Mastering Remote IoT Device Management Via Web Browser On Windows
Connecting to an IoT device remotely through a web browser on Windows is a valuable skill that bridges the gap between physical devices and cloud-based systems. In today's interconnected world, remote access to IoT devices is essential for monitoring, troubleshooting, and maintaining equipment without being physically present. This comprehensive guide will walk you step by step through the process, ensuring you establish a secure and reliable connection.
Remote SSH (Secure Shell) access to IoT devices via a web browser has gained immense popularity due to its convenience and ease of use. Whether you're a developer, system administrator, or hobbyist, understanding how to set up and manage remote connections is crucial for efficient device management. This article will provide detailed instructions to help you achieve seamless connectivity, enhancing your ability to manage IoT devices effectively.
By the end of this guide, you'll possess the knowledge to remotely SSH into IoT devices using a web browser on Windows. We'll explore everything from setting up your environment to troubleshooting common issues, ensuring a smooth and secure experience. Let's get started!
Read also:Exploring The Influence And Achievements Of Kim Kylie And Kendall
Table of Contents
- Understanding SSH
- Benefits of Remote SSH for IoT Devices
- Prerequisites for Remote SSH
- Setting Up Web Browser SSH
- Configuring Your IoT Device for Remote Access
- Securing Your Remote SSH Connection
- Troubleshooting Common Issues
- Alternatives to Web Browser SSH
- Best Practices for Remote IoT Device Management
- Conclusion
Understanding SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to facilitate secure communication between devices over an unsecured network. Widely used for remote command-line login and data transfer, SSH is an indispensable tool for managing and interacting with IoT devices remotely. Its robust security features make it ideal for safeguarding sensitive operations.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between the client and server, ensuring confidentiality and protecting against unauthorized interception.
- Authentication: It supports various authentication methods, including passwords and public-key cryptography, to verify the identity of users and prevent unauthorized access.
- Portability: SSH is compatible with multiple platforms, including Windows, macOS, and Linux, making it a versatile choice for diverse environments.
Understanding SSH is foundational to mastering remote IoT device management. Let's delve deeper into why remote SSH is particularly advantageous for IoT devices.
Benefits of Remote SSH for IoT Devices
IoT devices are frequently deployed in remote locations, making physical access challenging or impractical. Remote SSH offers several compelling advantages for managing these devices:
- Efficiency: Diagnose and resolve issues quickly without the need to travel to the device's physical location, saving time and resources.
- Security: SSH ensures encrypted communication, safeguarding sensitive data from unauthorized access and potential cyber threats.
- Scalability: Manage multiple IoT devices from a centralized location, streamlining operations and enhancing productivity.
As the global deployment of IoT devices continues to grow, remote SSH access has become an essential tool for maintaining and monitoring these devices effectively.
Prerequisites for Remote SSH
Before setting up remote SSH access to your IoT device via a web browser on Windows, ensure you meet the following prerequisites:
Software Requirements
- Windows 10 or later, equipped with the built-in OpenSSH client for seamless integration.
- A modern web browser such as Google Chrome or Microsoft Edge, capable of supporting SSH connections.
- A terminal emulator or SSH client if you prefer not to use the built-in Windows SSH client for advanced functionality.
Hardware Requirements
- An IoT device with SSH server capabilities enabled, ensuring it can receive and process remote commands securely.
- A stable and reliable internet connection for both the client and server to maintain uninterrupted communication.
Having these prerequisites in place will ensure a smooth setup process. Let's now proceed to configuring your web browser for SSH access.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
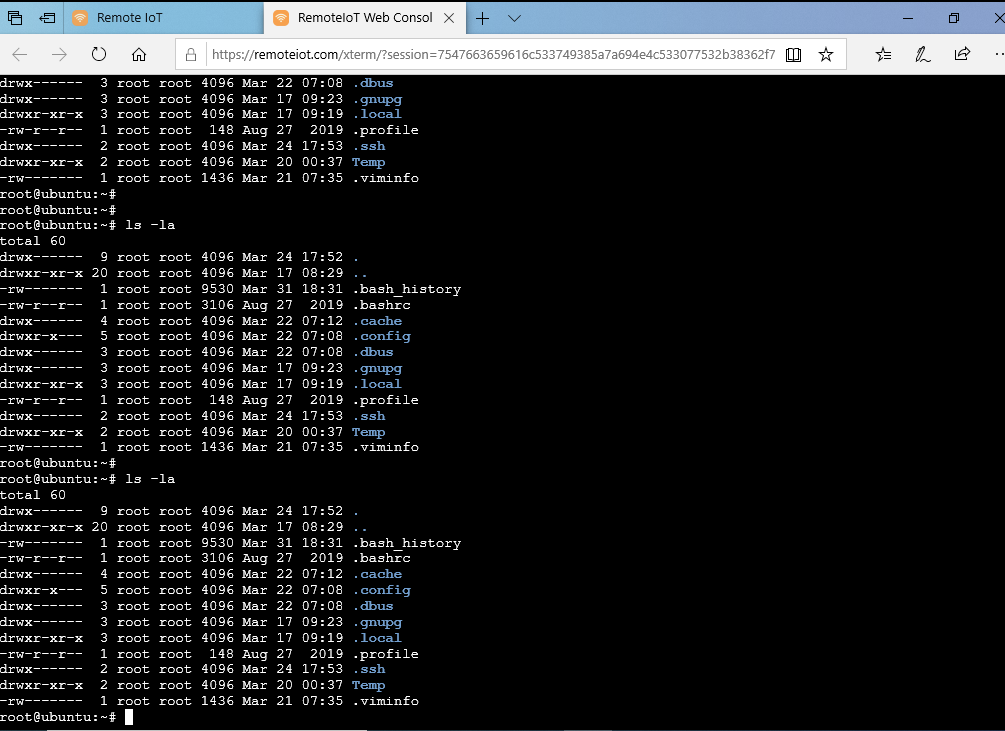
Setting Up Web Browser SSH
Modern web browsers, such as Google Chrome and Microsoft Edge, support SSH connections through extensions or built-in features. Follow these steps to configure SSH access:
Using Chrome DevTools
- Launch Google Chrome and navigate to the address bar to initiate the configuration process.
- Enter
chrome://flags/#enable-experimental-web-platform-featuresin the address bar and enable the experimental flag to unlock advanced capabilities. - Restart Chrome to apply the changes and ensure the new settings take effect.
- Use the
ssh://protocol to connect to your IoT device by entering the device's IP address or domain name, establishing a secure link.
Using Microsoft Edge
- Open Microsoft Edge and confirm that it is updated to the latest version for optimal performance and security.
- Enter
edge://flags/#enable-experimental-web-platform-featuresin the address bar and enable the feature to activate advanced functionality. - Restart the browser and use the
ssh://protocol to connect to your IoT device, ensuring a secure and reliable connection.
These steps empower your web browser to function as an SSH client, simplifying the connection process and enhancing your ability to manage IoT devices remotely.
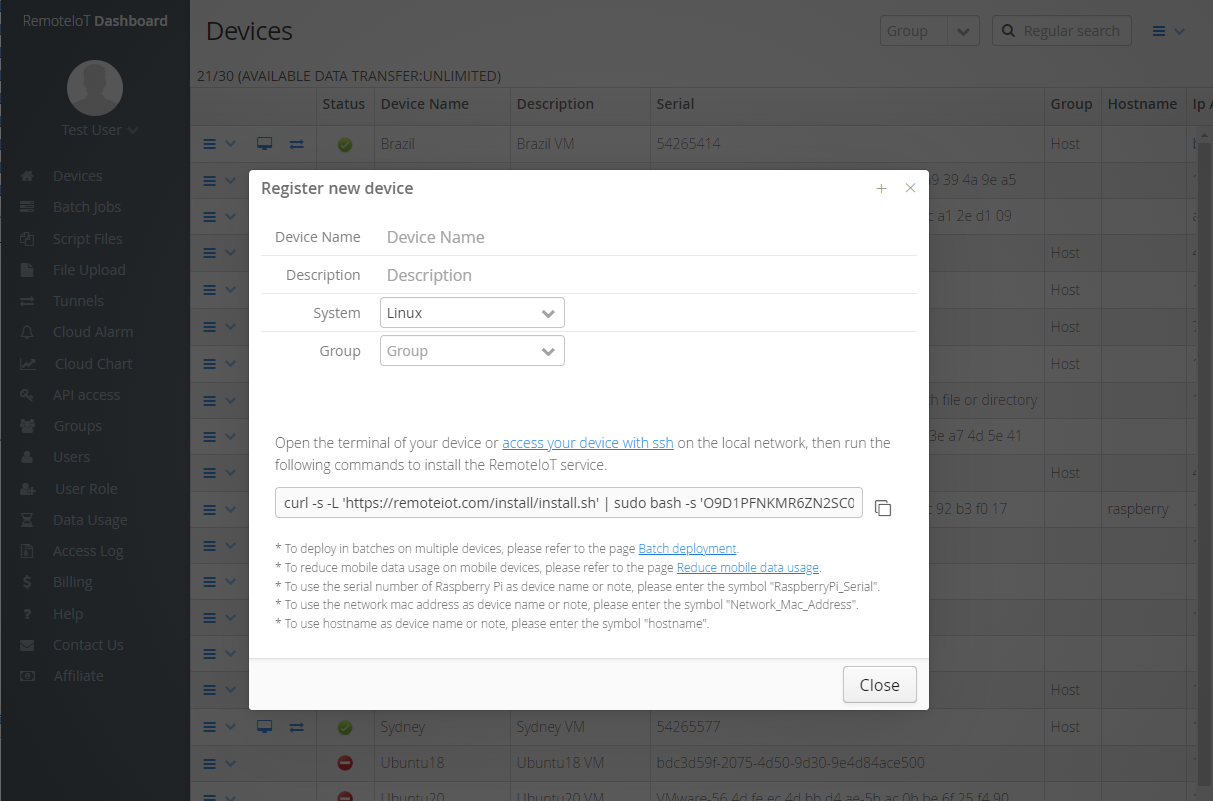
Configuring Your IoT Device for Remote Access
To enable remote SSH access, your IoT device must be properly configured. Follow these steps to ensure seamless connectivity:
Enable SSH Server
- Log in to your IoT device's management interface using the appropriate credentials and administrative tools.
- Locate the SSH settings and enable the SSH server to allow incoming connections from authorized users.
- Set a strong password or configure public-key authentication for enhanced security, minimizing the risk of unauthorized access.
Port Forwarding
- Log in to your router's configuration page to manage network settings and establish secure communication channels.
- Set up port forwarding to direct incoming SSH traffic (port 22) to your IoT device's internal IP address, ensuring it is accessible from outside your local network.
Proper configuration ensures that your IoT device is accessible remotely while maintaining robust security measures to protect against potential threats.
Securing Your Remote SSH Connection
Security is a top priority when remotely accessing IoT devices. Implement the following best practices to safeguard your connections:
Use Public-Key Authentication
- Generate an SSH key pair on your Windows machine using the built-in SSH client to establish secure and trusted connections.
- Copy the public key to your IoT device's authorized_keys file, ensuring only authorized users can access the device.
Disable Password Authentication
- Edit the SSH configuration file (
/etc/ssh/sshd_config) on your IoT device to enhance security and prevent unauthorized access. - Set
PasswordAuthentication noto disable password-based logins, reducing the risk of brute-force attacks.
Implementing these measures significantly strengthens the security of your remote SSH connections, ensuring your IoT devices remain protected from potential threats.
Troubleshooting Common Issues
Even with meticulous setup, issues may arise. Here are solutions to common problems:
Connection Refused
- Ensure the SSH server is running on your IoT device and configured to accept incoming connections.
- Verify your router's port forwarding settings to confirm that traffic is directed correctly to the IoT device's internal IP address.
Authentication Failure
- Confirm that the public key is correctly added to the authorized_keys file on your IoT device, ensuring secure authentication.
- Double-check the username and IP address used during the connection to avoid authentication errors and ensure successful access.
Addressing these issues promptly will help maintain uninterrupted access to your IoT devices, ensuring smooth and secure remote management.
Alternatives to Web Browser SSH
While web browser SSH offers unparalleled convenience, alternative methods are available for advanced users:
SSH Clients
- Utilize dedicated SSH clients like PuTTY or MobaXterm for enhanced functionality and advanced features, catering to more complex IoT setups.
Cloud-Based Solutions
- Leverage cloud platforms such as AWS IoT or Azure IoT Hub for comprehensive remote device management, integrating advanced security and scalability features.
Selecting the right method depends on your specific requirements and the complexity of your IoT infrastructure, ensuring optimal performance and security.
Best Practices for Remote IoT Device Management
Adopting best practices ensures efficient and secure management of your IoT devices:
- Regularly update firmware and software on your IoT devices to address vulnerabilities and enhance performance.
- Monitor device activity logs for suspicious behavior, enabling proactive identification and resolution of potential security threats.
- Implement network segmentation to isolate IoT devices from other network traffic, minimizing the risk of unauthorized access and enhancing overall security.
By adhering to these practices, you can maintain a robust and secure IoT infrastructure, ensuring optimal performance and reliability.
Conclusion
Remotely SSH-ing into an IoT device via a web browser on Windows is a practical and secure method for managing remote devices. This guide has provided a comprehensive overview of the essential steps, from setting up your environment to securing your connections. Remember to follow best practices and stay updated with the latest advancements in technology to enhance your skills and knowledge.
We encourage you to share your experiences and ask questions in the comments below. For more insights into IoT management and cybersecurity, explore our other articles. Together, let's build a safer and more connected world!