Enhancing IoT Security With RemoteIoT Platform SSH Keys
In the modern era of interconnected devices, the RemoteIoT platform's SSH keys serve as a cornerstone for securing IoT systems and ensuring reliable communication across networks. As the Internet of Things continues to expand exponentially, the importance of managing secure connections has never been greater. The RemoteIoT platform provides a comprehensive solution for device management, with SSH keys playing a pivotal role in authentication and encryption. These cryptographic keys are essential for safeguarding sensitive data and maintaining the integrity of IoT ecosystems.
This comprehensive guide delves into the significance of RemoteIoT platform SSH keys, their practical applications, and the best practices for their implementation. Whether you're a seasoned developer, a system administrator, or an IoT enthusiast, gaining a deep understanding of SSH keys within the RemoteIoT framework is crucial for building secure and efficient networks. By the end of this article, you'll have a thorough grasp of how these keys function, their advantages, and their role in enhancing IoT security. Let's explore further!
By the conclusion of this guide, you will possess a holistic understanding of RemoteIoT platform SSH keys—how they operate, their benefits, and their contribution to the overall security of IoT networks. Let’s get started!
Read also:What Does Obsidian Kingdom Mean Unveiling The Mysteries Of The Name
Table of Contents
- What Are RemoteIoT Platform SSH Keys?
- The Critical Role of SSH Keys in IoT Security
- A Brief History of RemoteIoT Development
- How RemoteIoT Platform SSH Keys Operate
- Advantages of Leveraging SSH Keys in RemoteIoT
- Steps to Implement SSH Keys in RemoteIoT
- Best Practices for Managing SSH Keys Effectively
- Key Security Considerations for RemoteIoT SSH Keys
- Exploring Alternatives to SSH Keys in IoT
- The Future Landscape of RemoteIoT Platform SSH Keys
What Are RemoteIoT Platform SSH Keys?
RemoteIoT platform SSH keys represent cryptographic key pairs designed to authenticate devices and users within the RemoteIoT ecosystem. SSH (Secure Shell) keys are widely recognized as one of the most secure methods for establishing encrypted connections between devices. In the context of IoT, these keys ensure that only authorized devices can communicate within the network, thereby maintaining a secure environment.
Understanding SSH Key Pairs
An SSH key pair consists of two components: a public key and a private key. The public key is shared with servers or devices, while the private key remains securely stored on the client side. During the authentication process, the public key verifies the identity of the client without exposing sensitive information. This mechanism ensures secure and reliable communication between devices.
Why Select the RemoteIoT Platform?
RemoteIoT platform is tailored specifically for IoT applications, offering features such as device management, data analytics, and secure communication. By integrating SSH keys into its architecture, RemoteIoT guarantees that all interactions within the network are secure and protected from unauthorized access. This makes it an ideal choice for organizations seeking robust IoT solutions.
The Critical Role of SSH Keys in IoT Security
In the realm of IoT, where devices often handle sensitive data and interact with critical systems, security remains a top priority. SSH keys play a vital role in securing IoT networks by providing:
- Strong authentication mechanisms to verify the identity of devices and users.
- End-to-end encryption to protect data during transmission.
- Defense against unauthorized access, ensuring only trusted devices can connect to the network.
Common IoT Security Threats
Without robust security measures, IoT devices are susceptible to various threats, including:
- Brute force attacks, where hackers attempt to guess passwords through repeated trials.
- Man-in-the-middle attacks, where malicious actors intercept and alter communications between devices.
- Data breaches, where sensitive information is exposed to unauthorized entities.
SSH keys significantly reduce these risks by ensuring that only trusted devices and users can access the network, thereby enhancing overall security.
Read also:Will Dan And Serena Get Back Together Exploring The Possibilities
A Brief History of RemoteIoT Development
The development of the RemoteIoT platform commenced in 2015, driven by the increasing demand for secure IoT solutions. Initially designed to address the unique challenges faced by IoT developers, such as scalability and security, the platform has evolved to become a leading choice for organizations worldwide.
Key Milestones
| Year | Milestone |
|---|---|
| 2015 | Initiation of development and official launch of the platform. |
| 2017 | Integration of SSH key functionality to enhance security. |
| 2020 | Expansion of support for large-scale IoT deployments, catering to enterprise-level needs. |
How RemoteIoT Platform SSH Keys Operate
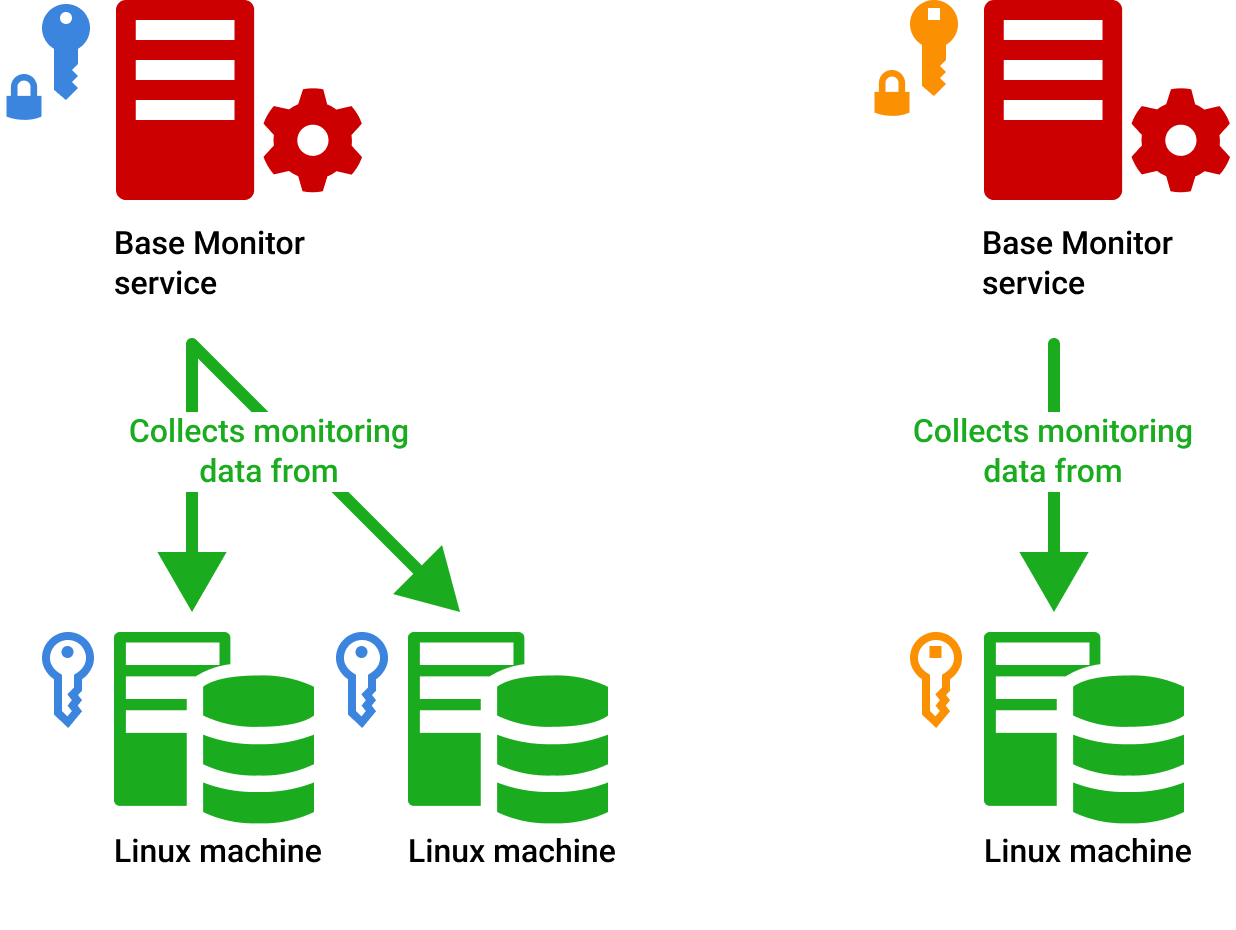
Implementing SSH keys in the RemoteIoT platform involves several well-defined steps:
- Generating a cryptographic key pair, consisting of a public and private key.
- Configuring the public key on the server to enable secure communication.
- Using the private key for authentication during connection initiation.
Key Generation
The process of key generation is fundamental to setting up SSH keys. It creates a unique pair of public and private keys that are mathematically related. The private key must be safeguarded at all times, while the public key can be freely distributed to servers or devices for authentication purposes.
Advantages of Leveraging SSH Keys in RemoteIoT
Utilizing SSH keys in the RemoteIoT platform offers numerous benefits, including:
- Enhanced security through robust encryption, ensuring data integrity and confidentiality.
- Elimination of password-based authentication, reducing the risk of weak or compromised passwords.
- Improved efficiency in managing multiple devices, streamlining operations and reducing administrative overhead.
Comparison with Password-Based Authentication
In contrast to traditional password-based authentication, SSH keys provide a more secure and scalable solution for IoT networks. They eliminate the vulnerabilities associated with weak passwords and reduce the likelihood of brute force attacks, thereby enhancing overall security.
Steps to Implement SSH Keys in RemoteIoT
Implementing SSH keys in the RemoteIoT platform requires meticulous planning and execution. Below are some essential steps to consider:
- Identify devices that require SSH key authentication to ensure comprehensive coverage.
- Generate key pairs for each device, ensuring uniqueness and security.
- Configure the platform to accept public keys, enabling secure communication between devices.
Tools for SSH Key Management
Several tools are available to simplify the process of managing SSH keys, including:
- OpenSSH, a widely used open-source tool for secure communication.
- SSH-Keygen, a utility for generating SSH key pairs efficiently.
- RemoteIoT platform management tools, offering specialized features for managing SSH keys within the ecosystem.
Best Practices for Managing SSH Keys Effectively
To ensure the long-term security of your IoT network, adhere to these best practices for managing SSH keys:
- Regularly rotate keys to minimize the risk of unauthorized access in case of compromise.
- Limit access to private keys, ensuring they are stored securely and accessible only to authorized personnel.
- Monitor key usage diligently and revoke compromised keys promptly to maintain network integrity.
Key Rotation
Key rotation is a critical aspect of maintaining security. By periodically replacing old keys with new ones, you significantly reduce the risk of unauthorized access in the event of a key compromise. This proactive approach ensures the ongoing security of your IoT network.
Key Security Considerations for RemoteIoT SSH Keys
While SSH keys offer robust security, they are not immune to vulnerabilities. Below are some important security considerations to keep in mind:
- Protect private keys with strong passphrases to prevent unauthorized access.
- Use secure protocols for key exchange to ensure data integrity during transmission.
- Regularly audit key usage to detect and address any suspicious activities promptly.
Handling Key Compromise
In the event of a key compromise, swift action is imperative. Revoke the compromised key immediately and generate a new one to prevent unauthorized access to your network. This ensures the continued security of your IoT ecosystem.
Exploring Alternatives to SSH Keys in IoT
While SSH keys remain a popular choice for securing IoT networks, alternative authentication methods are available, such as:
- TLS certificates, offering secure communication through certificate-based authentication.
- Public Key Infrastructure (PKI), providing a framework for managing digital certificates and public keys.
- Token-based authentication, utilizing short-lived tokens to verify identity and access rights.
Choosing the Right Solution
The selection of an authentication method depends on various factors, including network size, device capabilities, and specific security requirements. SSH keys are particularly well-suited for medium to large-scale IoT deployments where security is a top priority. Evaluating these factors carefully ensures the optimal choice for your IoT network.
The Future Landscape of RemoteIoT Platform SSH Keys
As IoT technology continues to advance, the role of SSH keys in securing device communication will only grow in importance. Future developments may include:
- Integration with quantum-resistant cryptography to address emerging security challenges.
- Enhanced key management tools to streamline operations and improve efficiency.
- Improved interoperability with other security protocols, fostering seamless integration within diverse ecosystems.
Preparation for Emerging Threats
Staying ahead of emerging threats requires continuous innovation and adaptation. By investing in secure authentication methods like SSH keys, IoT developers can ensure the long-term viability and security of their networks. Proactive planning and adoption of cutting-edge technologies are essential for safeguarding IoT ecosystems.
Conclusion
In summary, RemoteIoT platform SSH keys are indispensable tools for securing IoT networks. By comprehending their functionality, advantages, and best practices, you can implement them effectively to protect your devices and data. We encourage you to explore the resources mentioned in this article and apply these strategies to your projects. Your feedback and insights in the comments section below are highly valued!
For additional insights into IoT security and related topics, explore our other articles on the site. Together, let's create a safer and more connected world through secure and innovative IoT solutions.