Mastering Secure IoT Connections On Android With P2P SSH
In the modern digital era, establishing secure connections for remote IoT devices through peer-to-peer (P2P) SSH on Android has become indispensable for tech enthusiasts and professionals alike. Whether you're managing smart home systems or overseeing industrial equipment, maintaining secure communication is crucial. This comprehensive guide explores the complexities of remote IoT connections, focusing on P2P SSH protocols, and offers practical advice for downloading and configuring secure systems on Android devices.
As the number of interconnected devices continues to grow, the security of these networks has become a top priority. The rise of IoT technology has brought immense convenience, but it has also introduced vulnerabilities that cybercriminals can exploit. Understanding how to securely connect remote IoT devices using P2P SSH is not only a technical skill but also a fundamental necessity for safeguarding sensitive data and maintaining network integrity.
This guide is specifically crafted for individuals and organizations aiming to strengthen their cybersecurity measures. By the end of this article, you will gain a deep understanding of the tools, strategies, and best practices for establishing secure connections on Android devices, empowering you to protect your IoT ecosystem effectively.
Read also:Why You Should Join Wewillwritecom Today Unlock Your Writing Potential
Table of Contents
- Exploring Secure Remote IoT Connections
- Understanding IoT and Its Security Challenges
- The Role of P2P SSH in IoT Security
- Strengthening Android Security for IoT Networks
- A Comprehensive Guide to Downloading Secure Tools
- Top Tools for Securing IoT Connections
- Best Practices for Managing IoT Security
- Addressing Common Issues and Troubleshooting Tips
- Emerging Trends in IoT Security
- Conclusion and Next Steps
Exploring Secure Remote IoT Connections
Why Security is Essential in IoT
IoT devices are transforming the way we interact with technology in both personal and professional settings. However, this transformation comes with significant security risks. From smart home systems to industrial automation, the potential for unauthorized access and data breaches is a growing concern. Establishing secure connections for remote IoT devices is critical to protecting sensitive information and ensuring operational reliability.
The Importance of P2P SSH in IoT
Peer-to-peer (P2P) SSH provides a powerful solution for secure communication between IoT devices. Unlike traditional methods that rely on centralized servers, P2P SSH enables direct communication, reducing latency and enhancing security. This section delves into the mechanics of P2P SSH and its advantages over other protocols, offering a deeper understanding of its role in IoT security.
Android as a Platform for IoT Management
Android devices have become increasingly popular for managing IoT networks due to their flexibility, affordability, and widespread adoption. However, ensuring secure connections on Android requires a thorough understanding of security protocols and tools. This article provides valuable insights into optimizing Android devices for effective IoT management.
Understanding IoT and Its Security Challenges
What is IoT?
The Internet of Things (IoT) refers to the vast network of interconnected devices capable of collecting, transmitting, and exchanging data. These devices range from simple sensors to sophisticated industrial machinery. While IoT technology offers numerous benefits, it also introduces significant challenges, particularly in terms of security and privacy.
Key Security Challenges in IoT
IoT security faces several critical challenges, including:
- Data breaches resulting from inadequate security measures
- Unauthorized access due to weak authentication protocols
- Vulnerabilities in device firmware and software
- Network attacks such as DDoS and malware propagation
Tackling these challenges requires a holistic approach that combines secure protocols, regular updates, and user education to create a robust defense mechanism.
Read also:What Does Obsidian Kingdom Mean Unveiling The Mysteries Of The Name
The Role of P2P SSH in IoT Security
Defining P2P SSH and Its Functionality
P2P SSH (Secure Shell) is a cryptographic network protocol that facilitates secure communication between two devices without the need for a central server. By encrypting data in transit, P2P SSH ensures that only authorized parties can access the information, providing an additional layer of security for IoT networks.
Advantages of P2P SSH
P2P SSH offers several compelling advantages that make it a preferred choice for securing IoT connections:
- Enhanced Security: Advanced encryption techniques protect data from unauthorized access.
- Reduced Latency: Direct communication eliminates the need for intermediaries, resulting in faster data transfer.
- Improved Scalability: P2P SSH is well-suited for large networks, ensuring consistent performance as the number of devices grows.
- Cost-Effective: By eliminating reliance on centralized servers, P2P SSH reduces infrastructure costs.
These benefits position P2P SSH as an ideal solution for securing IoT connections in environments where data security is paramount.
Strengthening Android Security for IoT Networks
Security Features of Android
Android provides several built-in security features that can be effectively utilized for IoT management. These include:
- App Permissions: Control which apps have access to sensitive data and device functions.
- Device Encryption: Protect stored data by encrypting it at the device level.
- Regular Security Updates: Stay protected against emerging threats with timely updates.
- Biometric Authentication: Enhance security with fingerprint or facial recognition for device access.
Understanding and leveraging these features is essential for maintaining secure IoT connections on Android devices.
Best Practices for Android IoT Security
To enhance Android security for IoT connections, consider adopting the following best practices:
- Use strong, unique passwords and enable two-factor authentication for added protection.
- Regularly update apps and the operating system to ensure compatibility with the latest security patches.
- Only download apps from trusted sources, such as the Google Play Store or verified developer websites.
- Monitor device activity regularly to detect and address any suspicious behavior promptly.
Implementing these practices can significantly reduce the risk of security breaches and ensure a more secure IoT environment.
A Comprehensive Guide to Downloading Secure Tools
Selecting Reliable Tools
When choosing tools for securely connecting remote IoT devices, it's crucial to select reliable and trusted options. Platforms like the Google Play Store and official developer websites are safe sources for downloading apps. Always verify the authenticity of the app and read user reviews to ensure its reliability.
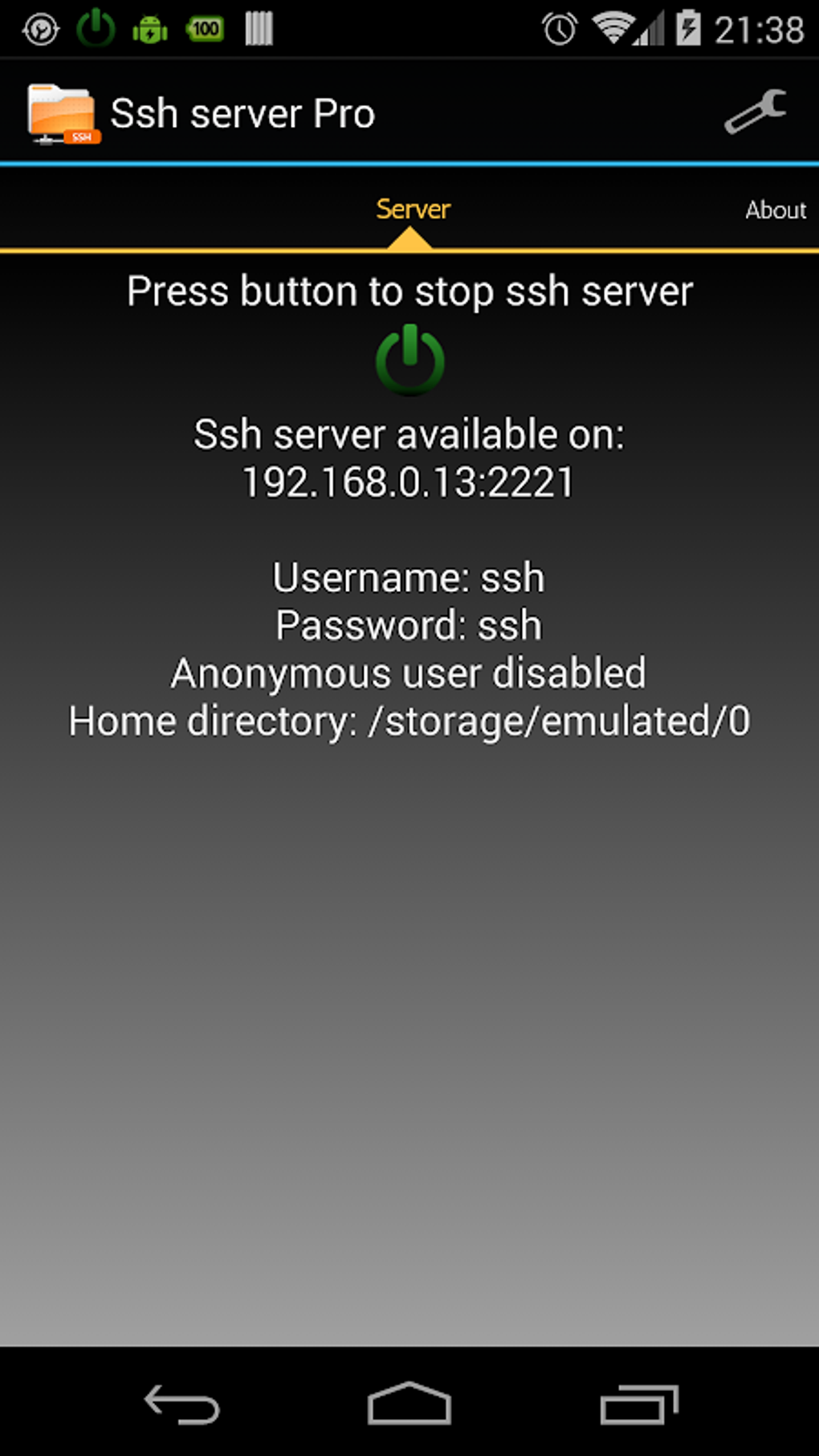
Installation and Configuration
After downloading the necessary tools, follow these steps for a seamless installation and setup process:
- Open the downloaded app on your Android device and review its permissions.
- Follow the on-screen instructions to complete the installation process.
- Customize app settings to align with your specific security requirements.
- Test the connection to confirm proper functionality and address any issues.
Proper installation and configuration are essential for maximizing the security benefits of these tools.
Top Tools for Securing IoT Connections
Tool 1: SSH Client for Android
SSH Client apps, such as Termius or ConnectBot, are indispensable for establishing secure connections between IoT devices. These apps provide an intuitive interface for managing SSH sessions and include advanced features like key management and session logging, ensuring secure and efficient communication.
Tool 2: Firewall and Antivirus Solutions
Firewall and antivirus apps, like Norton Mobile Security or Kaspersky Mobile Antivirus, are vital for protecting Android devices from malicious attacks. These tools monitor network activity and block unauthorized access, providing an additional layer of security for IoT connections.
Tool 3: Virtual Private Network (VPN) Services
Using a Virtual Private Network (VPN) can further enhance security by encrypting all data transmitted between devices. Services like NordVPN or ExpressVPN offer robust security features and are compatible with Android devices, making them ideal for securing IoT networks.
Best Practices for Managing IoT Security
Regular Updates and Maintenance
Keeping all devices and software up to date is one of the most effective ways to ensure security. Regular updates address known vulnerabilities and improve overall system performance, reducing the risk of security breaches.
Network Segmentation for Enhanced Protection
Segmenting your network can significantly limit the impact of a potential breach. By isolating IoT devices from critical systems, you can minimize the risk of widespread damage in the event of an attack, ensuring a more secure and resilient network infrastructure.
User Education and Awareness
Empowering users with knowledge about security best practices is essential for maintaining a secure IoT environment. Conducting training sessions and awareness campaigns can help users understand the importance of security and their role in protecting the network.
Addressing Common Issues and Troubleshooting Tips
Resolving Connection Problems
Connection issues are a common challenge when setting up P2P SSH for IoT devices. These problems may arise from incorrect configurations, network restrictions, or device incompatibilities. To troubleshoot effectively, consider the following steps:
- Ensure all devices are connected to the same network and verify their settings.
- Double-check SSH configurations, including credentials and port settings.
- Restart devices and retry the connection to rule out temporary glitches.
Handling Security Alerts
Security alerts are a frequent occurrence in IoT networks, often indicating potential threats or unauthorized access attempts. Always investigate these alerts promptly and take appropriate action to address any issues, ensuring the ongoing security of your IoT ecosystem.
Emerging Trends in IoT Security
Advancements in Encryption Techniques
As technology continues to evolve, advancements in encryption methods will play a pivotal role in enhancing IoT security. Cutting-edge techniques such as quantum encryption and homomorphic encryption hold great promise for revolutionizing data protection and ensuring the security of IoT networks.
Artificial Intelligence in Security Solutions
AI-driven security solutions are gaining traction for their ability to detect and respond to threats in real time. These systems analyze vast amounts of data to identify patterns and anomalies, providing proactive protection against cyberattacks and enhancing the overall security of IoT networks.
Conclusion and Next Steps
Securing remote IoT devices via P2P SSH on Android is a critical aspect of modern cybersecurity. By understanding the challenges, utilizing the right tools, and adhering to best practices, you can effectively protect your IoT network from potential threats. Staying informed about the latest trends and advancements in IoT security will ensure your systems remain secure and resilient.
We encourage you to take immediate action by implementing the strategies outlined in this article. Share your experiences and insights in the comments section below, and explore other resources on our website for further guidance on cybersecurity and IoT management. Together, we can build a safer and more secure digital future for everyone.