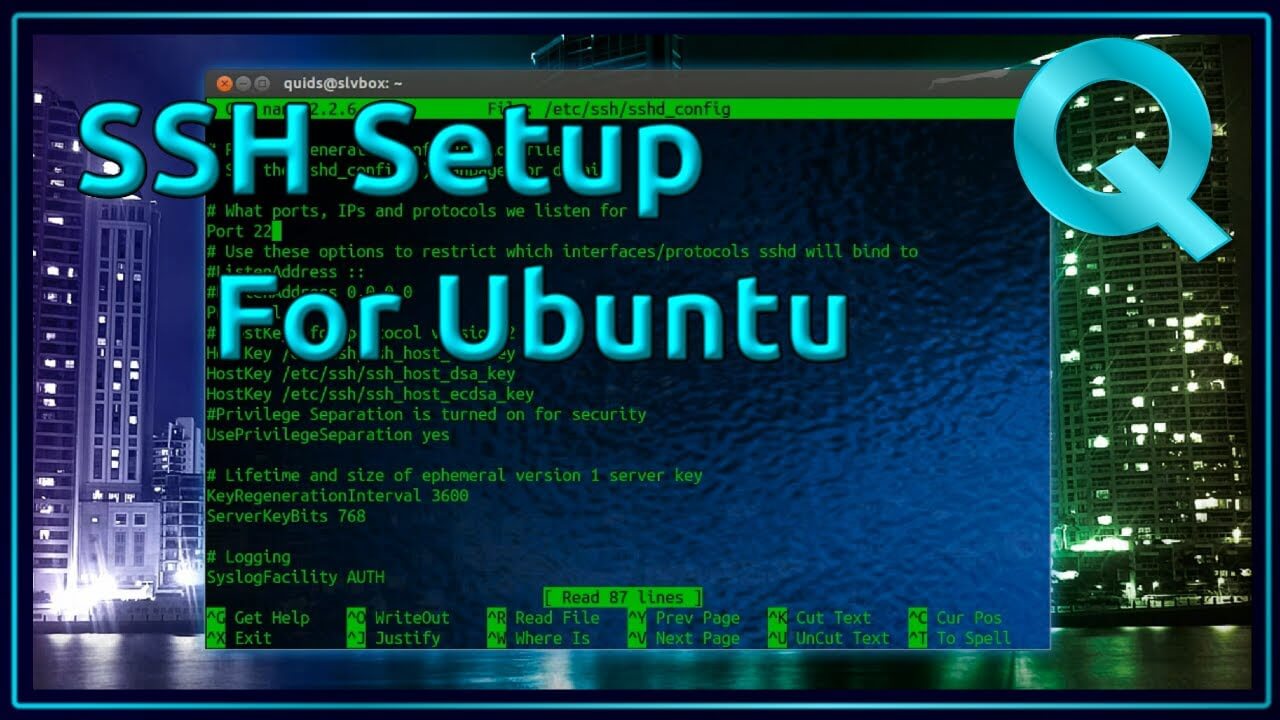
Preparing Ubuntu for IoT Deployment
Ubuntu is a widely adopted Linux distribution favored in IoT applications due to its stability, reliability, and extensive community support. Below are the steps to set up Ubuntu for IoT:
Step 1: Install Ubuntu Server
Start by downloading the latest version of Ubuntu Server from the official website. Follow the detailed installation instructions provided in the documentation to complete the setup.
Read also:What Is The Jamaican Slang For Friend Or Bro Exploring The Vibrant Language Of Jamaica
Step 2: Configure Networking
Ensure your network settings are properly configured. Use the following commands to check and configure your IP address:
ip addr show
sudo nano /etc/netplan/01-netcfg.yaml
Step 3: Install Essential Packages
Install necessary packages for SSH and IoT communication by running the following commands:
sudo apt updatesudo apt install openssh-server
An Overview of P2P SSH
Peer-to-Peer (P2P) SSH enables direct communication between two devices without relying on a central server. This approach not only reduces latency but also enhances security by eliminating intermediary points of failure.
How P2P SSH Works
In a P2P SSH setup, devices establish a direct encrypted connection using public and private keys. The process involves the following steps:
- Generating SSH Keys: Create a pair of cryptographic keys for secure authentication.
- Exchanging Public Keys: Share the public key with the remote device to facilitate secure communication.
- Initiating the Connection: Establish the encrypted connection between the devices.
Step-by-Step Guide to Secure Connections
Follow the steps below to securely connect remote IoT devices using P2P SSH on Ubuntu:
Step 1: Generate SSH Keys
Use the ssh-keygen command to generate SSH keys with enhanced security:
ssh-keygen -t rsa -b 4096
Step 2: Exchange Public Keys
Copy the public key from Device A to Device B using the following command:
ssh-copy-id user@deviceb
Step 3: Initiate the Connection
Connect from Device A to Device B securely using SSH:
ssh user@deviceb
Common Challenges and Solutions
While configuring P2P SSH, you may encounter several common issues. Below are solutions to help you resolve them:
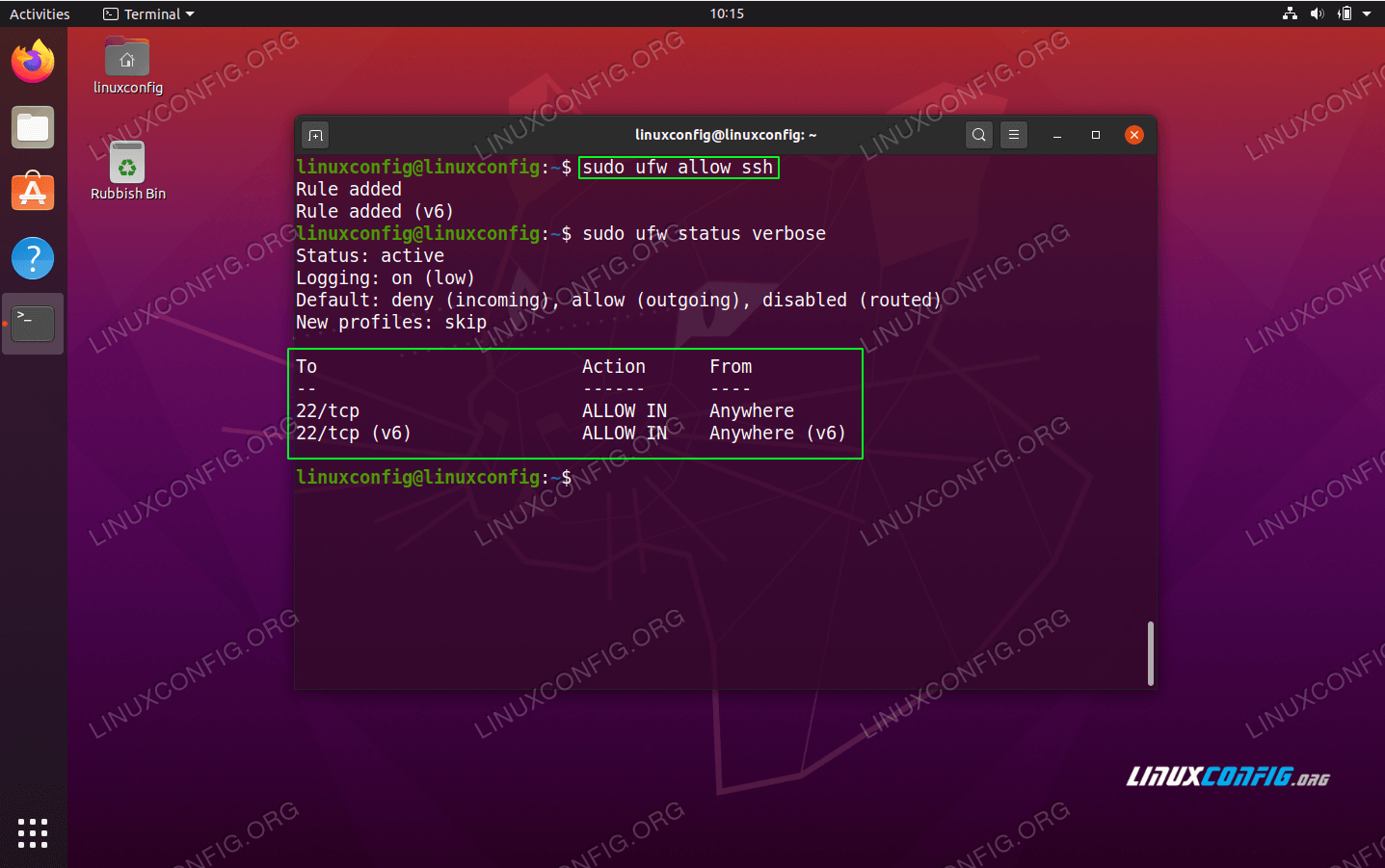
Issue 1: Connection Refused
This issue typically arises due to incorrect IP addresses or firewall restrictions. Verify your IP settings and ensure that SSH is allowed through the firewall.
Issue 2: Authentication Failure
Ensure that the public key is correctly added to the authorized_keys file on the remote device.
Best Practices for Enhanced Security
To fortify security when using SSH for IoT, adhere to the following best practices:
- Use Strong, Unique Passwords: Avoid weak or commonly used passwords to minimize the risk of unauthorized access.
- Disable Password Authentication: Rely solely on key-based authentication for added security.
- Regularly Update Your System: Keep your system and SSH packages up to date to patch vulnerabilities.
Troubleshooting Techniques
Efficient troubleshooting is crucial for resolving issues swiftly. Consider the following tips:
- Check SSH Logs: Review the SSH logs for detailed error messages to identify the root cause of the problem.
- Verify Network Connectivity: Use the
pingcommand to confirm network connectivity between devices. - Refer to Official Documentation: Consult the official SSH documentation for comprehensive guidance.
Advanced Methods for Securing IoT
For advanced users seeking to enhance security further, consider implementing the following techniques:
1. Port Forwarding
Set up port forwarding to enable SSH connections through Network Address Translation (NAT).
2. Two-Factor Authentication
Enable two-factor authentication to add an extra layer of security to your SSH connections.
Conclusion and Recommendations
Securing remote IoT connections using P2P SSH on Ubuntu is an indispensable skill for modern technology professionals. By following the steps outlined in this guide, you can ensure that your devices remain protected while maintaining optimal performance.
We encourage you to:
- Practice the steps in a controlled environment to gain hands-on experience.
- Explore advanced techniques to further enhance the security of your IoT infrastructure.
- Share your experiences and ask questions in the comments section to engage with the community.
Thank you for reading, and don’t hesitate to explore our other articles for more insights into IoT and cybersecurity!