Secure Remote IoT Connections With Raspberry Pi: A Comprehensive Guide
In today's fast-paced technological era, establishing secure peer-to-peer (P2P) connections between remote Internet of Things (IoT) devices has become essential for businesses and individuals alike. By leveraging the capabilities of a Raspberry Pi, you can implement cost-effective and secure remote IoT P2P solutions. Whether you're a tech enthusiast, a small business owner, or a hobbyist, this guide will help you understand how to seamlessly and securely connect IoT devices, unlocking the full potential of modern technology.
As the Internet of Things (IoT) continues to expand, so does the demand for secure, efficient, and budget-friendly methods to manage and monitor IoT devices remotely. This article will explore the intricacies of setting up secure remote IoT P2P connections using a Raspberry Pi. You'll learn how to protect your devices while maximizing their functionality. By the end of this guide, you'll have a thorough understanding of how to download and implement the necessary tools for a secure connection.
Whether your goal is to monitor home security systems, manage industrial equipment, or control smart home devices, this guide will equip you with the knowledge and resources to achieve your objectives. Let's dive into the world of remote IoT P2P connections and discover how to harness their power securely and efficiently.
Read also:Unveiling The Essence Of Main Character True Beauty A Comprehensive Guide
Table of Contents
- Introduction to Remote IoT P2P Connections
- Overview of Raspberry Pi for IoT
- Benefits of Remote IoT P2P Connections
- Security Considerations for Remote IoT
- Setup Process for Raspberry Pi
- Tools and Software for Secure Connections
- Free Solutions for Secure IoT Connections
- Optimizing Remote IoT Connections
- Troubleshooting Tips
- Conclusion and Call to Action
Understanding Remote IoT P2P Connections
Remote IoT P2P connections are transforming the way devices communicate and interact. These connections enable direct communication between devices without the need for a central server, significantly reducing latency and enhancing security. The emphasis here is on "securely connecting" devices, which is crucial in today's digital landscape where data breaches and cyber threats are prevalent.
Why Opt for Peer-to-Peer Networking?
Peer-to-peer (P2P) networks offer several advantages over traditional client-server architectures. They provide a decentralized approach, leading to increased reliability and reduced operational costs. By eliminating the need for a central server, P2P networks operate more efficiently and with less risk of single points of failure. This decentralized structure also enhances scalability, making it ideal for managing large-scale IoT deployments.
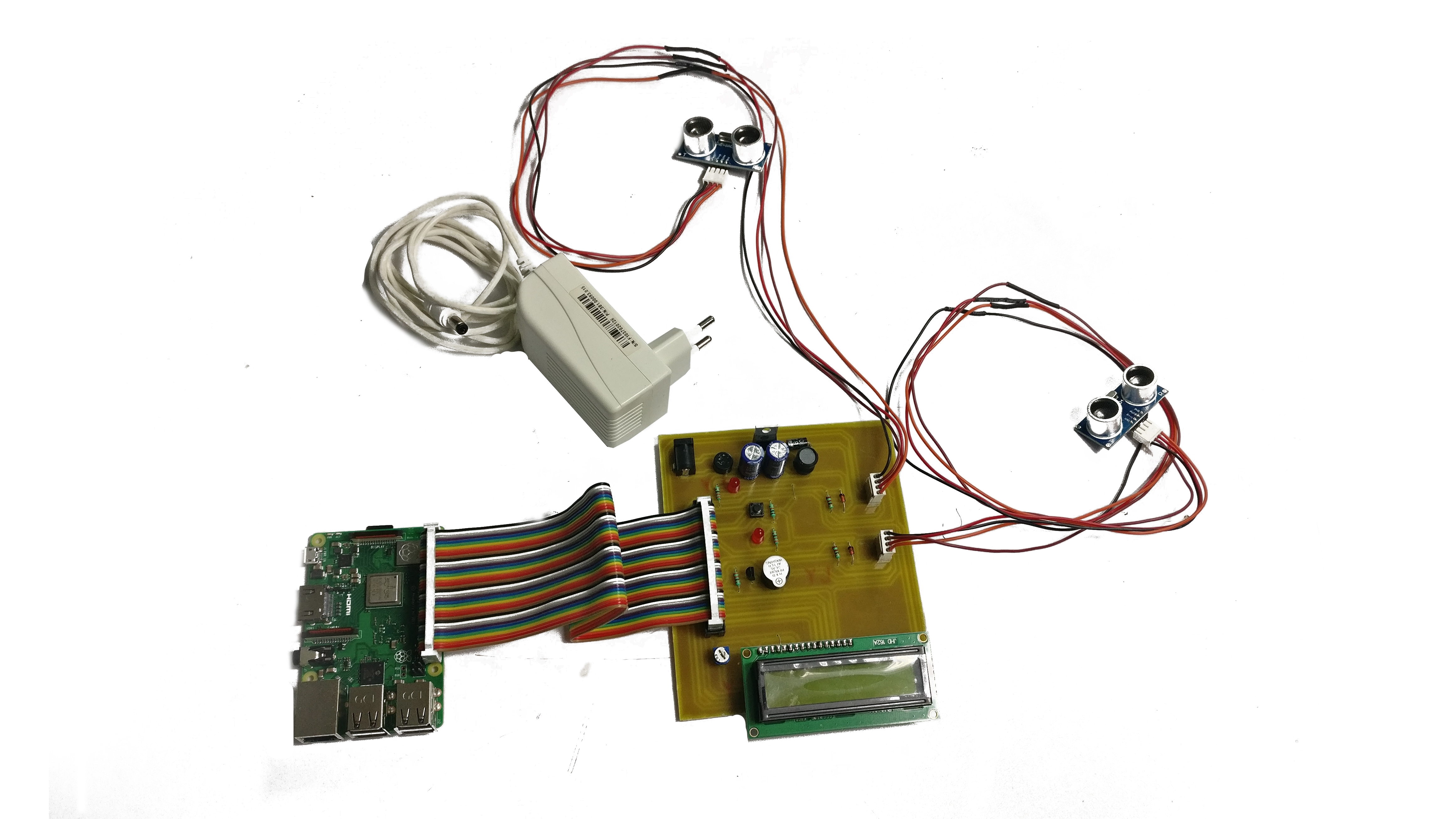
Raspberry Pi: The Ideal Platform for IoT
The Raspberry Pi has emerged as a favorite among IoT enthusiasts due to its affordability, versatility, and ease of use. This compact yet powerful device can be configured to act as a gateway for remote IoT P2P connections, making it an excellent choice for those seeking secure connectivity without excessive costs. Its compact design and low power consumption make it suitable for various applications, from home automation to industrial monitoring.
Key Features of Raspberry Pi
- Compact size and minimal power requirements
- Compatibility with multiple operating systems
- Extensive community support and abundant resources
- Interoperability with a wide array of sensors and devices
Advantages of Remote IoT P2P Connections
Implementing remote IoT P2P connections provides numerous benefits, including enhanced security, improved performance, and significant cost savings. By adopting these connections, businesses and individuals can gain greater control over their IoT devices while maintaining a high level of security. This approach is particularly advantageous for managing large-scale IoT deployments efficiently.
Enhanced Security
Security remains a top priority in the realm of IoT devices. Remote IoT P2P connections help mitigate common security risks by encrypting data transmissions and reducing the attack surface. This ensures that your devices remain protected from unauthorized access and potential breaches, safeguarding sensitive information and maintaining operational integrity.
Critical Security Considerations for Remote IoT
When setting up remote IoT P2P connections, it's vital to address various security aspects to ensure the safety of your devices and data. This includes implementing robust authentication mechanisms, utilizing encryption protocols, and keeping your software up to date to address vulnerabilities. Neglecting these considerations can expose your devices to potential threats and compromise their functionality.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
Best Practices for Securing IoT Devices
- Utilize strong passwords and enable multi-factor authentication
- Deploy firewalls and intrusion detection systems
- Regularly update firmware and software to patch vulnerabilities
- Monitor network activity for any suspicious or anomalous behavior
Step-by-Step Setup Process for Raspberry Pi
Configuring a Raspberry Pi for remote IoT P2P connections involves several stages, from initial setup to installing the necessary software. Below is a detailed guide to help you through the process:
Step 1: Initial Configuration
Start by installing the latest version of Raspberry Pi OS on your device. The Raspberry Pi Imager tool simplifies this process by enabling you to write the operating system to an SD card effortlessly. Ensure that your device is properly connected to a power source and a display during this step.
Step 2: Network Configuration
After installing the OS, configure your network settings to ensure your Raspberry Pi can connect to the internet. Depending on your setup, you may need to configure Wi-Fi or Ethernet connections. Proper network configuration is essential for establishing reliable communication between your IoT devices.
Essential Tools and Software for Secure Connections
A variety of tools and software solutions are available to help you establish secure remote IoT P2P connections. These include open-source libraries, encryption protocols, and monitoring tools that enhance the security and functionality of your setup. Selecting the right tools can significantly improve the performance and reliability of your IoT network.
Popular Tools for Secure IoT Connections
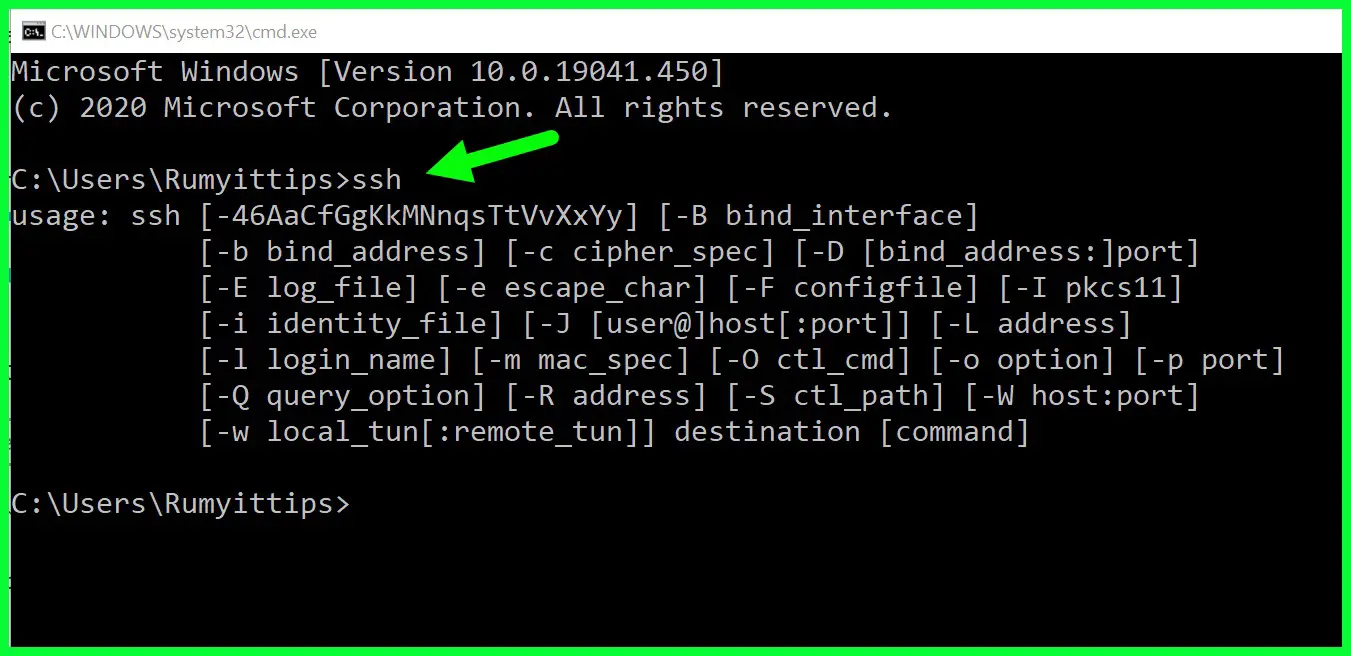
- OpenSSH: Ensures secure communication through encrypted connections
- WireGuard: Provides secure tunneling capabilities for remote access
- MQTT: Facilitates lightweight messaging between IoT devices
Free Solutions for Secure IoT Connections
There are numerous free solutions available for establishing secure IoT connections. These solutions often match the functionality of paid alternatives, making them an excellent choice for those operating on a limited budget. They also benefit from active communities and regular updates to address emerging security challenges.
Advantages of Free IoT Solutions
Free solutions for remote IoT P2P connections offer several advantages, including cost savings, access to a large and supportive user community, and regular updates to address security vulnerabilities. Some popular free solutions include:
- FreeRTOS: A real-time operating system for embedded systems
- Node-RED: A flow-based programming tool for IoT applications
- Home Assistant: A platform for smart home automation and integration
Maximizing Performance of Remote IoT Connections
Optimizing your remote IoT P2P connections can lead to improved performance and reliability. This involves fine-tuning various settings and configurations to ensure your devices operate efficiently and securely. By implementing optimization strategies, you can enhance the overall functionality of your IoT network.
Effective Optimization Strategies
- Minimize latency by optimizing network settings and reducing unnecessary data transmission
- Implement load balancing techniques for distributed systems to distribute workload effectively
- Regularly monitor and analyze performance metrics to identify and address bottlenecks
Addressing Common Issues in Remote IoT Connections
Even with a well-planned setup, issues can arise when working with remote IoT P2P connections. Below are some common troubleshooting tips to help you resolve potential problems and maintain a stable connection.
Common Challenges and Solutions
- Connection failures caused by network instability or incorrect configurations
- Authentication errors during setup due to incorrect credentials or misconfigured settings
- Data transmission delays or interruptions resulting from suboptimal network conditions
Conclusion and Next Steps
In summary, securely connecting remote IoT devices through P2P networks using a Raspberry Pi offers numerous benefits, including enhanced security, improved performance, and cost savings. By following the steps outlined in this guide, you can establish a robust and secure connection tailored to your needs. Whether you're managing home automation systems or industrial equipment, this approach ensures your IoT devices remain protected and functional.
We invite you to share your experiences and insights in the comments section below. Additionally, explore other articles on our site for more in-depth information on IoT and related technologies. Together, let's create a safer, more connected world!
Data Sources: