Enhancing Security With Remote Access IoT Firewalls
In today's highly interconnected world, ensuring secure communication between IoT devices has become paramount. As the Internet of Things (IoT) continues to expand, both businesses and individuals must adopt robust cybersecurity measures. This article explores the critical role of remote access IoT firewalls, offering practical examples and actionable strategies to help you fortify your network security.
The widespread adoption of IoT devices has revolutionized industries by providing unprecedented convenience and efficiency. However, this rapid expansion also introduces significant security challenges. Enabling secure remote access to IoT devices necessitates the implementation of a well-designed firewall to safeguard sensitive data against unauthorized access. By delving into best practices and real-world examples of remote access IoT firewalls, you can better protect your network infrastructure.
This comprehensive guide aims to provide in-depth insights into remote access IoT firewall examples, their advantages, and effective implementation strategies. By the conclusion of this article, you will possess a thorough understanding of how to secure your IoT devices and networks effectively.
Read also:Discovering The Most Dangerous Zodiac Sign When Angry Unveiling Astrological Insights
Table of Contents
- Understanding Remote Access IoT Firewalls
- Advantages of Implementing IoT Firewalls
- Different Types of Firewalls for IoT Networks
- Practical Example of Remote Access IoT Firewalls
- Steps for Configuring IoT Firewalls for Remote Access
- Essential Security Considerations for IoT Firewalls
- Best Practices for Remote Access IoT Firewalls
- Top Tools and Software for Managing IoT Firewalls
- Real-Life Case Studies: Success Stories
- The Evolution of Remote Access IoT Firewalls
- Final Thoughts
Understanding Remote Access IoT Firewalls
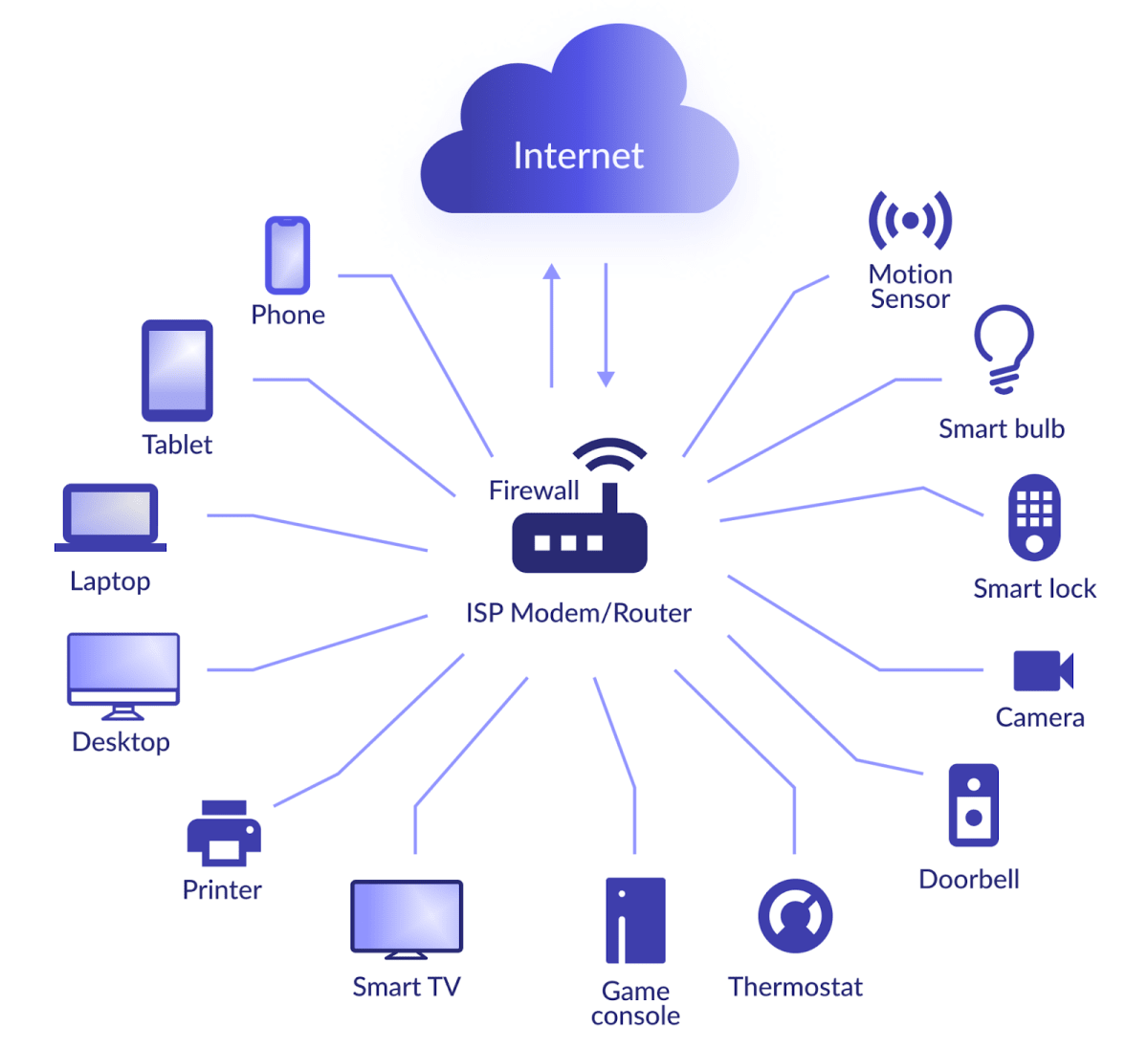
As IoT devices become increasingly integrated into daily operations, the importance of secure remote access has never been more critical. A remote access IoT firewall serves as a foundational element in protecting these devices from potential cyber threats. Essentially, firewalls act as protective barriers between internal networks and external access points, filtering traffic based on predefined rules to ensure only authorized access.
Implementing a remote access IoT firewall guarantees that unauthorized users are unable to infiltrate your network, thereby minimizing the risk of data breaches. This section will explore the fundamentals of IoT firewalls, their significance, and their contribution to comprehensive network security.
Advantages of Implementing IoT Firewalls
The deployment of IoT firewalls offers numerous benefits that significantly enhance network security:
- Enhanced Data Protection: Prevent unauthorized access to sensitive information by establishing stringent access controls.
- Comprehensive Network Monitoring: Gain detailed visibility into network traffic, enabling the detection and mitigation of suspicious activities.
- Regulatory Compliance: Ensure adherence to industry standards and regulations for robust cybersecurity measures.
- Scalable Security Solutions: Adapt effortlessly to expanding IoT ecosystems without compromising security.
These advantages underscore the necessity of IoT firewalls as an essential tool for securing remote access to IoT devices.
Different Types of Firewalls for IoT Networks
Various types of firewalls can be employed within IoT networks, each offering unique features:
Packet Filtering Firewalls
Packet filtering firewalls scrutinize individual packets of data to determine their legitimacy. While this method is efficient, it may lack some advanced features necessary for modern security requirements.
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
Stateful Inspection Firewalls
Stateful inspection firewalls monitor active connections and evaluate packets based on contextual information. They provide superior security compared to traditional packet filtering firewalls, making them ideal for IoT environments.
Next-Generation Firewalls (NGFW)
NGFWs integrate conventional firewall capabilities with cutting-edge features such as intrusion prevention and application awareness. Their advanced functionalities make them indispensable for securing modern IoT networks.
Practical Example of Remote Access IoT Firewalls
Let us examine a tangible example of a remote access IoT firewall in action:
Imagine a smart home system equipped with numerous IoT devices, including smart thermostats, cameras, and door locks. To ensure secure remote access, a next-generation firewall can be implemented. This firewall would incorporate rules to:
- Restrict access solely to authorized IP addresses.
- Encrypt all communication channels using robust protocols like SSL/TLS.
- Monitor and document all incoming and outgoing traffic for thorough analysis.
By deploying such a firewall, homeowners can confidently manage their devices remotely while significantly reducing security risks.
Steps for Configuring IoT Firewalls for Remote Access
Configuring an IoT firewall involves several critical steps:
1. Establish Access Rules
Create comprehensive rules that explicitly define which devices and users are permitted to connect. Employ IP whitelisting to limit access to trusted sources exclusively.
2. Enable Robust Encryption
Encrypt all data transmissions to safeguard sensitive information from potential interception. Utilize strong encryption protocols like AES-256 for maximum security.
3. Maintain Current Rule Sets
Regularly update your firewall rules to address emerging threats and vulnerabilities, ensuring your network remains secure.
By adhering to these steps, you can configure your IoT firewall effectively, enabling secure remote access to your network.
Essential Security Considerations for IoT Firewalls
When deploying an IoT firewall, several security considerations must be addressed:
- Periodic Security Audits: Conduct thorough audits at regular intervals to identify and mitigate potential vulnerabilities.
- Network Segmentation: Isolate IoT devices from critical systems to minimize risks associated with unauthorized access.
- Multi-Factor Authentication (MFA): Implement MFA protocols to authenticate user identities and enhance overall security.
These measures collectively enhance the security of your IoT network, providing robust protection against cyberattacks.
Best Practices for Remote Access IoT Firewalls
Adopting best practices is crucial for ensuring the effectiveness of your remote access IoT firewall:
- Consistent Firmware and Software Updates: Regularly update firmware and software to address vulnerabilities and maintain optimal security.
- Utilization of Monitoring Tools: Deploy intrusion detection systems (IDS) to monitor network activity and identify potential threats.
- Employee Training Programs: Educate staff on cybersecurity best practices to minimize human error and enhance network security.
By implementing these practices, organizations can significantly bolster their IoT firewall defenses and protect their networks against cyber threats.
Top Tools and Software for Managing IoT Firewalls
Several tools and software solutions are available to facilitate the management of IoT firewalls:
Palo Alto Networks
Palo Alto Networks offers advanced NGFW solutions equipped with comprehensive threat prevention capabilities, making it a top choice for securing IoT networks.
Fortinet
Fortinet provides robust firewall management tools tailored for IoT environments, ensuring secure remote access through its cutting-edge solutions.
Cisco ASA
Cisco ASA firewalls deliver scalable solutions for securing IoT networks, supporting a wide array of devices and offering flexible configurations.
These tools streamline the management of IoT firewalls, simplifying the process of maintaining secure remote access for your network.
Real-Life Case Studies: Success Stories
Several organizations have successfully implemented remote access IoT firewalls, achieving remarkable results:
Case Study 1: Smart City Initiative
A city government deployed IoT firewalls to secure its smart traffic management systems. The firewalls ensured that only authorized personnel could access real-time data, thereby enhancing public safety and operational efficiency.
Case Study 2: Healthcare Facility
A hospital implemented IoT firewalls to protect its medical devices from cyber threats. This initiative not only improved patient safety but also ensured compliance with stringent healthcare regulations.
These case studies highlight the practical applications and tangible benefits of remote access IoT firewalls across diverse industries.
The Evolution of Remote Access IoT Firewalls
The future of IoT firewalls holds exciting advancements, particularly in the realms of artificial intelligence (AI) and machine learning (ML). These technologies will empower firewalls to adapt dynamically to evolving threats, providing proactive protection against emerging cyber risks. Furthermore, the integration of zero-trust architecture will elevate the security of IoT networks to unprecedented levels.
As IoT adoption continues to expand, the importance of remote access IoT firewalls in ensuring a secure and interconnected world will only grow more significant.
Final Thoughts
In summary, remote access IoT firewalls play an indispensable role in safeguarding modern networks. By comprehending the benefits, types, and best practices associated with IoT firewalls, organizations can implement effective security measures to protect their IoT devices and networks.
We encourage you to take immediate action by implementing the strategies outlined in this article. Share your thoughts and experiences in the comments section below and explore additional articles on our site for further insights into cybersecurity and IoT innovation.