Mastering Remote IoT Access Without MAC Address Filtering
In today's highly interconnected world, the Internet of Things (IoT) has seamlessly integrated into our daily routines. Learning how to manage remote IoT devices behind a router without relying on MAC address filtering is essential for both enhanced security and convenience. This comprehensive guide will walk you through the process step-by-step, ensuring you maximize the functionality of your IoT devices while maintaining a secure network environment.
As the adoption of smart devices continues to grow, the ability to control and monitor them remotely has become indispensable. Whether you're adjusting smart lighting, checking security camera feeds, or managing home automation systems, understanding how to set up remote IoT access can significantly enhance your experience. This guide will delve into the technical aspects and provide practical solutions to help you achieve this.
Our focus will be on delivering a clear, actionable plan for setting up remote access to IoT devices without depending on MAC address filtering. By the end of this article, you'll have the knowledge and tools necessary to implement these techniques effectively and securely.
Read also:Exploring Elon Musks Partners And Kids A Comprehensive Look
Table of Contents
- Understanding Remote IoT Access
- The Importance of Routers in IoT Management
- Exploring MAC Address Filtering and Its Limitations
- Step-by-Step Guide to Setting Up Remote IoT Behind a Router
- Enhancing Security for Remote IoT Devices
- Essential Tools and Software for Remote IoT Access
- Troubleshooting Common Challenges in IoT Setup
- Alternative Solutions Beyond MAC Address Filtering
- Comparing Popular IoT Platforms
- Conclusion and Next Steps
Understanding Remote IoT Access
Remote IoT refers to the capability of controlling and monitoring Internet of Things devices from anywhere in the world. This technology empowers users to interact with their smart devices regardless of their physical location. For instance, you can adjust your smart thermostat while at work or review your home security camera footage while on vacation.
However, setting up remote IoT behind a router requires a solid understanding of networking principles. This setup ensures that your devices remain secure and accessible exclusively to authorized users. The process involves configuring your router, setting up port forwarding, and implementing secure communication protocols.
In this section, we'll explore the fundamentals of remote IoT and why it's becoming increasingly vital for modern households and businesses.
The Importance of Routers in IoT Management
Routers as the Central Nervous System
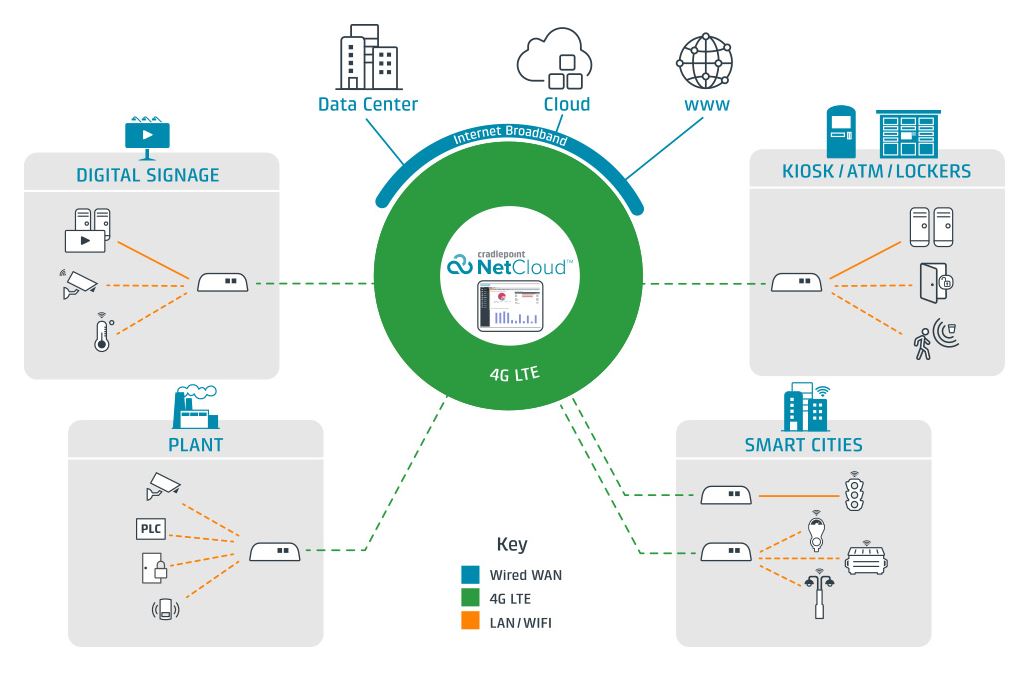
Routers serve as the backbone of IoT ecosystems, connecting all smart devices within a network. They play a crucial role in managing data flow, optimizing bandwidth usage, and enhancing security for your IoT infrastructure.
Key Benefits of Using a Router
- Centralized management of all connected devices, simplifying oversight and control.
- Advanced security features such as firewalls and encryption, safeguarding your network against unauthorized access.
- Improved network performance and stability, ensuring seamless operation of your IoT devices.
With the proliferation of IoT devices in homes and workplaces, routers have become indispensable for maintaining efficient and secure networks.
Exploring MAC Address Filtering and Its Limitations
MAC address filtering is a security mechanism that grants or denies network access based on a device's unique hardware identifier. While this method adds an extra layer of security, it also has notable limitations. For example, MAC addresses can be spoofed, rendering the filtering ineffective and leaving your network vulnerable.
Read also:What Is The Jamaican Slang For Friend Or Bro Exploring The Vibrant Language Of Jamaica
In this guide, we'll explore alternative methods for securing your IoT devices without relying on MAC address filtering. These methods include implementing strong passwords, enabling encryption, and configuring firewalls to fortify your network's defenses.
Step-by-Step Guide to Setting Up Remote IoT Behind a Router
Step 1: Inventory Your IoT Devices
Before configuring your router, it's essential to create a comprehensive list of all IoT devices connected to your network. This step ensures that you include every necessary device in your setup process, preventing oversight and enhancing overall network management.
Step 2: Configure Port Forwarding
Port forwarding is a critical component of enabling remote access to IoT devices. It directs specific ports on your router to particular devices, facilitating secure communication. Follow these steps to configure port forwarding:
- Log in to your router's admin interface using the appropriate credentials.
- Navigate to the port forwarding section, typically found under advanced settings.
- Enter the IP address of your IoT device and the desired port number, ensuring accuracy and consistency.
Step 3: Leverage a Dynamic DNS Service
A dynamic DNS (DDNS) service translates your router's dynamic IP address into a static domain name. This feature simplifies remote access by providing a consistent and easily memorable address for your IoT devices, enhancing user convenience.
Enhancing Security for Remote IoT Devices
Security should always be a top priority when setting up remote IoT access. Below are some best practices to ensure your devices remain protected from potential threats:
- Implement strong, unique passwords for all devices and accounts to deter unauthorized access.
- Enable robust encryption protocols like WPA3 for your Wi-Fi network, safeguarding data transmission.
- Regularly update firmware and software for all IoT devices to patch vulnerabilities and enhance functionality.
- Deploy a firewall to monitor and block unauthorized traffic, adding an additional layer of protection.
By adhering to these guidelines, you can significantly reduce the risk of cyberattacks and unauthorized access, ensuring the integrity of your IoT ecosystem.
Essential Tools and Software for Remote IoT Access
Top Remote Access Tools
Several tools and software solutions are available to facilitate remote access to IoT devices. Some of the most popular options include:
- TeamViewer: A versatile and secure remote access tool with a wide range of features tailored for IoT management.
- LogMeIn: A user-friendly platform designed for managing remote devices with ease and efficiency.
- ngrok: A powerful tool for creating secure tunnels to local servers, ideal for developers and advanced users.
Selecting the Right Tool
When choosing a remote access tool, consider factors such as ease of use, compatibility with your devices, and the level of security offered. Conducting thorough research and comparing features can help you make an informed decision that aligns with your specific needs and preferences.
Troubleshooting Common Challenges in IoT Setup
Despite careful planning, challenges may arise during the setup of remote IoT access. Below are some common issues and their corresponding solutions:
- Device Not Accessible: Verify your port forwarding settings and ensure the device's IP address is correctly configured.
- Connection Timeout: Check your internet connection stability and ensure your router's firmware is up to date to optimize performance.
- Security Alerts: Review your firewall settings and confirm they are not inadvertently blocking legitimate traffic.
Promptly addressing these issues will help maintain a stable and secure IoT network, ensuring seamless operation of your smart devices.
Alternative Solutions Beyond MAC Address Filtering
If you're seeking alternatives to MAC address filtering for managing your IoT devices, several robust solutions are available. These tools provide enhanced security and functionality without relying on MAC filtering:
- TeamViewer: Offers both free and premium versions with advanced features for IoT management.
- LogMeIn: Provides a user-friendly interface for remote access, simplifying device management.
- ngrok: Ideal for developers and advanced users, offering secure tunnels for local server access.
These tools can significantly enhance your IoT setup, providing flexibility and security without the need for MAC address filtering.
Comparing Popular IoT Platforms
Several IoT platforms offer unique features and capabilities for managing smart devices. Below is a detailed comparison of some popular options:
| Platform | Key Features | Security Measures | Pricing |
|---|---|---|---|
| Amazon Alexa | Voice control integration, extensive smart home compatibility | End-to-end encryption, regular security updates | Free with compatible devices |
| Google Home | Smart home automation, advanced AI assistance | Data encryption, automatic firmware updates | Free with compatible devices |
| Home Assistant | Highly customizable, open-source architecture | User-configurable security settings, community-driven support | Free, donation-based funding model |
Selecting the right platform depends on your specific requirements, preferences, and budget. Carefully evaluating these options will help you choose the best solution for your IoT needs.
Conclusion and Next Steps
Setting up remote IoT access behind a router without relying on MAC address filtering is a practical and secure approach to managing smart devices. By following the comprehensive steps outlined in this guide, you can ensure your IoT ecosystem remains efficient, accessible, and protected from potential threats.
We encourage you to share your experiences, insights, and questions in the comments section below. Additionally, feel free to explore other resources on our site for further tips and strategies to optimize your IoT setup. Together, we can build a smarter, safer, and more connected future.
Data sources and references: