Mastering Secure IoT Connections With P2P SSH On Ubuntu
In today’s fast-paced technological landscape, securely connecting remote IoT devices using Peer-to-Peer (P2P) SSH on Ubuntu has emerged as an indispensable skill for IT professionals and hobbyists alike. As the Internet of Things (IoT) continues to expand, ensuring secure communication channels is no longer optional—it's a necessity. This comprehensive guide explores the intricacies of setting up and managing secure remote IoT connections through SSH on Ubuntu, offering actionable insights and expert advice to help you safeguard your devices.
With businesses and individuals increasingly relying on IoT devices for a wide range of applications, the importance of maintaining data integrity and privacy has never been more critical. The risks associated with unsecured connections, such as data breaches, unauthorized access, and cyberattacks, can have far-reaching consequences. This guide is designed to equip you with the knowledge and tools necessary to create a robust and secure environment for your IoT devices, ensuring peace of mind as you navigate the connected world.
This article will take you step-by-step through the process of setting up a P2P SSH connection on Ubuntu, adhering to the highest security standards. Whether you're an experienced IT professional or a beginner exploring the realm of IoT, this guide will provide valuable insights and practical steps to help you secure your remote IoT connections effectively.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
Table of Contents
- Introduction
- Understanding SSH
- Setting Up Ubuntu for IoT
- Implementing P2P SSH
- Securing Remote Connections
- Best Practices for Secure IoT Connections
- Troubleshooting Common Issues
- Data Security Considerations
- Future Trends in IoT Security
- Conclusion
Introduction
The proliferation of IoT devices has transformed the way we interact with technology, enabling seamless communication between devices across networks. However, with this convenience comes the responsibility to ensure secure and reliable connections. Securely connecting remote IoT devices using P2P SSH on Ubuntu is a powerful solution that addresses many of the security concerns associated with IoT deployments.
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication over potentially unsecured networks. By leveraging SSH, you can establish encrypted connections between IoT devices, ensuring that sensitive data remains protected from potential threats. In this section, we will explore the importance of secure IoT connections and highlight the critical role that SSH plays in achieving this goal. As we delve deeper into the topic, you'll gain a comprehensive understanding of the steps required to implement a secure P2P SSH connection on Ubuntu.
Understanding SSH
What is SSH?
SSH, or Secure Shell, is a network protocol designed to provide secure communication over untrusted networks. It encrypts all data transmitted between devices, ensuring that sensitive information remains confidential and protected from unauthorized access. SSH is widely regarded as one of the most secure methods for remote communication, making it an ideal choice for IoT applications where security is paramount.
How SSH Works
SSH operates by establishing a secure tunnel between two devices, enabling encrypted communication. This process involves several key steps: authentication, key exchange, and encryption. Authentication verifies the identity of the devices involved in the connection, ensuring that only authorized parties can communicate. Key exchange establishes a shared secret key for encrypting and decrypting data, while encryption protects the transmitted data from interception and tampering. Together, these mechanisms form the foundation of SSH's robust security framework.
- Authentication: Verifies the identity of the devices involved in the connection, ensuring that only authorized parties can communicate.
- Key Exchange: Establishes a shared secret key for encrypting and decrypting data, ensuring secure communication.
- Encryption: Protects the data transmitted between devices from interception and tampering, maintaining data integrity and confidentiality.
Setting Up Ubuntu for IoT
Choosing the Right Ubuntu Version
When setting up Ubuntu for IoT applications, selecting the appropriate version is crucial. Ubuntu Core is a lightweight and secure operating system specifically designed for IoT deployments. It offers a streamlined architecture that minimizes resource consumption while maximizing security, making it an ideal choice for embedded systems.
Installing Required Packages
To enable SSH functionality on Ubuntu, you'll need to install the OpenSSH server package. This can be accomplished by running the following command:
Read also:What Is The Gerber Life College Plan And How Can It Help You Save For Education
sudo apt-get install openssh-server
Once installed, the SSH service will start automatically, allowing you to establish secure connections with your IoT devices. It's important to verify that the service is running correctly and that it is configured to meet your specific security requirements.
Implementing P2P SSH
Configuring SSH for P2P Connections
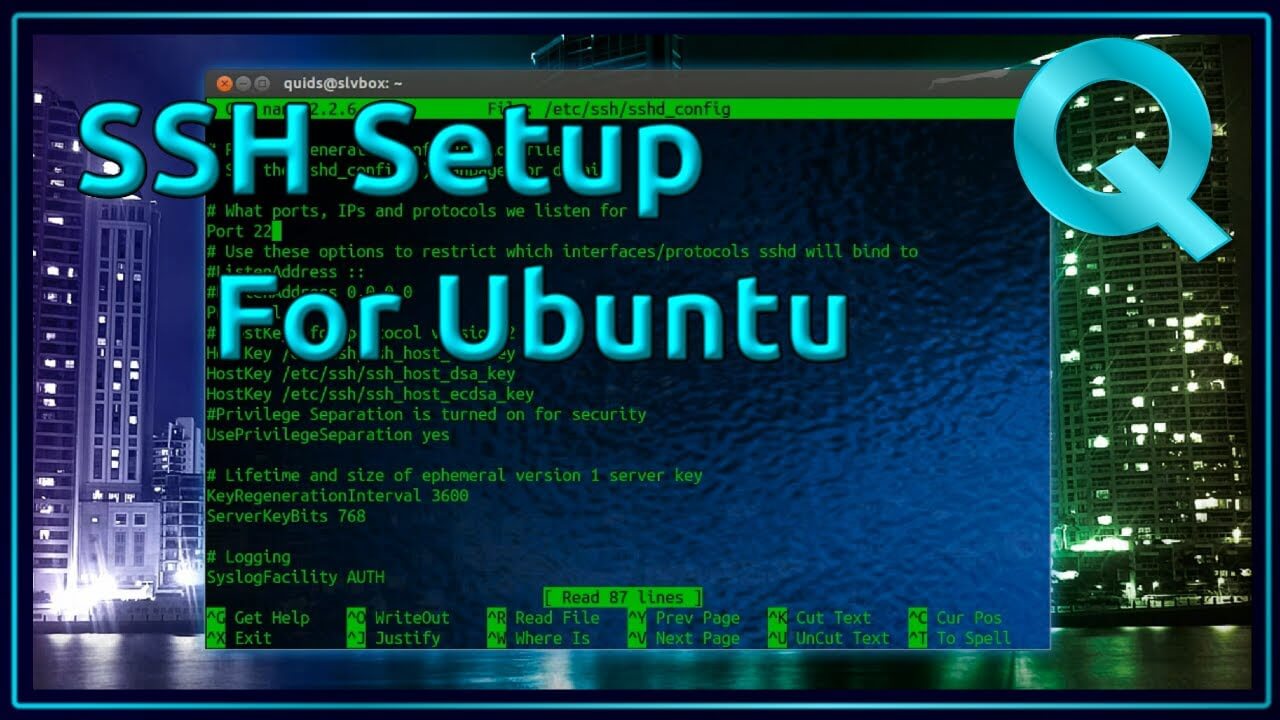
Setting up a P2P SSH connection involves configuring the SSH server to allow direct communication between devices. This can be achieved by modifying the SSH configuration file located at /etc/ssh/sshd_config. Below are some key settings to consider:
- PermitRootLogin: Set to "no" to disable root login, enhancing security by preventing unauthorized access through the root account.
- Port: Specify a non-standard port to reduce the risk of automated attacks and make it more difficult for malicious actors to target your system.
- PublicKeyAuthentication: Enable this option to use public key authentication, which provides a more secure method of access compared to traditional password-based authentication.
Testing the Connection
After configuring the SSH server, it's essential to test the connection to ensure that everything is working as expected. Use the following command to establish the connection:
ssh username@ip_address
Replace "username" with the appropriate user account and "ip_address" with the IP address of the target device. If the connection is successful, you will be logged in to the remote device, confirming that the P2P SSH setup is functioning properly.
Securing Remote Connections
Firewall Configuration
Securing remote connections involves configuring the firewall to allow only authorized traffic. The UFW (Uncomplicated Firewall) tool is an effective way to manage firewall rules on Ubuntu. Use the following commands to enable the firewall and allow SSH traffic:
sudo ufw enable
sudo ufw allow ssh
Monitoring and Logging
Regularly monitoring and reviewing SSH logs is an essential part of maintaining security. By analyzing log files, you can identify potential security threats and take corrective action before they escalate. Use the following command to view SSH logs:
sudo tail -f /var/log/auth.log
This command displays real-time updates of SSH activity, allowing you to detect and respond to suspicious behavior promptly. Regular monitoring helps ensure that your system remains secure and protected from unauthorized access.
Best Practices for Secure IoT Connections
Regular Software Updates
Keeping your Ubuntu system and installed packages up to date is crucial for maintaining security. Regular updates ensure that you have the latest security patches and bug fixes, reducing the risk of vulnerabilities. Use the following commands to update your system:
sudo apt-get update
sudo apt-get upgrade
Strong Password Policies
Enforcing strong password policies can significantly enhance security. Encourage the use of complex passwords that include a mix of uppercase and lowercase letters, numbers, and special characters. Additionally, consider implementing two-factor authentication (2FA) for added protection. This additional layer of security ensures that even if a password is compromised, unauthorized access remains difficult.
Network Segmentation
Segmenting your network can limit the potential impact of a security breach. By isolating IoT devices on a separate network, you can prevent unauthorized access to critical systems and reduce the risk of lateral movement in the event of a compromise. Network segmentation is a key strategy for maintaining a secure and resilient IoT infrastructure.
Troubleshooting Common Issues
Connection Refused Errors
If you encounter "Connection refused" errors, it's important to verify that the SSH service is running and that the firewall allows SSH traffic. Double-check the IP address and port number used for the connection to ensure that they are correct. Additionally, review the SSH configuration file to confirm that all settings are properly configured.
Authentication Failures
Authentication failures can occur due to incorrect credentials or misconfigured settings. Carefully review the username, password, and public key settings to resolve this issue. If you're using public key authentication, ensure that the public key has been correctly added to the authorized_keys file on the remote device.
Data Security Considerations
Encrypting Data at Rest
Encrypting data stored on IoT devices is a critical step in protecting sensitive information from unauthorized access. Tools like LUKS (Linux Unified Key Setup) can be used to encrypt disk partitions, ensuring that data remains secure even if the device is physically compromised. By implementing encryption at rest, you add an additional layer of protection to your IoT devices.
Secure Data Transmission
Ensuring secure data transmission involves using encryption protocols like TLS (Transport Layer Security) in addition to SSH. This provides an extra layer of protection for data transmitted over the network, safeguarding it from interception and tampering. By combining SSH with other encryption protocols, you can create a comprehensive security framework that protects your data at every stage of transmission.
Future Trends in IoT Security
Advancements in Encryption
As technology continues to evolve, advancements in encryption algorithms and quantum computing will play a significant role in shaping the future of IoT security. Staying informed about these developments is essential for maintaining secure connections and protecting your devices from emerging threats. By adopting cutting-edge encryption technologies, you can ensure that your IoT infrastructure remains secure and resilient in the face of evolving challenges.
AI and Machine Learning
The integration of AI and machine learning in IoT security systems will enable more effective threat detection and response. These technologies can analyze patterns and anomalies in network traffic to identify potential security threats proactively. By leveraging AI and machine learning, you can enhance your ability to detect and mitigate threats in real time, ensuring that your IoT devices remain secure and operational.
Conclusion
Securing remote IoT connections using P2P SSH on Ubuntu is a vital step in protecting your devices and data from potential threats. By following the best practices outlined in this guide, you can create a robust and secure environment for your IoT deployments, ensuring that your devices remain safe and reliable. We encourage you to share your thoughts and experiences in the comments section below and to explore other articles on our site to further expand your knowledge of IoT security and related topics. Together, we can build a safer and more connected world.