Mastering SSH Key Management For Remote IoT Devices
In the fast-paced digital era, managing SSH keys for remote IoT devices has become a cornerstone of secure operations. As businesses increasingly depend on reliable and protected connections, understanding the best practices for RemoteIoT SSH key management is more essential than ever. This comprehensive guide will provide you with actionable insights to fortify security and ensure smooth operations.
As the Internet of Things (IoT) continues to expand its reach, the demand for secure communication between interconnected devices rises exponentially. SSH keys play a pivotal role in safeguarding these communications, ensuring that only authorized users and devices gain access to sensitive systems and data.
This article is designed to offer an in-depth exploration of the most effective strategies for managing SSH keys in remote IoT environments. By the end of this guide, you will have a clear understanding of the tools, techniques, and best practices that can significantly enhance your organization's security framework.
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
Table of Contents
- Understanding SSH Key Management
- The Importance of SSH Key Management
- Key Best Practices for RemoteIoT SSH Management
- Essential Tools for SSH Key Management
- Leveraging Automation for SSH Key Management
- Securing Remote IoT Devices
- Avoiding Common Pitfalls in SSH Key Management
- Real-World Success Stories in SSH Key Management
- Emerging Trends in RemoteIoT SSH Key Management
- Final Thoughts and Next Steps
Understanding SSH Key Management
SSH (Secure Shell) keys serve as cryptographic keys that authenticate users and devices in a secure and reliable manner. In the context of RemoteIoT, these keys are indispensable for establishing secure connections between remote devices and centralized systems. Proper SSH key management ensures that only authorized entities can access sensitive data and systems, effectively minimizing the risk of unauthorized access and potential data breaches.
The Importance of SSH Key Management
Robust SSH key management is essential for preserving the security and integrity of remote IoT environments. Without diligent management, SSH keys can become susceptible to misuse, leading to potential security vulnerabilities. According to a report by Gartner, inadequate key management practices contribute to approximately 70% of security incidents in IoT environments. This underscores the critical need for implementing comprehensive SSH key management strategies.
Key Best Practices for RemoteIoT SSH Management
Utilizing Strong Keys
A foundational best practice in RemoteIoT SSH key management is the use of strong keys. Strong keys are characterized by their length and complexity, making them resistant to brute-force attacks. For instance, RSA keys should be at least 2048 bits long, while ECC (Elliptic Curve Cryptography) keys should be a minimum of 256 bits long. Employing strong keys significantly enhances the security of your remote IoT environment.
Implementing Key Rotation
Another critical component of SSH key management is the regular rotation of keys. Rotating keys ensures that even if a key is compromised, its potential impact is limited due to its restricted lifespan. A study by IBM suggests that SSH keys should be rotated at least once every six months to maintain optimal security. Regular key rotation is a proactive measure that safeguards your system against potential breaches.
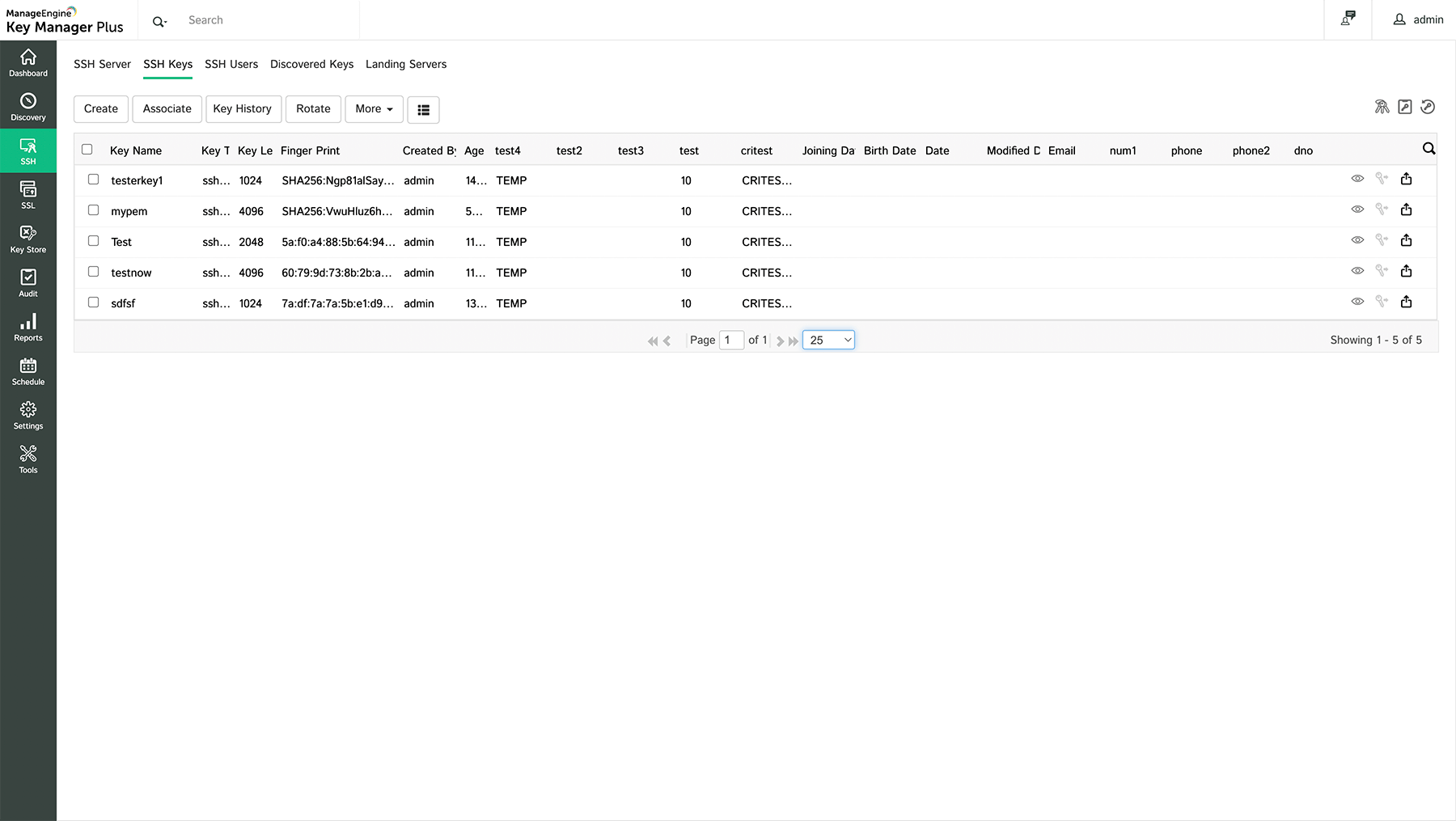
Essential Tools for SSH Key Management
Various tools are available to simplify SSH key management in remote IoT environments. These tools offer features such as key generation, secure storage, and automated rotation, streamlining the management process while enhancing security. Some of the most widely used tools include:
- HashiCorp Vault: A powerful tool for managing secrets, including SSH keys, with robust support for key rotation and access control.
- SSH Key Manager: A specialized tool for managing SSH keys across multiple devices and users, providing centralized control and monitoring capabilities.
- Puppet: An automation platform that can be configured to manage SSH keys as part of its comprehensive infrastructure management offerings.
Leveraging Automation for SSH Key Management
Automation is instrumental in streamlining SSH key management processes. By automating tasks such as key generation, distribution, and rotation, organizations can minimize the risk of human error and ensure consistent adherence to security protocols. Automation tools also offer real-time monitoring and alerts, enabling swift responses to potential security threats. This proactive approach enhances both the security and efficiency of your remote IoT environment.
Read also:What Is The Jamaican Slang For Friend Or Bro Exploring The Vibrant Language Of Jamaica
Securing Remote IoT Devices
Beyond managing SSH keys, securing remote IoT devices necessitates a multi-layered security strategy. This includes implementing robust authentication mechanisms, encrypting data during transmission and at rest, and regularly updating firmware and software. A report by Symantec highlights that encrypting data is one of the most effective methods to protect against unauthorized access and data breaches. A comprehensive security approach ensures the resilience of your remote IoT infrastructure.
Avoiding Common Pitfalls in SSH Key Management
When managing SSH keys for remote IoT environments, it is crucial to avoid several common errors. These include:
- Using weak or default keys that are easily compromised.
- Overlooking the importance of regular key rotation, leaving keys vulnerable to exploitation.
- Failing to monitor key usage and access, which can lead to undetected security breaches.
- Storing keys in insecure locations, increasing the risk of unauthorized access.
Avoiding these mistakes is fundamental to maintaining the security and integrity of your remote IoT environment.
Real-World Success Stories in SSH Key Management
Several organizations have achieved remarkable success by implementing effective SSH key management strategies. For example, a major telecommunications company adopted HashiCorp Vault for managing its SSH keys. This implementation reduced the time required for key rotation by 70% and significantly improved the company's overall security posture. Such case studies demonstrate the tangible benefits of investing in robust SSH key management solutions.
Emerging Trends in RemoteIoT SSH Key Management
As technology continues to advance, new trends in RemoteIoT SSH key management are emerging. These include the adoption of quantum-resistant algorithms, the integration of AI and machine learning for anomaly detection, and the implementation of zero-trust security models. These innovations promise to enhance the security and efficiency of SSH key management in remote IoT environments, paving the way for a more secure digital future.
Final Thoughts and Next Steps
In conclusion, effective SSH key management is indispensable for maintaining the security and integrity of remote IoT environments. By adhering to best practices, leveraging the right tools, and steering clear of common mistakes, organizations can significantly strengthen their security posture. We encourage readers to take the following actions:
- Implement strong key management practices within your organization to enhance security.
- Explore automation tools to streamline and optimize your SSH key management processes.
- Stay informed about emerging trends and technologies in SSH key management to remain ahead of potential threats.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for further insights into remote IoT security and management strategies.